Endpoint detection response capabilities are technologies and processes that continuously monitor endpoints, collect telemetry, and detect behavioral threats while enabling both automated and manual remediation in real time.
Modern EDR goes beyond traditional antivirus, retaining deep endpoint data to support investigations and response across laptops, and remote devices. It tracks process activity, network connections, and user behavior to provide full attack chain visibility.
IBM Security Cost of a Data Breach Report showing a global average breach cost of $4.45 million in 2023, strong endpoint security is critical. Keep reading to see how EDR operates inside a security operations center.
Quick Wins – Endpoint Detection in Action
- Modern endpoint detection and response combines deep telemetry, behavioral analytics, and automated containment to reduce MTTD and MTTR.
- Strong endpoint visibility enables proactive threat hunting aligned with MITRE ATT&CK techniques.
- Response maturity, not just detection, determines real impact on ransomware detection and lateral movement containment.
What Are Endpoint Detection Response Capabilities?
Endpoint detection response capabilities continuously monitor devices, collect telemetry, detect suspicious behavior, and enable immediate containment or remediation. We implement these capabilities starting with network threat detection and extend into host-level visibility. Correlating network activity with endpoint telemetry provides stronger attack chain insight.
As highlighted by CISA
“Endpoint detection and response (EDR) tools combine endpoint and network event data to aid in the detection of malicious activity.” – CISA
Key elements of effective EDR we see in SOCs include:
- Continuous endpoint monitoring across laptops, servers, and cloud workloads
- Real-time detection using machine learning security models
- Endpoint isolation and automated response workflows
- Historical telemetry retention for 30 to 180 days
Modern EDR platforms have four core layers:
- Data collection engines gather endpoint telemetry, process trees, and suspicious process signals
- Analytics engines apply heuristics and anomaly detection
- EDR consoles provide timeline and investigative views for SOC analysts
- Response orchestration enables containment and automated workflow actions
In practice, detection and rule tuning significantly reduce alert fatigue. Properly tuned systems can lower false positives, aligning with industry benchmarks and improving SOC efficiency while maintaining full visibility across all monitored endpoints.
How Does EDR Differ from Traditional Antivirus?

EDR differs from traditional antivirus because it relies on behavioral analytics and long-term telemetry rather than just signature-based detection. We’ve seen in practice that traditional AV cannot provide the same automated response or endpoint forensic capabilities that EDR delivers.
From our experience in large-scale deployments, these capabilities help uncover sophisticated threats that standard AV would miss.
Key distinctions we highlight in our work include:
- Behavioral analytics detect anomalies that signatures cannot
- Extended telemetry retention supports investigations over weeks or months
- Built-in threat hunting tools allow SOC teams to query endpoints efficiently
- Automated response options such as endpoint isolation and process termination
A clear comparison shows the difference:
| Feature | Traditional AV | Endpoint Detection and Response |
| Detection method | Signature-based detection | Behavioral analytics + machine learning security |
| Telemetry retention | Minimal logs | Extended endpoint telemetry storage |
| Threat hunting | Not supported | Built-in query and hunting tools |
| Response | File quarantine | Endpoint isolation, process kill, remediation scripts |
| ATT&CK mapping | Rare | Common practice |
In our experience, comparing AV and EDR directly isn’t fair. Antivirus is a baseline layer, but EDR provides depth, investigative power, and the ability to respond to advanced attack patterns across endpoints.
What Visibility Should Strong EDR Provide?
Strong EDR provides full process lineage, command-line logging, registry monitoring, file integrity tracking, and cross-device correlation. In our experience, comprehensive endpoint visibility is essential for effective threat detection and response.
In practical SOC operations, strong endpoint monitoring includes:
- Complete process tree reconstruction across devices
- Network activity tracking across hosts
- Historical telemetry replay for at least 90 days
- Agent health monitoring with near 100% coverage
We focus on Network Threat Detection first, then pivot into host-level telemetry when suspicious traffic appears. This layered approach lets us validate alerts quickly, reconstruct attack chains, and reduce dwell time significantly.
Signs of weak endpoint visibility are usually obvious:
- Dropped telemetry during peak load
- Lack of cross-host correlation
- Limited historical search capabilities
We’ve investigated incidents where incomplete telemetry added hours to MTTR, increasing business risk. From our perspective, strong EDR visibility is not just about collecting data, it’s about ensuring analysts have a complete, accurate view across endpoints to detect, investigate, and respond to threats effectively.
What Response Actions Define Advanced EDR Platforms?

Advanced EDR platforms provide automated host isolation, process termination, file quarantine, and scripted remediation, all integrated with orchestration tools. From our experience, these capabilities allow SOC teams to respond faster while maintaining control over critical systems.
In practice, a mature response workflow looks like this:
- Security alert triggers in the EDR console
- SOC analyst validates suspected attacker behavior
- Endpoint isolation is initiated where needed
- Remediation scripts are executed automatically
- Post-incident forensic investigation is performed
We rely on automation and orchestration to reduce manual effort, but we always validate containment decisions before acting on mission-critical systems. Balancing speed with business continuity is essential, especially when endpoints support critical operations.
Integration with SIEM platforms, SOAR workflows, and threat intelligence feeds further strengthens response reliability.
In our hands-on experience, combining these integrations with well-defined EDR actions ensures that threats are contained quickly, investigation is thorough, and teams can maintain a proactive security posture without unnecessary disruption to business processes.
How Does EDR Support Proactive Threat Hunting?
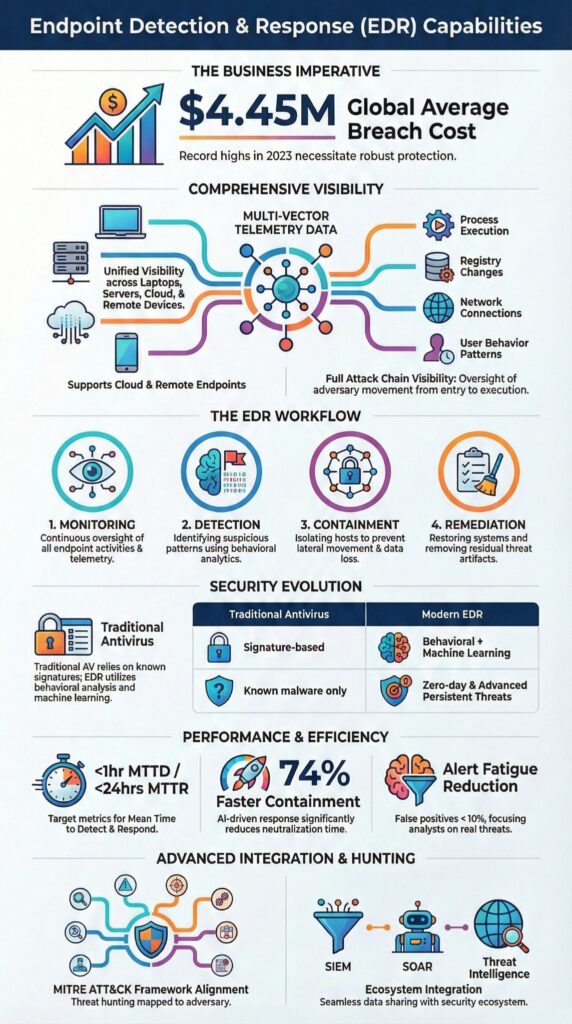
EDR enables proactive threat hunting by giving analysts access to historical endpoint telemetry and the ability to map activity to MITRE ATT&CK techniques.
In our experience, this visibility is critical for detecting subtle attacker behaviors that automated alerts often miss. Many enterprises now report that over 60% run formal threat hunting programs, reflecting the growing importance of this approach.
Proactive hunting in practice often involves:
- Querying PowerShell abuse patterns across endpoints
- Identifying suspicious process anomalies
- Mapping attacker behavior across remote devices
We typically start with indicators from Network Threat Detection and then pivot into host-based queries. This layered method improves confidence before escalating alerts and ensures that investigations are focused and evidence-backed.
From our perspective, threat hunting shifts security teams from reactive alert triage to structured detection engineering.
It allows continuous improvement of detection logic, exposes hidden threats earlier, and strengthens overall security posture. Combining endpoint telemetry with network indicators and our threat models helps organizations anticipate attacker tactics and respond more effectively.
What Metrics Prove EDR Effectiveness?
Credits : CertPro Hub
EDR effectiveness is measured through key operational metrics such as MTTD, MTTR, telemetry coverage, false positive rates, and automated containment performance. In our experience, tracking these metrics provides clear insight into how well endpoint security performs and supports executive decision-making.
Key practices we follow include:
- Monitoring alert triage efficiency weekly
- Tracking isolation success rates across endpoints
- Reviewing telemetry coverage and agent health
- Adjusting detection rules to reduce false positives
- Evaluating automated containment performance trends
We monitor benchmarks like:
| Metric | Target Benchmark |
| Mean Time to Detect (MTTD) | Under 1 hour |
| Mean Time to Respond (MTTR) | Under 24 hours |
| Agent coverage | 95 to 100 percent |
| False positive rate | Below 10 percent |
| Automated containment rate | Increasing year over year |
By combining these metrics with hands-on analysis, we ensure detection tuning aligns with business risk tolerance. This approach allows SOC teams to optimize alert handling, maintain high visibility across endpoints, and keep response workflows effective against emerging threats.
What Limitations and Challenges Come With EDR?
EDR requires careful tuning, skilled analysts, and thoughtful deployment to avoid alert fatigue and incomplete coverage.
In a recent analysis by IBM
“EDR collects data from all endpoints … and can respond automatically to prevent or minimize damage from threats it identifies.” – IBM
In our experience, hybrid environments, spanning cloud workloads, virtual machines, and BYOD models, often create visibility gaps that make comprehensive monitoring difficult. Multi-cloud deployments add complexity, requiring image-based agent embedding and automated lifecycle management to maintain consistent endpoint visibility across environments.
We’ve observed common challenges firsthand, including:
- Alert fatigue in large-scale environments, where excessive notifications can overwhelm SOC teams
- Performance concerns caused by agent-based monitoring on critical hosts
- Incomplete coverage on unmanaged or rogue devices that operate outside standard policies
- Misconfigured automated isolation workflows that may disrupt business operations if triggered improperly
In our threat modeling and risk analysis work, addressing these limitations allows teams to maintain reliable monitoring, reduce operational strain, and strengthen the overall security posture. Strong EDR implementation balances automation, visibility, and analyst oversight to detect threats effectively without compromising system performance.
FAQ
What does endpoint detection and response actually do for my team?
Endpoint detection and response gives your team continuous visibility into activity across laptops, desktops, servers, and remote endpoints.
An EDR solution combines endpoint monitoring, endpoint telemetry, and real-time detection to identify suspicious process detection, malware detection, and ransomware detection. It improves endpoint visibility so the security operations center can reduce dwell time, lower mean time to detect, and improve mean time to respond.
How is an EDR solution different from antivirus vs EDR tools?
Many teams compare antivirus vs EDR or AV vs EDR when evaluating endpoint security.
Traditional antivirus relies mainly on signature-based detection, while endpoint detection and response uses behavioral analytics, heuristic analysis, and machine learning security to detect attacker behavior. An EDR agent supports anomaly detection, zero-day detection, and credential theft detection, which provides stronger endpoint protection than basic antivirus tools.
How does endpoint monitoring improve threat detection and response?
Endpoint monitoring collects detailed endpoint telemetry, including process monitoring, file integrity monitoring, registry monitoring, and network activity monitoring.
This data enables accurate threat detection, lateral movement detection, and privilege escalation detection. With clear attack chain visibility and MITRE ATT&CK mapping, a SOC analyst can perform faster alert triage, reduce mean time to detect, and execute effective incident response.
Can endpoint detection and response reduce false positives and alert fatigue?
Endpoint detection and response can reduce false positives and alert fatigue when teams apply proper detection engineering and detection tuning.
Rule tuning and security analytics help refine detection rules and improve the accuracy of security alerts. Automation and orchestration support automated response actions such as endpoint isolation, process kill, and file quarantine, which strengthen containment workflow and reduce mean time to respond.
Does endpoint detection and response support cloud workloads and remote endpoints?
Modern endpoint detection and response supports cloud workloads, virtual machines, server security, laptop security, desktop security, BYOD security, and mobile endpoint security.
Agent-based security through an EDR agent extends protection to remote endpoints without reducing visibility. With SIEM integration, XDR integration, and threat intelligence integration, organizations improve endpoint compliance, strengthen security posture, and maintain consistent security hygiene across environments.
Strengthen Endpoint Detection Response with Measurable Impact
Effective endpoint detection requires deep telemetry, rapid isolation, automation, and scalable visibility. When combined with Network Threat Detection, teams gain clarity across endpoints, reducing dwell time and exposing hidden threats before they escalate. Modern endpoint security demands structured evaluation and proactive response.
Strengthen your capabilities with Network Threat Detection to map MITRE ATT&CK techniques, orchestrate automated defenses, scale across 10,000+ endpoints, and track measurable metrics, empowering SOCs, CISOs, and analysts to respond faster, improve resilience, and defend confidently against ransomware, zero-days, and advanced attacks.
References
- https://www.cisa.gov/news-events/news/edr-best-practices
- https://www.ibm.com/reports/data-breach


