Using EDR for incident response means converting raw endpoint telemetry into actionable workflows that support detection, triage, containment, eradication, and recovery across all affected systems.
We see firsthand that collecting data alone is not enough, teams must define structured processes and automation to make endpoint insights operational. Reviewing at least 13 workflow and automation criteria before relying on an EDR platform in live incidents.
In practice, gaps appear when telemetry isn’t correlated with network activity or when response playbooks aren’t validated. Keep reading to learn how to operationalize EDR effectively while integrating Network Threat Detection for stronger outcomes.
Quick Wins – EDR + Network Threat Detection
- EDR works best when paired with Network Threat Detection, giving both host-level and network-level visibility before containment begins.
- A structured incident response workflow reduces EDR alert fatigue and improves mean time to detect and respond.
- Automation helps, but disciplined scoping and investigation prevent premature EDR containment mistakes.
What Does EDR Actually Do in Incident Response?
EDR collects endpoint telemetry and applies behavioral analytics to detect threats, reconstruct execution chains, and enable fast response actions. In practice, it turns raw endpoint signals into structured insights that drive investigation and containment.
As highlighted by CISA
“…EDR alerts were not continuously reviewed, and some public‑facing systems lacked endpoint protection.” – Cybersecurity and Infrastructure Security Agency (CISA)
Unlike traditional antivirus, modern EDR emphasizes process tree analysis, PowerShell monitoring, and command-line tracking. This depth allows our teams to reconstruct timelines and map activity to MITRE ATT&CK techniques, improving detection of subtle adversary behaviors.
From our experience, high-severity alerts involve misuse of legitimate tools like PowerShell or WMI. Behavioral analytics uncover these patterns faster than static signatures.
Key capabilities include:
- Real-time alerts on suspicious endpoint behaviors
- Deep forensics across disk, registry, and process activity
- Remote actions such as endpoint isolation and process termination
- Integration with SIEM or XDR platforms for cross-domain correlation
We always start with network telemetry. When Network Threat Detection identifies unusual command and control activity first, EDR investigation becomes more focused, allowing faster remediation and stronger operational confidence.
How Does EDR Support Each Phase of the Incident Response Lifecycle?

EDR supports detection, scoping, containment, eradication, and recovery by combining endpoint visibility with automation and investigative controls. In practice, it turns raw telemetry into actionable steps across the SOC workflow.
Research from ResearchGate
“…real‑time monitoring of endpoints, behavioural analysis, and incident response…” – ResearchGate
Behavioral alerts, credential access monitoring, and privilege escalation detection identify suspicious activity. Analysts pivot into host and user context to validate true positives versus false positives. In high-volume environments, this process reduces alert fatigue and accelerates decision-making.
EDR hunting allows fleet-wide searches for indicators of compromise. Teams map EDR telemetry to MITRE ATT&CK techniques, enrich with IOCs, and correlate with SIEM logs. We often start with Network Threat Detection to confirm suspicious traffic, narrowing endpoint investigations quickly.
Remote controls enable isolation, process termination, and artifact removal. Key actions include:
- EDR endpoint isolation
- EDR remediation scripts
- EDR quarantine policies
- EDR policy enforcement
Decisions to isolate or remediate follow validated scoping to preserve forensic integrity. By integrating EDR across the incident response lifecycle, teams gain structured workflows that reduce dwell time, improve accuracy, and maintain operational confidence without over-reliance on manual intervention.
What Are the Most Common EDR Pitfalls in Incident Response?

Even the best EDR tools can create risks if misused. In our experience, the biggest challenges come from automation overreach, alert fatigue, premature eradication, and assuming EDR is a complete security layer on its own.
| Pitfall | Risk | Recommended Approach |
| Poor baseline calibration | High false positives, alert fatigue | Refine baselines and tune detection rules |
| Automation overreach | Loss of forensic artifacts, incomplete investigation | Validate containment timing and manual review |
| Weak alert severity prioritization | Analysts overwhelmed by noise | Apply severity tiers and feedback loops |
| Missing correlation across endpoints | Missed lateral movement and context | Integrate network, identity, and cloud telemetry |
High-volume environments generate thousands of daily alerts. Without proper tuning, detection engineering, and analyst feedback loops, noise overwhelms the SOC. We prioritize refining baselines and EDR correlation rules first, which improves triage efficiency and reduces false positives.
Common Contributors
- Poor EDR baseline calibration
- Overly broad or misconfigured custom rules
- Weak alert severity prioritization
- Missing correlation across endpoints
We’ve learned that disciplined EDR operations, combining tuning, analyst oversight, and layered visibility including Network Threat Detection, restores signal from noise and ensures incident response remains both fast and accurate.
How Should SOC Teams Operationalize EDR for Repeatable Results?
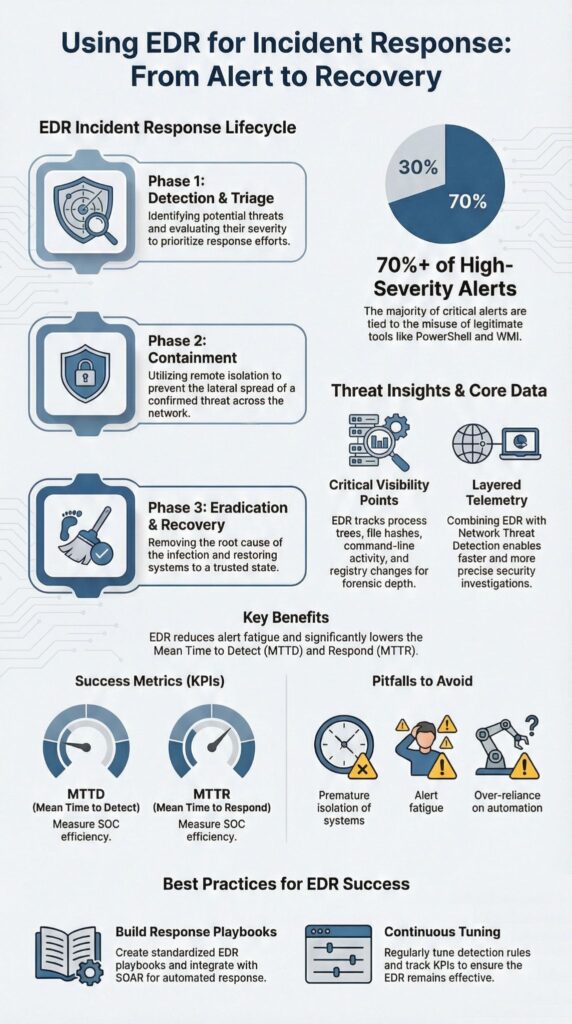
Operationalizing EDR requires clear playbooks, careful automation, continuous tuning, and layered telemetry integration. In our experience, the most effective approach follows three layers: Network first, Endpoint second, and Automation third. Two principles guide our work: visibility before action, and context before containment.
Key steps include:
- Build an EDR playbook for each alert type
- Define thresholds for containment versus monitoring
- Enable SOAR integration for high-confidence automation
- Track KPIs like mean time to detect, respond, and contain
Strong detection engineering is critical. We maintain:
- Clear, version-controlled detection logic
- Continuous mapping and normalization of EDR schemas
- Monitoring for configuration and policy drift
Integrating broader telemetry ensures SOC teams see the full picture. Endpoint data alone misses lateral movement, identity anomalies, and cloud workload activity. By correlating EDR telemetry with Network Threat Detection, identity logs, and cloud signals, we create an XDR layer that reduces dwell time and strengthens detection confidence.
In practice, mature SOCs report up to 70% faster investigations once EDR automation and detection engineering are optimized. The combination of disciplined playbooks, layered telemetry, and continuous tuning makes EDR a repeatable, reliable driver of security outcomes.
How Do Practitioners Actually Use EDR in Real Environments?
Credits : Microsoft Security
In practice, we treat EDR as a structured investigation engine rather than just an alert dashboard. Alerts are the starting point, but actionable response depends on context and investigation. A typical workflow looks like this:
- Suspicious PowerShell execution triggers an EDR alert
- Analysts trace execution chains and parent process lineage
- Fleet-wide searches identify similar command-line patterns
- Outbound connections are validated against network logs
- Decisions are made for isolation, monitoring, or deeper forensics
For servers and cloud workloads, we balance performance with visibility. Lightweight agents and server protection must avoid slowing operations while still providing full telemetry. EDR live response, remote shell access, and controlled disk artifact collection are essential tools in our toolkit.
Operational realities include:
- Managing agent deployment across thousands of endpoints
- Monitoring upgrades, versioning, and patch compliance
- Evaluating vendors for detection depth and response features
- Minimizing performance impact while maximizing telemetry coverage
Ultimately, EDR is most effective when combined with disciplined workflow, structured automation, and layered telemetry. In our experience, the teams that integrate network data, endpoint logs, and proactive hunting consistently uncover threats faster and reduce dwell time across complex hybrid environments.
FAQ
How does endpoint detection and response improve the incident response workflow?
Endpoint detection and response improves the incident response workflow by providing continuous visibility into EDR telemetry, EDR alerts, and host-level context across all endpoints.
It supports structured EDR triage, EDR containment, EDR eradication, and EDR recovery. With accurate EDR logging and well-defined EDR correlation rules, security teams reduce confusion and significantly lower mean time to detect and mean time to respond.
How can a SOC analyst EDR setup reduce alert fatigue and false positives?
A well-configured SOC analyst EDR environment reduces EDR alert fatigue by applying EDR baselining, EDR rule tuning, and clearly defined EDR detection logic.
Teams refine EDR custom rules and strengthen EDR behavioral analytics to minimize EDR false positives. An active EDR analyst feedback loop ensures alerts are reviewed, improved, and prioritized based on real incident data and measurable outcomes.
What role does EDR telemetry play in investigation and threat hunting?
EDR telemetry plays a central role in EDR investigation and EDR hunting by collecting detailed EDR process tree analysis, EDR execution chains, and EDR timeline reconstruction data.
Analysts enrich findings through EDR IOC enrichment, EDR threat intelligence, and EDR TTP mapping. This structured approach supports reliable lateral movement detection, credential access detection, and deeper understanding of attacker behavior.
How do security teams use EDR for containment and remediation?
Security teams use EDR endpoint isolation and EDR auto containment to immediately restrict malicious activity on affected systems. During EDR containment, analysts conduct EDR live response actions or use an EDR remote shell to assess impact.
EDR remediation scripts and quarantine policies support complete eradication. Strong EDR policy enforcement ensures systems are secured before recovery begins.
How should organizations measure EDR effectiveness and operational performance?
Organizations should measure EDR effectiveness using defined metrics and KPIs such as mean time to detect, mean time to respond, and mean time to contain.
They should evaluate incident scoping accuracy, automation workflows, and detection engineering maturity. Regular reviews of SIEM integration and SOAR integration also confirm that the EDR program supports consistent operational improvement.
Transform EDR into a Repeatable Incident Response Engine
Effective incident response goes beyond deploying agents, it requires structured workflows, layered telemetry, and context-driven automation. When endpoint data aligns with SIEM, SOAR, and network insights, teams uncover threats faster, reduce dwell time, and preserve evidence integrity.
Treat EDR as an investigative engine, not just a reactive tool. Strengthen your incident response by aligning telemetry and workflows with Network Threat Detection, enabling measurable MTTR improvements, high-confidence alerts, and confident containment.
Visual attack simulations, CVE mapping, and continuous intelligence help SOCs, CISOs, and analysts proactively defend networks and close blind spots before attackers exploit them.
References
- https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-266a
- https://www.researchgate.net/publication/383015439_Evolution_of_Endpoint_Detection_and_Response_EDR_in_Cyber_Security_A_Comprehensive_Review