EDR integration SIEM SOAR platforms connects endpoint detection and response with security information and orchestration tools, creating a unified pipeline that accelerates detection, investigation, and response. In our experience, hybrid environments often leave gaps when endpoint telemetry, network logs, and cloud signals operate in isolation.
IBM reported that the average breach lifecycle in 2023 was 277 days, showing how slow fragmented tools can be. By integrating EDR with SIEM and SOAR, alerts become contextual, workflows automate response actions, and investigations move from fragmented to coordinated. Keep reading to learn how to build a modern, scalable security stack that actually works.
Quick Wins – Smarter EDR & SOC Integration
- Integrated EDR SIEM integration improves centralized correlation and reduces detection blind spots across endpoints, network, and cloud.
- A mature SOAR platform enables automated quarantine, enrichment, and ticketing that reduces breach costs by millions.
- Smart design avoids dashboard redundancy, alert fatigue, and unnecessary ingestion costs while improving SOC modernization.
How Do EDR, SIEM, and SOAR Work Together in a Unified Security Stack?
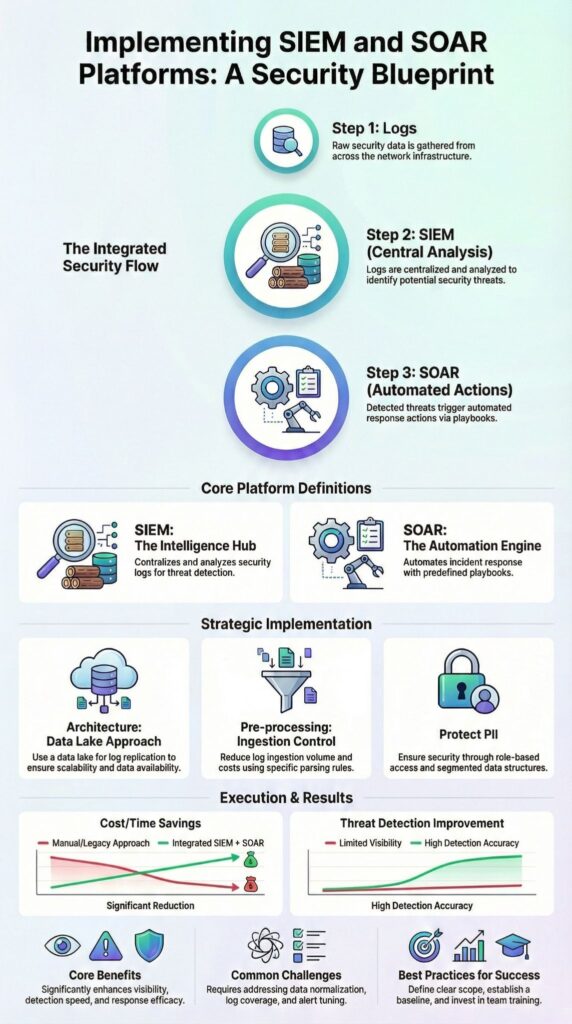
EDR, SIEM, and SOAR combine to form a unified security stack that reduces detection time and enables coordinated response. In our experience, endpoint telemetry from EDR agents, covering process behavior, file integrity, and user activity, forms the foundation of threat detection. Strong Network Threat Detection always starts with this deep visibility layer.
As noted by NIST
“Integrating SIEM and SOAR platforms helps automate and streamline the response to incidents, providing a more efficient defense.” – NIST
SIEM platforms, such as Microsoft Sentinel, then centralize and normalize logs from firewalls, identity systems, and cloud workloads.
SOAR tools, like Splunk SOAR, automate response workflows. In practice, playbooks trigger actions such as automated quarantine, notifications, or endpoint isolation, dramatically reducing manual triage time.
Key telemetry flow steps include:
- EDR agent deployment: collects endpoint visibility and forwards logs to SIEM
- SIEM correlation: normalizes and applies rules engine logic across sources
- SOAR orchestration: executes YAML-based playbooks via RESTful APIs
By combining endpoint visibility, centralized correlation, and automated response, organizations maintain coverage at scale while keeping operational efficiency high, even in high-volume hybrid environments.
Why Forward EDR Logs into SIEM?

Forwarding EDR logs into a SIEM allows centralized correlation across endpoints, network logs, and cloud telemetry, reducing investigative silos. In our experience, endpoint data is critical for understanding breaches, yet native EDR tools alone don’t always provide the full cross-log context needed for fast response.
When EDR logs feed into a SIEM rules engine, analysts can:
- Correlate suspicious hashes with VPN anomalies, firewall denials, or CASB alerts
- Share IOCs across teams and threat intelligence feeds
- Enrich alerts with historical context to identify persistent threats
We’ve also learned that over-ingesting logs can backfire. Excessive telemetry inflates storage costs and creates dashboard redundancy, and SIEM performance can degrade if endpoint data isn’t properly scoped. Effective deployment balances completeness with operational efficiency.
| Capability | Native EDR | SIEM |
| Endpoint process tree | Deep visibility | Limited |
| Cross-log correlation | Limited | Strong |
| IOC historical search | Moderate | Extensive |
In our deployments, SIEM querying complements rather than replaces native EDR tools. By combining endpoint visibility, cross-log correlation, and contextual alerting, teams reduce dwell time, improve detection accuracy, and maintain centralized oversight across hybrid environments.
What Role Does SOAR Play in EDR–SIEM Integration?

SOAR acts as the coordination layer that connects EDR and SIEM through automated playbooks, enabling containment, enrichment, and documentation without relying solely on manual intervention. In our experience, SOAR platforms streamline alert handling and reduce dwell time by orchestrating actions across multiple systems.
In a recent analysis by DoD
“SIEM platforms collect and analyze logs, while SOAR platforms use this data to automate workflows and streamline response processes.” – DoD
A typical workflow we implement includes:
- SIEM rules engine triggers a real-time alert
- SOAR enrichment engine adds context from threat intelligence feeds
- EDR executes automated quarantine or process isolation
- Case management and PagerDuty escalation update teams automatically
Platforms like Cortex XSOAR and Cisco SecureX illustrate how automation layers unify alert correlation and response. We’ve seen containment windows shrink from hours to minutes when STIX/TAXII feeds deliver rapid IOC updates across integrated systems.
We focus on balanced SOAR maturity models that blend machine learning security with analyst review, ensuring rapid response without sacrificing accuracy or context. This combination allows SOC teams to scale operations while maintaining confidence in endpoint, network, and cloud detection coverage.
What Are the Most Common Integration Pitfalls?
Integration between EDR, SIEM, and SOAR can fail when tuning is poor, dashboards overlap, or teams rely too heavily on SIEM for endpoint context. In our experience, overloading the SIEM normalization layer with raw endpoint telemetry creates alert fatigue and slows queries, making response slower than intended.
Dashboard duplication is another frequent issue. We’ve seen environments where multiple NDR and EDR dashboards reported the same malware event differently, confusing SOC teams and complicating escalation workflows.
Key pitfalls we encounter include:
- Alert fatigue from weak correlation rules
- Integration gaps caused by incomplete SOAR connectors
- Misaligned IOC formatting when STIX/TAXII standards are ignored
- Limited endpoint context when relying solely on SIEM for visibility
To mitigate these, we prioritize endpoint telemetry quality first and feed only high-signal events into the SIEM data lake.
Strong Network Threat Detection acts as a safety net, validating activity independently before it reaches the SIEM. This approach improves operational scalability, reduces redundant alerts, and ensures that integration supports rapid, accurate detection and response rather than creating new complexity.
When Should Organizations Integrate EDR, SIEM, and SOAR?
Credits : Harvansh Singh
Organizations benefit from integration when they need cross-domain visibility, automated remediation, compliance alignment, and scalable SOC workflows. In our experience, integration becomes critical once log volumes exceed what teams can triage manually. Without coordination, alerts can pile up, and incident response slows.
Typical scenarios where integration is warranted include:
- SOC maturity reaches intermediate or advanced levels
- Multiple data sources exist across cloud workloads, endpoints, and network monitoring
- Regulatory or audit requirements, such as NIST cybersecurity frameworks or ISO 27001, demand centralized logging and evidence trails
- Continuous monitoring and automated remediation are part of business risk management
We also see integration supporting cyber insurance compliance and SOC 2 Type II reporting. When telemetry, correlation, and orchestration are aligned, evidence generation becomes structured rather than ad hoc.
By combining EDR, SIEM, and SOAR, organizations gain not only faster detection and response but also confidence that controls, workflows, and reporting meet both operational and regulatory expectations. Integration turns fragmented visibility into a unified, proactive security posture.
FAQ
How does EDR SIEM integration improve threat detection and response?
EDR SIEM integration connects endpoint detection response with security information event management to strengthen the threat detection pipeline. Endpoint telemetry and EDR logs forwarding flow into log aggregation, where SIEM normalization prepares data for centralized correlation.
This process improves alert correlation, enables accurate SIEM querying, and supports real-time alerting. As a result, the incident response workflow becomes faster, more structured, and less prone to alert fatigue within the security operations center.
What role does a SOAR platform play in automated incident response?
A SOAR platform applies security orchestration automation response to coordinate actions across the cybersecurity stack. It uses SOAR connectors to receive alerts from the SIEM rules engine and endpoint detection response systems.
The SOAR orchestration engine then executes playbook automation, including automated quarantine and malware response automation. When required, it supports human-in-the-loop approval to maintain control while reducing manual effort and improving consistency.
How can endpoint telemetry and log aggregation reduce false positives?
Endpoint telemetry combined with network logs inside a unified security dashboard provides stronger endpoint visibility and clearer context. Through SIEM querying, behavioral analytics, and UEBA integration, security teams perform precise anomaly detection and structured false positive tuning.
Centralized correlation across the cybersecurity stack connects related signals and filters noise. This approach improves ransomware detection accuracy and strengthens process behavior monitoring across monitored endpoints.
What integration challenges exist in a hybrid cybersecurity stack?
Integration complexity often arises when combining native EDR tools, SIEM normalization processes, NDR integration, and cloud workload protection in a hybrid environment. Hybrid environment monitoring requires stable API-based integration and a well-designed log ingestion pipeline.
Scalability challenges, dashboard redundancy, and unplanned security tool stacking can reduce efficiency and increase costs. Proper data lake architecture planning and cost optimization strategies are necessary to maintain long-term performance.
How does automation support compliance and reporting requirements?
Automation strengthens compliance reporting aligned with NIST cybersecurity guidance, ISO 27001 controls, GDPR data protection, and SOC 2 Type II requirements. Through structured playbook automation and consistent SIEM querying, teams document each step of the incident response workflow.
Threat intelligence enrichment, IOC sharing through the STIX TAXII protocol, and post-incident IOC batching create clear audit trails. This structured process supports regulatory frameworks, cyber insurance compliance, and continuous monitoring obligations.
Strengthen SOC Operations with Integrated EDR, SIEM, and SOAR
EDR integration with SIEM and SOAR transforms endpoints into a centralized, intelligent detection hub. Deep telemetry, correlation, and automation speed incident response, reduce alert fatigue, and provide clearer operational insight across hybrid environments.
Teams aligning endpoint detection, SIEM analytics, and SOAR orchestration achieve proactive resilience, scalable workflows, and compliance-ready telemetry. Strengthen your SOC today by scheduling a security architecture assessment with Network Threat Detection, turning reactive firefighting into measurable, confident, and continuous defense.
References
- https://www.nist.gov/cyberframework
- https://media.defense.gov/2025/May/27/2003722066/-1/-1/0/Implementing-SIEM-and-SOAR-platforms-Practitioner-guidance.PDF