A single hacked computer can let an attacker roam your entire network. Breaches like that cost companies an average of $4.45 million.
From our work, we know endpoint tools alone miss too much. They don’t see the traffic between machines. Pairing them with network security changes that. Your team can then trace an attack from the initial point of infection all the way through its path across your systems.
That full picture is critical. See how to build it below.
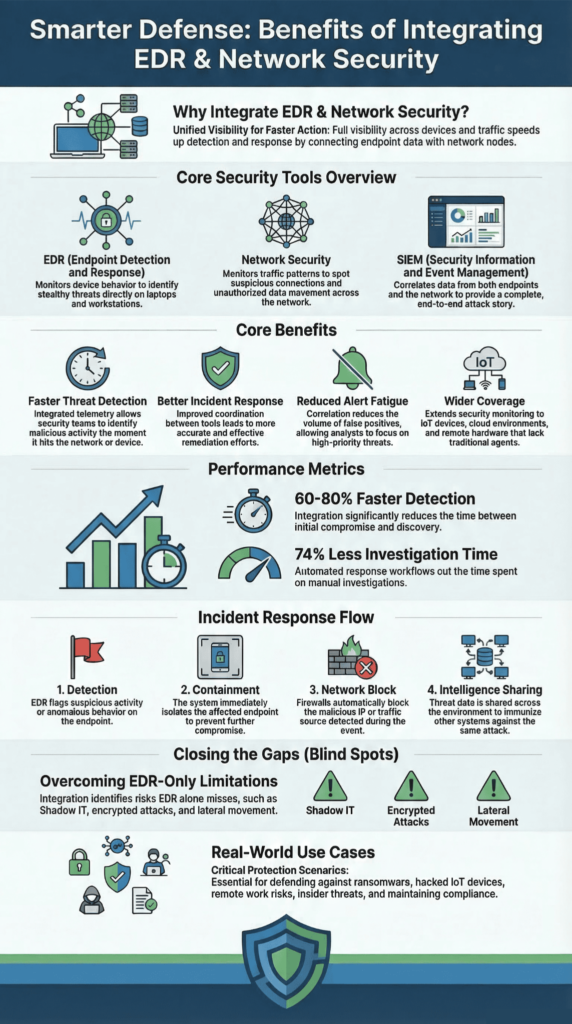
Core Benefits of Integrating EDR and Network Security
Bringing endpoint and network protection together gives security teams a clearer view of what is really happening inside their environment.
- Network Threat Detection, combined with Endpoint Detection and Response, provides full attack visibility across devices and network traffic.
- Integrated telemetry reduces mean time to detect (MTTD) and mean time to respond (MTTR) during security incidents.
- Correlated data from endpoints and network tools helps security professionals reduce alert fatigue and improve investigations.
What Are EDR and Network Security Tools?
Think of your security tools as two different watchmen. Endpoint Detection and Response (EDR) guards the individual devices, your laptops, servers, and phones. It watches what happens on them, like strange programs running or settings being changed. Network security tools are the guards at the gates and hallways. They watch the traffic moving between all those devices.
EDR is good at spotting tricky threats that hide from regular antivirus software. This includes fileless malware that lives in memory, or attackers using your own system tools against you. We see these every day.
The network watchmen see a different picture. They notice when a computer starts talking to a strange server on the internet, it’s never contacted before, or when there’s a sudden spike in traffic between two internal machines that shouldn’t be chatting.
In our work, we often spot suspicious patterns while detecting threats missed at the network level, often before endpoint tools realize a machine is fully infected.
By 2023, most big companies were using EDR. They stopped just looking for bad files and started watching for suspicious actions.
Here’s how the main tools fit together:
| Tool | Its Job | What It Catches |
| EDR | Watches what happens on your computers and servers. | Malware and odd behavior that needs investigating. |
| Network Threat Detection | Listens to the traffic between all your devices. | Strange calls to the internet or between machines. |
| IDS/IPS | Scans traffic for known attack patterns. | Tries to block common hacking methods. |
| SIEM | Gathers logs from all the other tools. | Puts the pieces together to tell the full story of an attack. |
Today, the best setups connect these tools. An EDR platform will feed its alerts into a SIEM, which can then check them against network traffic logs from an IDS. This creates a single, much clearer view.
Why We Combine Endpoint and Network Visibility

Attackers rarely stop at one computer. They break in, then move sideways through the network to find valuable data. If you only watch the endpoints, you miss this crucial movement.
A computer might look fine to its EDR agent. But at the same time, it could be quietly sending data to an attacker’s server or trying to log into other machines. That’s a network story, not an endpoint one.
We combine the views because we have to. In our own investigations, an endpoint alert is just the starting point. The real evidence usually lies in the network traffic, the calls made, the data sent, and the paths taken between systems.
As highlighted by Exabeam
“By integrating both, security teams can correlate network-level anomalies with endpoint activity, gaining a more complete understanding of an attack’s scope. This dual approach enhances incident detection, accelerates response times, and strengthens overall threat mitigation by covering both the network and device perspectives.” – Exabeam
For example, we’ve seen cases where an endpoint showed minor suspicious activity. But the network logs revealed it was “beaconing” out to a command server every five minutes, a sure sign of compromise. The endpoint tool missed that pattern; the network tool caught it.
The MITRE ATT&CK framework, a global knowledge base of hacker techniques, shows this clearly. Attacks are a sequence of steps: initial access, moving laterally, and stealing data. Some steps are visible on endpoints, some only on the network.
Putting both views together lets a security team do much better work:
- They can match a weird process on an endpoint with a suspicious connection it made.
- They can trace how an attacker jumped from the first infected machine to three others.
- They can map what they’re seeing to known hacker playbooks in MITRE ATT&CK.
Ultimately, this combination lets you follow the attack from the moment it gets in, all the way to what it was trying to steal. You’re not just putting out a fire on one machine; you’re seeing the arsonist’s path through the whole building.
How Integration Improves Threat Detection Speed
Credits: Arista Networks
The real benefit of connecting your endpoint and network tools is simple: you find threats much faster. Alone, each tool sees only part of the problem. Together, they tell the whole story sooner.
EDR tools watch what’s happening on your computers. They use behavior analysis and machine learning to spot odd things, like a strange script running or a program acting in a way it shouldn’t.
This catches modern threats that old antivirus software might miss, especially when security teams manage EDR agent deployment properly across laptops, servers, and remote devices.
Network tools watch the conversations between those computers. They notice when a machine starts talking to a shady server overseas, or when there’s a sudden, hidden flow of data leaving your network.
In our work, the network often tells us first. We’ve seen computers that looked perfectly healthy to their EDR agent, but were quietly “phoning home” to an attacker’s server every few minutes. The endpoint tool didn’t flag it; the network monitor did.
Research, like that cited by Xcitium Security, shows this combined approach can cut detection time by 60-80% in some security teams. That’s because you’re looking at multiple clues at once:
- A weird process on an endpoint (caught by EDR).
- A suspicious internet connection from that same endpoint (caught by the network).
- A known bad domain from a threat intelligence feed.
- How does all this match a known hacker technique in the MITRE ATT&CK framework.
Finding the attack faster means the hacker has less time to operate. This directly limits how much data they can steal and how far they can spread.
How Integration Strengthens Incident Response
When you find a threat, you need to stop it immediately. Integrated tools let you do that with one command, across both the infected device and your network.
Here’s how it works. Let’s say your EDR tool spots a malicious script. It can automatically isolate that computer to prevent the infection from spreading. At the exact same time, your network security can block all traffic to the hacker’s server that the script was trying to contact.
This kind of coordination becomes far easier when teams focus on integrating endpoint data with network telemetry so alerts and response actions are connected.
We use this constantly. The network data gives us crucial context in the first moments of an incident. It shows us not just the infected machine, but every other system it talked to. This lets us contain the breach in minutes, not hours, before it jumps to other machines.
According to IBM Security, this kind of automated, coordinated response can reduce investigation time by up to 74%. That’s a massive time savings.
A typical integrated response looks like this:
- Detection: An EDR alert flags suspicious activity on an endpoint.
- Containment: The EDR tool automatically isolates that endpoint.
- Network Block: Firewall or security gateway rules block traffic to the malicious IP or domain.
- Intelligence Sharing: Details of the attack are shared instantly with all other security tools to look for similar patterns.
This automation means your security team isn’t running around manually disconnecting machines and updating block lists. They can focus on the important work: figuring out how the attacker got in, what they did, and how to prevent it next time.
Does Integration Reduce Alert Fatigue for SOC Teams?
Yes, absolutely. The main reason is simple: it cuts down the noise. When your endpoint tools and network tools work separately, they each shout about every little thing they see. An analyst gets hundreds of alerts a day, and most are false alarms.
Many security teams use ten or more different monitoring tools. That’s a lot of separate alarm bells.
We’ve talked to teams drowning in alerts. They spend most of their day just figuring out which alerts are real and which are nothing. But when they started correlating network signals with endpoint alerts, things changed.
A single suspicious event, like a weird process on a computer and a strange outbound connection from that same computer, creates one high-priority alert instead of two separate, low-confidence ones.
Here’s the difference it makes for an analyst:
| Monitoring Model | What the Analyst Sees |
| Separate Tools | A flood of alerts from different places. Everyone needs to be checked. It’s slow and tiring. |
| Integrated Detection | Alerts are grouped together. One alert shows the full story from endpoint to network. It’s faster to judge. |
| Unified Dashboards | One screen shows everything connected. Investigations start in seconds, not hours. |
This cross-layer view helps security pros focus on real incidents, not harmless blips.
Where EDR Alone Creates Security Blind Spots

EDR is great, but it has limits. It can only see what’s happening on the computers where you can install its software. That leaves a lot of things in the dark.
Think about all the devices in a modern office that aren’t traditional computers: smart thermostats, security cameras, medical equipment, and industrial machines. Most of these “IoT” devices can’t run an EDR agent. If one gets hacked, your endpoint tools won’t see it.
Network monitoring sees these devices. It sees the traffic they send. So if a hacked camera starts sending data to a server in another country, the network tools will spot that strange conversation, even though the camera itself is “invisible” to EDR.
As noted by Fortinet
“EDR automatically discovers rogue devices, IoT devices, and applications and their vulnerabilities, based on risk mitigation policies for existing and unmanaged endpoints connected to the network. This is to either bring them under management, set up communication control policies, or set up virtual patching policies.” – Fortinet
We see this gap all the time, especially in companies with lots of cloud services and remote workers. The network view becomes critical.
Here are common blind spots when you only use EDR:
- Shadow IT: Devices employees bring in without approval. No agent, no visibility.
- Encrypted Attacks: Hackers hiding their commands in encrypted traffic. EDR might not see inside.
- Lateral Movement: An attacker hopping from one computer to another across the network.
- Insider Threats: A person using their access to move sensitive files between systems.
Guidance from the National Institute of Standards and Technology (NIST) supports this. Their framework stresses layered monitoring for complex environments.
Using network and endpoint tools together closes these gaps.
Real-World Use Cases of EDR and Network Security Integration
So where does this actually help? In almost every modern IT setup.
Big companies use it to protect their mix of old servers, employee laptops, and cloud services. The cloud makes things especially tricky. An employee’s laptop (with EDR) might be compromised and used to attack a cloud server. Network monitoring can see the suspicious link between them.
From our work with security data, we find network detection is key for tracing these cross-environment attacks. You can follow the trail from an on-site server to a cloud storage bucket.
Research from Gartner suggests that by 2026, about 40% of organizations will use unified platforms (called Open XDR) to bring all these signals, endpoint, network, identity together.
Here are a few specific situations where the combination is essential:
- Stopping Ransomware: Seeing it try to encrypt one machine (EDR) and then communicate to others on the network to spread (Network).
- Finding Hacked IoT Devices: Spotting unusual traffic from a smart printer or sensor.
- Securing Remote Work: Monitoring home laptops for signs they’re connecting to malicious sites.
- Investigating Insider Theft: Correlating a user downloading files (EDR) with them sending those files externally (Network).
This integration also helps with compliance. Having clear, correlated logs makes it much easier to show auditors what happened during an incident.
Many organizations add other tools around this core, like Cloud Access Security Brokers (CASB) for cloud apps or Secure Access Service Edge (SASE) for secure remote access.
FAQ
How does Endpoint Detection and Response support network security?
Endpoint Detection and Response supports network security by monitoring both devices and data movement. Endpoint detection tracks endpoint activity on laptops, servers, and IoT devices through the operating system. Network security tools monitor network traffic and detect lateral movement between systems.
When both work together, security teams gain stronger threat detection, faster incident response, and better protection against cyber threats and data breaches across the full attack surface.
Why do modern EDR tools use machine learning?
Modern Endpoint Detection and Response tools use machine learning to identify suspicious behavior that traditional antivirus software may miss. Behavioral analysis and behavioral analytics review endpoint activity, malware infections, and fileless malware patterns.
AI and machine learning systems compare behavior against known threat patterns and indicators of compromise. This approach helps security teams reduce alert fatigue and detect cyber threats before attackers cause serious damage.
How does integration help threat hunting for security teams?
Integration between endpoint security and network security improves threat hunting for security teams. Security professionals can examine endpoint activity, network traffic, and lateral movement from a single investigation view.
Threat intelligence and threat intelligence feeds provide context for suspicious behavior. Many teams also rely on the MITRE ATT&CK framework to map threat patterns and investigate indicators of compromise during security incidents.
Does EDR integration improve incident response time?
Integrating Endpoint Detection and Response with network security improves incident response time. Endpoint detection reveals actions occurring inside the operating system, while network security shows how malware infections move through network traffic.
Security teams use forensic analysis and root cause analysis to understand the attack path. These insights help security professionals apply containment policies and automated response workflows to stop active security incidents quickly.
How does combining endpoint and network security strengthen cyber defense?
Combining endpoint security and network security strengthens Cyber Security strategies such as Zero Trust. Organizations must protect laptops, IoT devices, and Industrial control systems as cloud adoption continues to grow.
Technologies such as an endpoint protection platform, Next-Generation Antivirus, and behavior-based detection monitor endpoint activity. This layered defense reduces the attack surface and helps block supply chain attacks or zero-day exploits before they escalate into major security incidents.
Why Integrated EDR and Network Security Strengthens Cyber Defense
Cyber attackers rarely knock on the front door. They slip through small gaps—one strange packet, one quiet connection, one signal most tools miss. Many breaches start this way. Quiet. Slow. Hard to see.
That is why watching only endpoints is not enough. Strong defense means seeing both the device and the network. When teams connect those signals, hidden activity becomes clear before real damage begins.
Security teams deserve tools that show the full story. If you want to spot threats earlier, join Network Threat Detection and see how unified visibility helps you defend your network with confidence.
References
- https://www.exabeam.com/explainers/network-detection-and-response/ndr-vs-edr-key-differences-pros-cons-using-them-together/
- https://www.fortinet.com/uk/resources/cyberglossary/what-is-edr