Endpoint security is for your devices. Network security is for the connections between them. It’s a fact: About 70% of breaches involve compromised endpoints (IBM 2023).
In today’s setup, with remote work everywhere, one infected laptop can let an attacker roam your entire network. We know because we’ve responded to these incidents. You need to watch both the devices and the network traffic. The warning signs usually show up in the network first.
To build a real defense, you have to understand both parts. Let’s break down how they work.
Endpoint Security vs Network Security: Key Differences at a Glance
Understanding how these two security layers work together helps explain why modern organisations rely on both.
- Endpoint security protects individual devices such as laptops, servers, and mobile systems using tools like Endpoint Detection and Response (EDR) and Next-Generation Antivirus.
- Network security protects traffic and infrastructure, using technologies like Intrusion Detection and Prevention Systems, Virtual Private Networks, and Network Access Control.
- A layered model combining device visibility and Network Threat Detection improves detection speed and reduces breach impact.
What Is the Difference Between Endpoint Security and Network Security?
Endpoint security protects your devices. Network security protects the connections between them.
We install endpoint security software directly on laptops, desktops, and phones. It watches what happens on the device itself, looking for malicious software and unusual behavior. Network security is different. It uses tools like intrusion detection systems and web gateways to inspect the traffic flowing across your routers and switches.
Insights from the NDSS Symposium indicate
“While endpoint security is important, Stawowski notes that network safeguards provide the first line of defense for IT system resources against attacks, both internal and external. … This has driven research into ways of securing the home holistically through network security to complement endpoint security.” – NDSS Symposium
We see this split play out in real incidents. In one case we reviewed, unusual network traffic between servers was the first clue that something was wrong. The endpoint alerts didn’t go off until later. Spotting the problem on the network gave the team a head start.
Here’s a simple breakdown:
- Endpoint security watches files, processes, and activity on the device’s operating system. It catches things like ransomware.
- Network security watches traffic patterns and connections. It catches things like DDoS attacks or strange communication.
Research from Zscaler shows that using both layers helps teams find security incidents faster. You see the threat from two different angles.
Quick Snapshot: Key Insights on Endpoint vs Network Security
Credits: Proxy Digi
Endpoint security looks inside devices. Network security looks at the traffic between them.
Attackers move. They might break into a laptop, then use it to move across the network. That’s why you need both types of security.
Endpoint tools, like Endpoint Detection and Response (EDR), analyze what apps and files are doing on a user’s device. Network tools set up security controls at the perimeter, watching the patterns of incoming and outgoing traffic.
A few key points from current setups:
- Common endpoint tools are EDR, Next-Gen Antivirus, and endpoint protection platforms.
- Common network tools are Intrusion Prevention Systems (IPS), VPNs, and Network Access Control (NAC).
- Advanced network monitoring now uses behavioral analytics and outside threat intelligence.
- With cloud and office networks mixed together, you need visibility across all of it.
Gartner noted that over 75% of organizations had adopted EDR by 2023. Everyone wants better visibility on their devices. But in our work, we still find that network monitoring often catches the early warning signs before an endpoint tool officially raises an alarm.
What Is Endpoint Security and How Does It Protect Devices?
Endpoint security uses small software agents to protect laptops, servers, and even smart devices. These agents monitor device activity and can block threats right there.
The tools run on the device itself, analyzing every file that executes and every action a user takes. Most companies we work with use a combined endpoint protection platform. It bundles next-gen antivirus, EDR for deeper investigation, and automated patch management into one system.
Security teams often rely on deeper telemetry from endpoint detection response capabilities to understand how threats behave once they land on a device.
The numbers show why this matters. IBM Security reported that 70% of successful cyberattacks in 2023 started with a compromised endpoint. Attackers go after devices because it’s often the easiest way in.
The main technologies in endpoint security are:
- Antivirus and Next-Gen Antivirus: The basic guard against known malware.
- Endpoint Detection and Response (EDR): Looks for subtle, suspicious behavior over time.
- Data Encryption: Scrambles data so it’s useless if a device is lost or stolen.
- Multi-factor Authentication (MFA): Adds an extra step to prove a user’s identity.
- Remote Wipe: Allows us to securely erase a compromised device from afar.
These tools use machine learning to spot oddities, like a program trying to access files it shouldn’t. This is especially critical for remote work. When employees use home Wi-Fi or coffee shop networks, their devices are more exposed. Strong endpoint protection is the last line of defense if someone manages to exploit a flaw in the operating system or an app.
What Is Network Security, and How Does It Protect Your Systems?
Network security protects the data moving across your wires and airwaves. It inspects traffic, controls who gets in, and blocks malicious activity before it ever touches a device.
The technology works at key points in your corporate network, your firewalls, switches, and gateways. It looks at traffic patterns, stops unauthorized access, and spots strange conversations between systems.
In the setups we manage, network threat detection is often the first warning sign. We’ll see unusual communication between servers long before any malware is found on an endpoint device. That head start is critical.
Cloudflare reports DDoS attacks rising significantly YoY (e.g., 50%+ in recent years).
The main tools for network security are:
- Intrusion Detection and Prevention Systems (IDPS)
- Virtual Private Networks (VPN)
- Network Access Control (NAC)
- Security Web Gateway
- Unified Threat Management (UTM)
Today, these protections must extend to the cloud. We use tools like Cloud Access Security Brokers (CASB) and Secure Access Service Edge (SASE) for that. For companies with a mix of their own servers and cloud services, monitoring also has to cover the traffic between those two worlds, like connections to workloads in the AWS Marketplace.
How Do Endpoint Security and Network Security Compare?
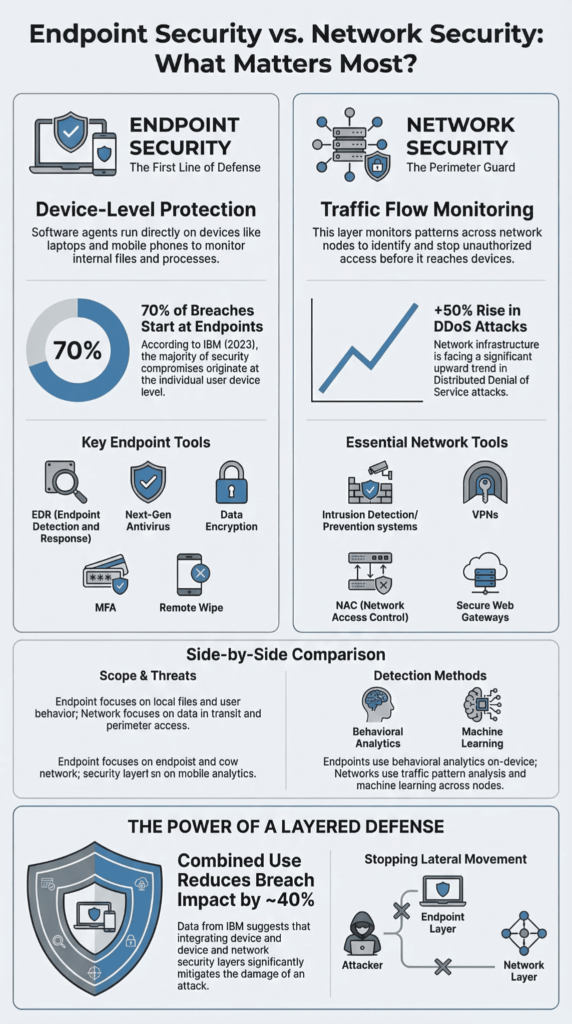
Endpoint security watches what happens on a device. Network security watches the traffic between devices. They are two different, but perfectly matched, layers of defense.
Endpoint tools look at local activity inside your computers and phones. Network tools look at the connections and data flowing between them. When you use both, you can see the whole picture: what’s happening on a device and how it’s talking to the network.
Many investigations start by reviewing EDR data sources like process execution and suspicious files, which reveal how malware actually behaves on a compromised machine.
Here’s a side-by-side look:
| Aspect | Endpoint Security | Network Security |
| Scope | Individual devices | The entire corporate network |
| Threat focus | Malware, ransomware | DDoS attacks, unauthorized access |
| Technologies | EDR, antivirus, encryption | Intrusion Detection Systems, VPN |
| Detection method | Behavioral analysis | Traffic monitoring |
| Deployment | Software agents on devices | Centralized infrastructure tools |
IBM Security found that organizations using layered security like this reduce the impact of a breach by about 40%.
From our experience, the timeline is telling. Suspicious traffic patterns on the network usually show up first. The endpoint detection alert comes later. Spotting the problem on the network lets a team contain a threat before it spreads from device to device.
Why Do You Need Both Endpoint and Network Security?

Alt text: Office team working under a protective dome, illustrating endpoint security vs network security in action
You need both because they stop attacks at different stages. Network security blocks threats from getting in. Endpoint security finds and stops malicious activity that’s already running inside.
Think of network security as a filter at the border. It checks all incoming and outgoing traffic. Endpoint security is the guard inside the building, watching what each person and machine is actually doing.
As highlighted by LevelBlue
“Endpoint protection secures individual devices, while network security safeguards the entire network. … Combining network protection with endpoint protection enhances defenses against cyber threats. Endpoint protection platforms help prevent vulnerabilities introduced by endpoint devices, while centralized management tools streamline data sharing between the network and endpoint security.” – LevelBlue
This layered thinking matches modern guidance, like the NIST Zero Trust model, which says you should verify both the device and its connection.
Using both controls together helps you:
- Find security incidents faster.
- Coordinate your response better.
- Shrink the overall attack surface.
- Spot lateral movement when an attacker jumps from one system to another.
In practice, these two layers talk to each other through security platforms like SIEM systems or automated threat containment tools. The data from both sides makes each one smarter.
The benefit is real. The 2024 IBM Cost of a Data Breach Report found that companies using a Zero Trust approach, which relies on this layered defense, spent roughly 20% less to resolve a breach.
What Are the Pros and Cons of Each Approach?
Endpoint security gives you a deep look inside a device. Network security gives you a broad view of all the traffic moving around. They’re good at different things.
Endpoint security is best at finding threats that are already running on a laptop or server. Network security is best at spotting strange conversations happening between systems on your network.
Here’s a breakdown of what each one does well, and where it falls short.
Endpoint Security Strengths
- It watches everything a device does.
- It can detect malicious software as it runs.
- It sees how applications behave.
- It protects devices no matter where they are, at home, in an office, or on the road.
Endpoint Security Limitations
- You have to install a software agent on every single device.
- Managing thousands of these agents gets complex.
- It can’t see what’s inside encrypted network traffic.
Network Security Strengths
- You monitor everything from a central point.
- It’s strong protection against DDoS attacks that try to overwhelm your systems.
- You see the full flow of traffic across your network.
- Network threat detection often provides the earliest warning sign.
Network Security Limitations
- It can’t see what processes are running inside a device.
- Encryption can hide the contents of the traffic it inspects.
- Sometimes a device is already compromised before the network tools see anything wrong.
Over 90% of web traffic is encrypted (Google Transparency Report). This makes simple traffic inspection harder and pushes us toward more behavioral monitoring on both the network and the endpoint.
How Do Modern Setups Combine Both Layers?
Today’s security doesn’t pick one or the other. It blends endpoint and network monitoring into platforms that connect the dots in real time.
Teams are moving to models like Zero Trust Network Access (ZTNA) and Secure Access Service Edge (SASE). The core idea is simple: trust nothing, verify everything. Every device and every connection gets checked.
These integrated systems use technologies like:
- Extended Detection and Response (XDR)
- Security Information and Event Management (SIEM) platforms
- Shared threat intelligence feeds
- Automated response workflows
They tie device alerts to network events. For example, a suspicious finding on an endpoint might automatically trigger a network rule to contain that device. Or, a weird traffic pattern might cause a system to be isolated before the malware on it even activates.
This kind of visibility becomes much stronger when organizations are integrating EDR signals with network detection systems that monitor east-west traffic across corporate environments.
The industry is betting on this approach. Research from MarketsandMarkets projects the global Zero Trust market will grow to over $60 billion by 2027.
Endpoint Security Vs. Network Security: Which Comes First?

Alt text: Professional analyzing endpoint security vs network security options on dual holographic digital displays
You shouldn’t choose. You need a strategy that uses both, because attacks start in one place and move to the other.
Attackers usually get in through a device first. A phishing email, a stolen password, or a software vulnerability on a laptop gives them that initial access. Once they’re on one device, they try to move sideways across the network to find more valuable targets.
For smaller teams, starting with a solid endpoint protection platform makes sense. Device compromise is the most common problem, especially with remote work.
Larger companies typically deploy both layers at the same time. They have to protect their corporate network, thousands of remote devices, and cloud infrastructure altogether.
What you prioritize depends on a few things:
- How many devices do you have?
- How much are you using the cloud?
- What do your industry’s regulations require?
- Do you have a lot of IoT devices or scattered infrastructure?
From what we see with clients, combining endpoint protection with network threat detection is the only way to get clear visibility into modern, multi-stage attacks. The threats move, so your visibility has to move with them.
FAQ
What is endpoint security and why do endpoint devices need it?
Endpoint security protects endpoint devices such as laptops, phones, tablets, and IoT devices from malicious software and phishing attacks. These end-user devices connect to corporate networks every day.
If one device becomes infected, attackers may move deeper into the system. Tools such as antivirus software, Next-Generation Antivirus, and Endpoint Protection help detect threats early and protect the operating system and data security.
How does network security protect corporate networks from cyber threats?
Network security protects data that moves across corporate networks. Security teams use tools such as intrusion detection systems, Intrusion Detection and Prevention Systems, and Network Access Control to monitor traffic.
These systems search for Indicators of Compromise and block threats like DDoS attacks or lateral movement. Strong Wi-Fi security, perimeter security controls, and Virtual Private Networks also protect data encryption and network endpoint security.
What role does Endpoint Detection and Response play in endpoint protection?
Endpoint Detection and Response helps security teams monitor endpoint devices in real time. The system studies behavior with machine learning and behavioral analytics to find unusual activity.
When security incidents appear, it gathers Threat Intelligence and identifies Indicators of Compromise. This process helps security teams react quickly and start Automated Threat Containment, including actions such as device wipe or blocking malicious software.
How do Zero Trust and Multi-factor authentication improve data security?
Zero Trust requires every user and device to verify identity before gaining access. No connection receives automatic trust. Multi-factor authentication adds an extra step to confirm the user.
When used with Zero Trust Network Access, this method protects endpoint devices and systems during cloud adoption. It also reduces risk from phishing attacks and helps organizations maintain stronger data security.
How do modern platforms combine endpoint security and network security tools?
Modern security platforms combine endpoint security and network security tools into one system. Organizations may use an endpoint protection platform together with Unified Threat Management and Intrusion Prevention System controls.
Security Web Gateway, Cloud Access Security Broker, and Secure Access Service Edge also help protect cloud adoption. This approach supports Unified Security Fabric strategies and improves protection for data encryption and corporate networks.
Why Modern Security Requires Both Endpoint and Network Protection
Cyber attacks do not knock first. They slip into a laptop, hide in network traffic, then move across systems while no one sees the full picture. When endpoint security and network security work together, the story changes. Device signals meet network signals, and hidden threats become clear.
Ask yourself one simple question: Can we truly see what is happening in our network right now? If the answer feels unsure, it may be time to act. Join Network Threat Detection and start seeing the threats that attackers hope you miss.
References
- https://www.ndss-symposium.org/wp-content/uploads/2018/06/eurousec2018_11_Nthala_paper.pdf
- https://www.levelblue.com/blogs/levelblue-blog/network-security-vs-endpoint-security-key-differences-and-best-practices