Network Taps Vs. SPAN/Mirror Ports: What Matters
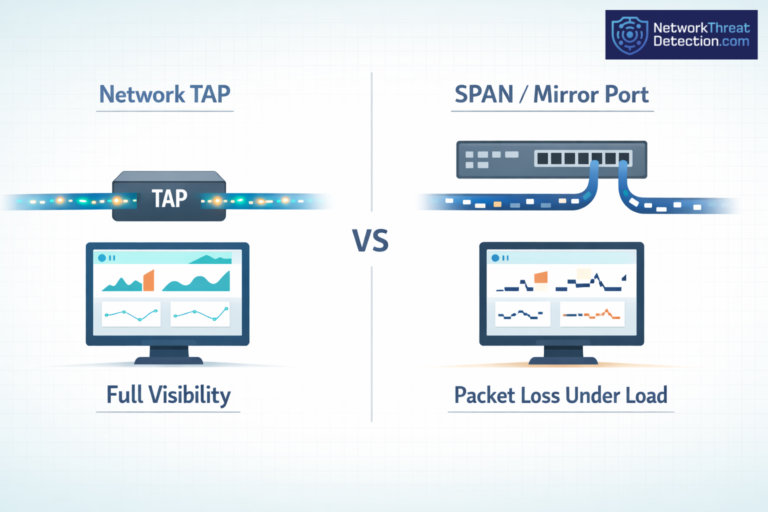
Network taps see every packet. SPAN ports can miss some when traffic spikes. That gap shows up fast in real networks, especially with tools like Gigamon and Keysight. Teams notice it during audits or when chasing odd issues. With higher…