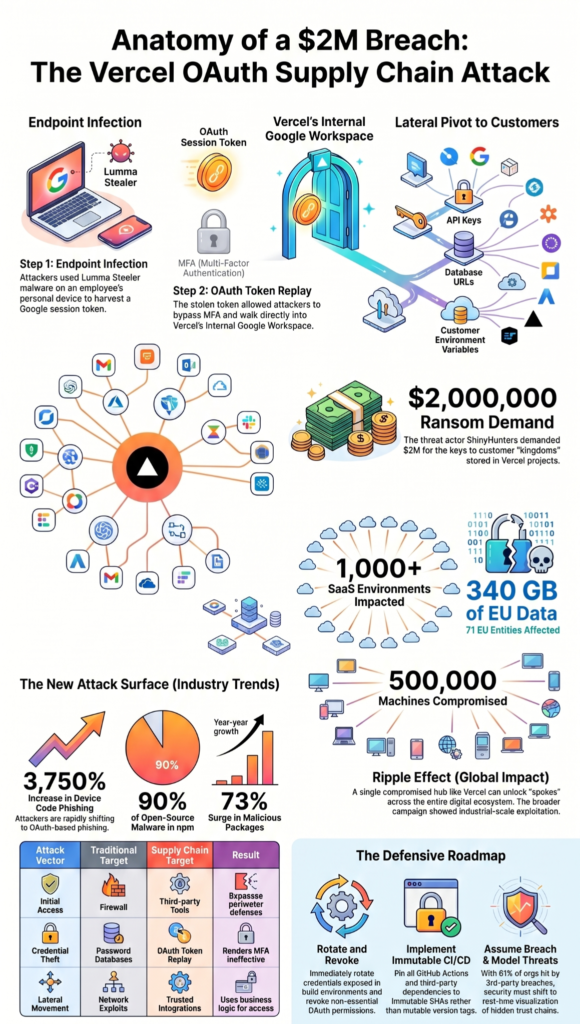
The Vercel breach in April 2026 wasn’t a sophisticated hack of their servers. It was a simple, devastating replay of a stolen OAuth token. Attackers infected a Vercel employee’s personal device with Lumma Stealer malware, harvested their Google session token, and used it to walk right into Vercel’s internal Google Workspace.
From there, they accessed customer environment variables and posted a $2 million ransom on BreachForums. This incident reveals a fundamental flaw in our trust of third-party AI tools and the OAuth connections that bind them.
Keep reading to understand the kill chain that bypassed MFA and compromised over a thousand SaaS environments.
Key Statistics on the Vercel Supply Chain Breach
The April 2026 Vercel incident is not an isolated event but a data point in a rapidly escalating trend of software supply chain and third-party attacks. The numbers below paint a stark picture of the scale, methodology, and systemic risk facing modern development and deployment ecosystems.
- $2,000,000 – The ransom demand posted on BreachForums by the threat actor ShinyHunters for the stolen Vercel data.
- ~580 employee names, emails, status records – The number of Vercel employee records exposed in the internal database dump.
- 1,000+ – The number of SaaS environments impacted by the related TeamPCP supply chain campaign, as tracked by Mandiant.
- ~500,000 – The estimated total number of machines compromised across the broader supply chain campaign, according to industry analysis.
- 73% – The year-over-year increase in malicious open-source package detections, per ReversingLabs’ 2026 report.
- 340 GB uncompressed (91.7 GB compressed) – The volume of European Commission data exfiltrated via a separate Trivy supply chain compromise.
- 71 clients (42 internal EC departments + 29 other EU entities) – The number of EU entities affected by the European Commission cloud breach stemming from the supply chain attack.
- 90% – The percentage of all open-source malware in 2025 that was delivered via malicious npm packages.
- 3,750% (37.5x) – The staggering increase in device code phishing attacks, a primary method for OAuth token abuse, from 2025 to 2026.
- 61% – The proportion of organizations that reported experiencing a third-party breach in the past year, highlighting the pervasive nature of this risk.
$2,000,000: The Price of Trust in the OAuth Chain

According to Coinspeaker and statements from Vercel CEO Guillermo Rauch (April 19, 2026), the ransom demand reached $2,000,000. That seven-figure ransom demand wasn’t for Vercel’s source code. It was for the keys to their customers’ kingdoms: the environment variables.
The attackers knew the real value lay in the credentials stored within Vercel projects, database URLs, API keys, internal service tokens. By accessing these, they could pivot into a thousand different customer environments.
The ransom figure signals a shift. Attackers are no longer just disrupting service, they’re commoditizing access. They’re selling the means to breach, turning a single point of failure into a recurring revenue stream.
The high price tag reflects the perceived quality and breadth of the data, a direct result of the supply chain’s deep, trusted access.
580 Employee Records: The Human Foothold

As reported by Coinspeaker (April 19, 2026), nearly 580 employee records were exposed in the breach. The exposure of nearly 600 employee records is more than a privacy violation. It’s a roadmap for future attacks. With names, emails, and employment status, threat actors can craft hyper-targeted phishing campaigns, a technique known as spear-phishing. They might impersonate HR to distribute fake “security training” links, or pose as a fellow engineer with an urgent “context.ai” issue.
This data turns a faceless corporation into a list of vulnerable individuals. Each record represents a potential new entry point, a way to bypass technical controls by exploiting human psychology. The breach of employee data ensures the attack has a long tail, enabling secondary social engineering campaigns long after the initial OAuth tokens are rotated.
1,000+ SaaS Environments: The Domino Effect
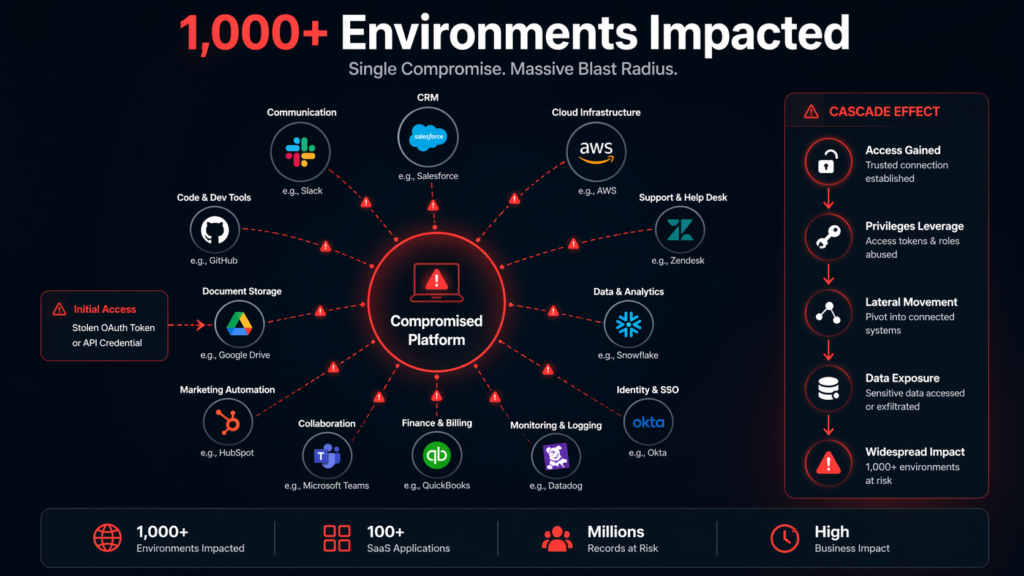
According to Mandiant, via SANS ISC reporting (April 2, 2026), over 1,000 SaaS environments were impacted. When Mandiant reported over a thousand SaaS environments impacted, they were mapping the ripple from a single stone. The Vercel breach wasn’t the end goal, it was a strategic pivot point. Compromising a central deployment platform like Vercel gives attackers a centralized console to potentially thousands of downstream applications.
Each connected SaaS environment, a CRM, a data warehouse, a customer support tool, becomes a new victim without the attacker needing to breach it directly. This is the core promise and peril of modern integration. The efficiency of connected tools creates a breathtaking attack surface. One compromised OAuth token at a hub like Vercel can theoretically unlock spokes across the digital ecosystem.
500,000 Machines Compromised: The Campaign’s True Scale

Based on estimates from The Register citing SANS ISC (April 2, 2026), approximately 500,000 machines were compromised. The half-million machine estimate reveals this was industrial-scale exploitation. This wasn’t a targeted hack against Vercel alone, but part of a sprawling campaign, likely automated and fueled by the same initial access brokers.
The scale suggests the attackers used the initial foothold, whether through stolen OAuth tokens or malicious npm packages, to deploy payloads that spread laterally within networks. It points to a mature cybercriminal operation with clear objectives: establish persistent backdoors, deploy cryptominers, or prepare for large-scale data exfiltration.
The number underscores that the Vercel incident is a single, high-profile symptom of a much wider epidemic in the software supply chain.
73% Increase in Malicious Packages: The Poisoned Well
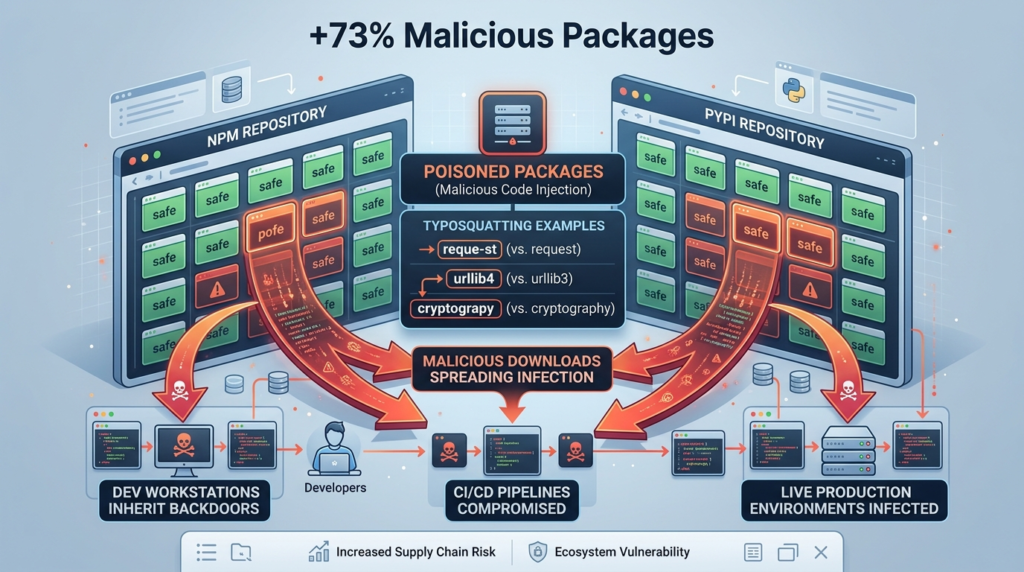
ReversingLabs‘ finding of a 73% year-over-year surge is a clear indicator that open-source repositories are under sustained assault. Attackers are flooding npm, PyPI, and RubyGems with malicious packages, often using “typosquatting” (names similar to popular libraries) or compromising maintainer accounts.
The driving force is automation and reach. A single malicious package can be pulled thousands of times automatically by build scripts and CI/CD pipelines. It’s a force multiplier. Developers, trusting the ecosystem, npm install their way into a breach.
This trend forces a radical rethink of dependency management, moving from implicit trust to continuous verification and deep artifact inspection.
340 GB of EU Data: When Trusted Tools Betray You

According to CERT-EU advisories via SANS ISC (April 3, 2026), 340 GB of data was exfiltrated from the European Commission. The exfiltration of 340 GB from the European Commission via a compromised Trivy security scanner is a profound irony.
A tool designed to find vulnerabilities became the vulnerability. This highlights the “trusted advisor” problem in supply chain attacks. The most dangerous compromises aren’t of random libraries, but of the utilities you explicitly bring in to enhance security, compliance, or operations.
These tools often demand high levels of access to do their job, scanning code, checking configurations, deploying patches. When they turn malicious, that privileged access is turned against you. The massive data haul shows attackers aren’t just planting backdoors, they’re using these positions of trust to conduct wholesale data theft.
| Attack Vector | Traditional Target | Supply Chain Target | Result |
| Initial Access | Firewall, VPN, Email Gateway | Third-party Tool (e.g., Context.ai, Trivy) | Bypasses perimeter defenses |
| Credential Theft | Password Database, Keylogger | OAuth Token Replay, CI/CD Secrets | Renders MFA ineffective |
| Lateral Movement | Network Exploits, Privilege Escalation | Trusted Integrations (e.g., Vercel Env Vars) | Uses existing business logic for access |
71 EU Entities: The Blast Radius of a Shared Tool
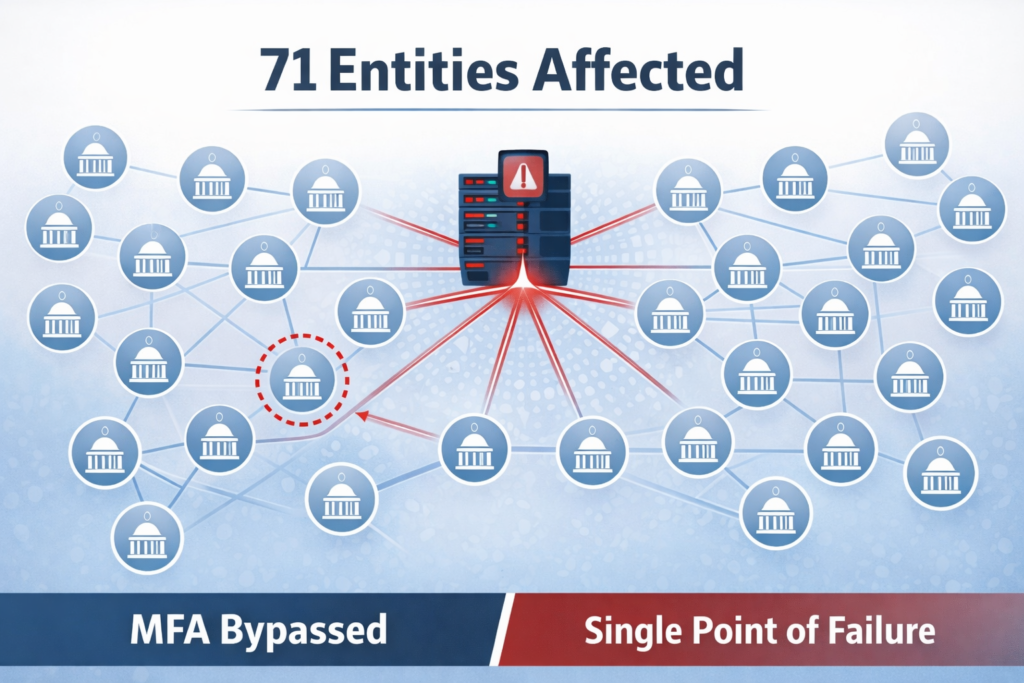
As reported by CERT-EU via SANS ISC (April 3, 2026), 71 EU entities were affected. The 71 affected EU entities demonstrate how a shared utility or platform creates concentrated risk. A single compromised tool within a shared services environment, like the European Commission’s cloud, doesn’t just affect one department. It instantly exposes every entity that relies on that shared service.
This is a major challenge for governments and large enterprises. The push for operational efficiency and cost-saving through centralized IT creates a “single point of failure” security model. An attacker who understands this architecture, as the Vercel attackers clearly did, will target these central nodes precisely because the payoff is multiplied across the entire organization and its partners.
90% of Open-Source Malware via npm: The JavaScript Ecosystem Under Siege

According to the ReversingLabs 2026 Report (January 27, 2026), 90% of malicious open-source packages are found in npm. The fact that 9 out of 10 malicious open-source packages are in npm is a startling indictment of the JavaScript ecosystem’s security model. Its sheer volume, ease of publication, and deeply nested dependency trees make it a perfect hunting ground. The drivers are clear:
- Low barrier to entry for publishing.
- Automatic dependency resolution pulls in sub-dependencies unseen by developers.
- A culture of micro-packages creates complex, fragile dependency graphs.
Attackers exploit this by creating packages that seem helpful, or by hijacking popular ones. The result is that modern web applications, built on thousands of these dependencies, are constantly at risk of importing malice alongside functionality. This stat forces a confrontation with the foundational security of the world’s most popular software registry.
3,750% Increase in OAuth Device Code Phishing: MFA’s Achilles’ Heel
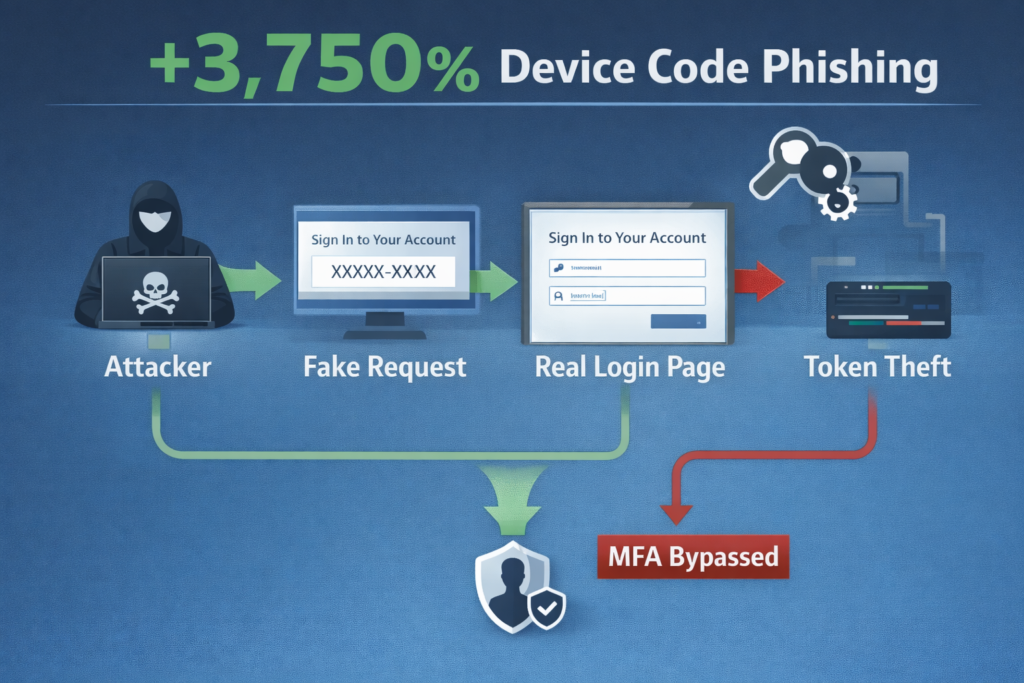
According to Push Security via BleepingComputer (April 4, 2026), device code phishing attacks have increased by 3,750%. This astronomical spike is the most critical technical trend revealed by the data. OAuth device code phishing is how the Vercel breach likely started. Here’s the simple, devastating process:
- Attacker initiates an OAuth login for a service like Google or Microsoft.
- The service provides a device code for the user to enter at a URL like microsoft.com/devicelogin.
- The attacker tricks the victim (e.g., via a fake helpdesk ticket) into entering that code on the real Microsoft page.
- The victim’s authentication is completed, and the session token is handed to the attacker.
The token is then replayed, making Multi-Factor Authentication (MFA) useless. The surge shows - attackers have found a highly effective, scalable way to bypass the strongest common authentication defense. They’re not breaking MFA, they’re tricking users into handing it over.
61% of Organizations Suffered a Third-Party Breach: A Systemic Failure

According to Help Net Security via 6clicks (2024–2026), 61% of organizations experienced a third-party breach in the past year. When nearly two-thirds of organizations report a third-party breach, it’s no longer an operational risk, it’s a certainty.
This number confirms that perimeter defense is obsolete. Your security is now the collective security of every vendor, tool, and open-source library in your stack. The driving force is the interconnectedness of modern business.
Every new SaaS app, AI integration, and deployment plugin adds another link to a chain of trust you can’t fully audit or control. The Vercel breach is a textbook example: Context.ai’s security became Vercel’s problem, which then became every Vercel customer’s problem.
This statistic is a mandate for a new security paradigm focused on continuous third-party exposure assessment and real-time threat modeling.
FAQ
What actually happened in the April 2026 supply chain attack?
The April 2026 incident involved a supply chain OAuth attack triggered by a Context AI breach. Attackers used a compromised employee account takeover to access internal systems. Through Google Workspace hijack and OAuth compromise, they achieved lateral movement, exposing non-sensitive env vars and internal metadata. This highlighted third-party AI risk and weaknesses in OAuth supply chain trust across enterprise environments.
How did attackers gain access to internal systems?
Attackers leveraged a compromised Context.ai OAuth app with broad scopes, exploiting OAuth app authorization risk. This allowed credential exfiltration AI techniques and bypassed perimeter defenses. Using the Google OAuth app ID and internal env enumeration, they moved laterally. The breach showed how enterprise AI tooling risk and agentic supply chain agents can create an enterprise AI foothold without traditional malware.
What type of data was exposed during the breach?
The breach led to environment variable exposure, including non-sensitive data read and unencrypted credentials leak. Reports mention API keys compromised, GitHub tokens exposed, and NPM tokens stolen. While encrypted sensitive vars stayed safe, attackers accessed employee database dump records and internal metadata. The incident also raised concerns about proprietary source code leak risks and internal infra navigation visibility.
Why are AI integrations increasing supply chain risks?
AI integration security gaps often stem from excessive OAuth scopes and weak third-party risk management. Tools with deep access can enable credential theft, rapid privilege escalation, and internal systems access. This case shows how TPRM AI tools and OAuth supply chain trust can fail. Enterprise AI tooling risk grows when non-encrypted at rest vars and broad permissions are left unchecked.
What should organizations do to prevent similar attacks?
Organizations should enforce credential rotation advisory, tighten OAuth scopes, and audit AI platform credential theft risks. Strong third-party risk management and continuous monitoring for IOC OAuth app ID activity are critical. Protect sensitive var storage, validate Google Workspace admin checks, and reduce internal env enumeration exposure. Limiting lateral movement and reviewing dev tool supply chain dependencies can significantly reduce future attack impact.
Rethinking Defense After the Vercel Supply Chain Breach
The story of the Vercel supply chain breach isn’t about a single vulnerability. It’s about the collapse of a security model built on perimeter defense and implicit trust. The kill chain, from a stolen OAuth token to a $2 million ransom, proved that attackers are now hunting in the spaces between your tools, in the trusted connections you approved and forgot.
They target the non-sensitive environment variable, the unpinned GitHub Action, the third-party MCP server with your API key. The data shows this is accelerating: 3,750% growth in OAuth attacks, 73% more malicious packages, 61% of organizations already hit.
Practical advice starts with assuming breach. Rotate every credential that could have been exposed, today. Audit your OAuth integrations and revoke anything non-essential, especially those with env:read or deployments:write scopes.
Pin all CI/CD actions to immutable SHAs, not tags. Most importantly, implement continuous threat modeling that can visualize these hidden trust chains and detect anomalous access patterns in real-time, before the attacker finishes enumerating your environment variables. Check your own project’s exposure to these exact attack vectors now with a dedicated supply chain security scan.


