EDR vs traditional antivirus AV differs in scope and capability. EDR goes beyond signature-based blocking by continuously monitoring endpoints for behavioral anomalies, suspicious process activity, and lateral movement, enabling real-time detection and response.
Traditional antivirus AV still prevents known malware effectively, but advanced threats like ransomware, fileless attacks, and living-off-the-land techniques often bypass static signatures.
We’ve seen organizations relying solely on AV experience blind spots, slower incident response, and incomplete threat visibility, especially across hybrid and cloud networks. Understanding the differences helps teams align security tools with operational maturity and risk tolerance. Keep reading to explore which approach fits your environment.
Quick Wins – EDR vs Traditional AV
- EDR (Endpoint Detection and Response) focuses on real time behavioral monitoring and threat hunting, while traditional AV focuses on known malware prevention.
- Traditional AV is lightweight and cost effective, but EDR provides deeper telemetry, forensic visibility, and active response.
- For modern ransomware and fileless attacks, combining Network Threat Detection with EDR strengthens layered defense.
What Is the Core Difference Between EDR and Traditional Antivirus?
Traditional antivirus (AV) protects endpoints by blocking known malware using signature databases. When a file matches a known hash, it’s quarantined or blocked. This approach has been effective for decades against commodity threats, and it still provides a solid baseline for malware prevention.
As highlighted by CMS Information Security and Privacy Program
“This approach allows traditional endpoint protection to handle ‘blocking what we know is bad,’ while EDR/XDR takes on ‘assuming something got through.’” – CMS Information Security
EDR, on the other hand, assumes breaches will happen. It monitors endpoint behavior continuously, tracking process execution, memory injection, registry changes, and network activity.
In our experience, solutions like CrowdStrike and SentinelOne detect suspicious behaviors that traditional AV misses, including zero-day attacks and fileless techniques that blend into normal system activity.
The distinction becomes practical in real-world deployments:
- Traditional AV blocks known threats before execution.
- EDR flags abnormal behavior during or after execution.
- EDR provides investigation tools like timeline reconstruction and process lineage analysis.
We’ve seen firsthand how EDR uncovered credential dumping and lateral movement attempts that AV never touched.
How Do Detection Methods Compare in Practice?

Traditional AV relies on signature databases and basic heuristics, scanning files at rest or during execution and comparing them to known malware hashes. This works for commodity malware, but it misses novel or fileless attacks.
EDR approaches detection differently. It continuously collects telemetry from endpoints, including:
- Parent–child process trees
- Memory behavior and in-memory execution patterns
- Command-line arguments and scripting activity
- Outbound network connections
This data feeds behavioral analytics and AI-driven anomaly detection. In our experience, EDR has flagged legitimate utilities like certutil misused during red team exercises, something traditional AV completely missed.
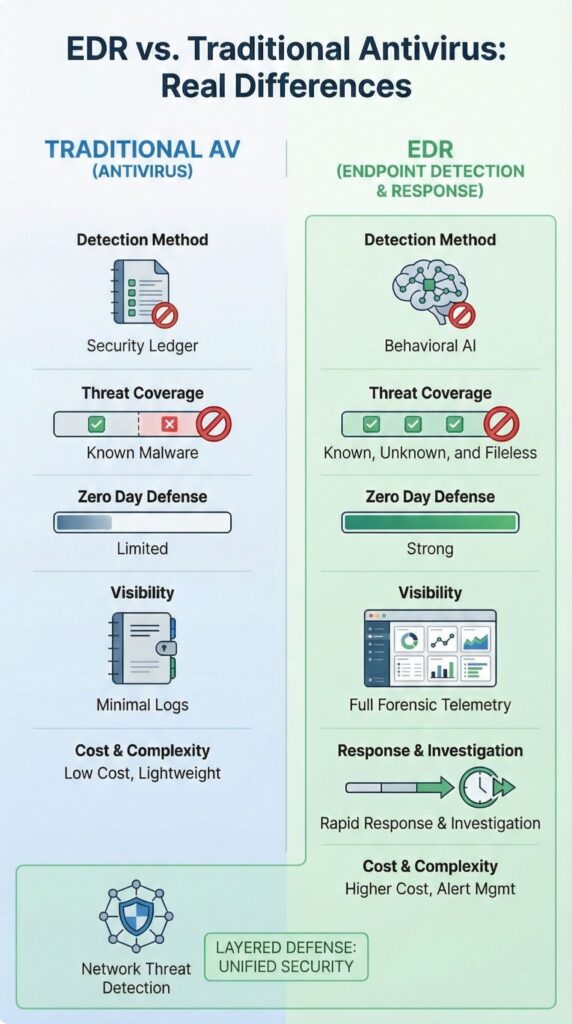
Here’s a practical comparison:
| Aspect | Traditional AV | EDR |
| Detection Method | Signature-based scanning | Behavioral AI & anomaly detection |
| Threat Coverage | Known malware | Known + unknown + fileless |
| Zero Day Defense | Limited | Strong via behavior analysis |
| Visibility | Minimal logs | Full forensic telemetry |
In operational environments, AV blocks threats quietly. We rely on EDR to correlate endpoint activity, provide forensic evidence, and give our teams actionable insights. The combination of behavioral detection and layered telemetry ensures investigations are data-driven, not just reactive.
What Are the Strengths and Limitations of Each Approach?

Traditional AV is reliable for baseline endpoint hygiene. We often see small organizations under 50 endpoints rely on it because it’s lightweight, easy to deploy, and automatically quarantines known threats with minimal system impact. However, AV struggles with obfuscated ransomware or novel malware, static signatures alone can’t keep up with advanced attacks.
We use EDR to trace lateral movement, isolate affected hosts, and reconstruct timelines during incidents.
It generates detailed telemetry that supports root cause analysis and allows our teams to hunt threats proactively rather than just react. That said, EDR requires trained analysts to tune alerts and manage noise; misconfigured rules can create alert fatigue.
Key strengths and limitations include:
Traditional AV Strengths
- Cost-effective deployment
- Low system overhead
- Effective against known malware
Traditional AV Limitations
- Weak against zero-day exploits
- Limited forensic visibility
- Minimal investigation capability
EDR Strengths
- Behavioral detection of advanced threats
- Remote endpoint isolation and remediation
- Timeline reconstruction for investigation
EDR Limitations
- Alert fatigue risk if mismanaged
- Requires skilled analysts
- Higher operational cost
In practice, combining AV for baseline protection and EDR for investigative depth gives organizations both efficiency and actionable visibility.
Can EDR Replace Traditional Antivirus?
In many enterprise environments, modern EDR platforms now include next-generation AV capabilities, and in some cases, they can replace standalone antivirus entirely.
Insights from Federal Bureau of Investigation
“…obfuscation methods allow LummaC2 actors to bypass standard cybersecurity measures, such as Endpoint Detection and Response (EDR) solutions or antivirus programs…” – Federal Bureau of Investigation
We’ve seen organizations successfully consolidate endpoint protection when EDR provides both behavioral monitoring and signature-based scanning. This reduces tool sprawl, simplifies policy enforcement, and improves operational visibility.
That said, replacement doesn’t automatically mean simplification. EDR generates far more telemetry than traditional AV, and without structured workflows and disciplined alert triage, alert overload quickly becomes a real problem.
In our deployments, we always layer Network Threat Detection first. By monitoring network traffic and detecting anomalies, we often spot lateral movement or command-and-control activity before endpoint alerts fire.
Layered defense often looks like this:
- Network Threat Detection for traffic-level anomaly monitoring
- EDR platforms for endpoint behavior analysis and automated response
- Managed detection or SOC support for capacity gaps
Effective coverage comes from aligning endpoint and network visibility, tuning detection rules, and implementing structured response playbooks.
When Should You Choose AV, EDR, or Both?
Credits : IBM Technology
Choosing between traditional AV, EDR, or a combination depends on risk exposure, operational scale, and compliance requirements.
We often see small offices with minimal IT staff and limited regulatory demands successfully rely on AV for baseline protection. Signature-based blocking handles common malware efficiently, especially when devices are fewer than 50 and data sensitivity is low.
For larger enterprises, hybrid environments, or cloud workloads, EDR becomes essential. Its behavioral analytics detect suspicious credential use, privilege escalation, and lateral movement that traditional AV cannot see. In our experience, EDR adds real investigative depth and allows teams to respond quickly to complex attacks.
Practical guidance looks like this:
- Choose Traditional AV if: Limited IT resources, budget constraints, low risk exposure
- Choose EDR if: Enterprise scale operations, hybrid or cloud deployments, regulatory compliance requirements
- Choose Both if: High ransomware risk, sensitive data environments, need for layered detection and visibility
We always begin with Network Threat Detection to establish traffic intelligence across the environment. From there, layering EDR provides endpoint context without creating unnecessary complexity. This combination reduces blind spots, strengthens detection fidelity, and ensures response actions are both timely and informed.
FAQ
What is the main difference between EDR and traditional antivirus?
The main difference between EDR and traditional antivirus lies in visibility and response. Traditional antivirus relies mostly on signature based detection and AV definition files.
Endpoint detection response adds behavioral analysis security, real time threat detection, continuous monitoring EDR, threat hunting capabilities, and post breach analysis. These features allow organizations to detect and respond to advanced persistent threats and malware beyond standard malware prevention strategies.
Can endpoint detection response effectively prevent zero-day attacks?
Yes. Endpoint detection response provides zero day threat protection by using EDR machine learning, behavior based blocking, and continuous monitoring.
Unlike traditional antivirus, which depends on AV signature updates or antivirus heuristic scanning, EDR detects suspicious activity patterns. This allows it to identify memory based malware, fileless attack detection, and other advanced persistent threats that often bypass legacy antivirus limitations.
Is next generation antivirus sufficient without implementing EDR platforms?
Next generation antivirus improves on traditional antivirus software evolution with features like behavioral analytics AV and antivirus cloud sandboxing.
However, EDR platforms enhance protection by providing EDR telemetry data, lateral movement detection, privilege escalation detection, and detailed endpoint security solutions. Organizations facing complex threat actor TTPs or supply chain attack risks benefit from combining next gen AV features with EPP vs EDR capabilities for stronger coverage.
How do EDR deployment costs compare to traditional antivirus solutions?
EDR deployment costs are generally higher than traditional antivirus because EDR offers continuous monitoring, EDR SOC integration, and incident response automation.
Cloud based EDR and managed EDR services can help reduce internal workload. In contrast, traditional antivirus relies on lightweight agents and AV performance impact is lower. However, EDR delivers more comprehensive protection, which improves long-term EDR vs antivirus ROI.
Can endpoint monitoring tools reduce ransomware and breach impact?
Endpoint monitoring tools within EDR significantly reduce ransomware and breach impact. They provide ransomware protection EDR, exploit prevention EDR, endpoint isolation EDR, EDR alert triage, playbook automation, and EDR forensics.
While antivirus real time scanning and antivirus scheduled scans help block known threats, they often fail against AV bypass techniques, AV bypass evasion, and sophisticated attacks that EDR is designed to detect.
The Future of Endpoint Security: EDR Beyond Traditional AV
As attacks evolve, static antivirus cannot see fileless malware, memory exploits, or encrypted command-and-control channels. EDR, combined with Network Threat Detection, turns fragmented signals into unified, continuous detection, reducing blind spots and accelerating response.
Prevention alone is no longer enough. Teams that align endpoint, network, and cloud telemetry gain measurable resilience, faster detection, and confident response to advanced threats. Strengthen your security posture today by exploring integrated EDR and Network Threat Detection, turning reactive defense into a proactive, behavior-driven strategy.
References
- https://security.cms.gov/posts/core-cyber-essentials-resilient-digital-environment
- https://www.fbi.gov/file-repository/cyber-alerts/threat-actors-deploy-lummac2-malware-to-exfiltrate-sensitive-data-from-organizations-052125.pdf


