
Challenges Monitoring Multi Cloud Environments at Scale
Challenges monitoring multi cloud environments come from one simple issue: too many systems that don’t connect well. Teams…

Challenges monitoring multi cloud environments come from one simple issue: too many systems that don’t connect well. Teams…

Cloud native security monitoring tools give real-time visibility into cloud environments by tracking APIs, containers, and runtime behavior…

Google cloud platform gcp logging brings all your logs into one place. You can see what’s happening across…

Azure monitor activity log analysis helps track who did what, when, and where across your Azure environment. It…
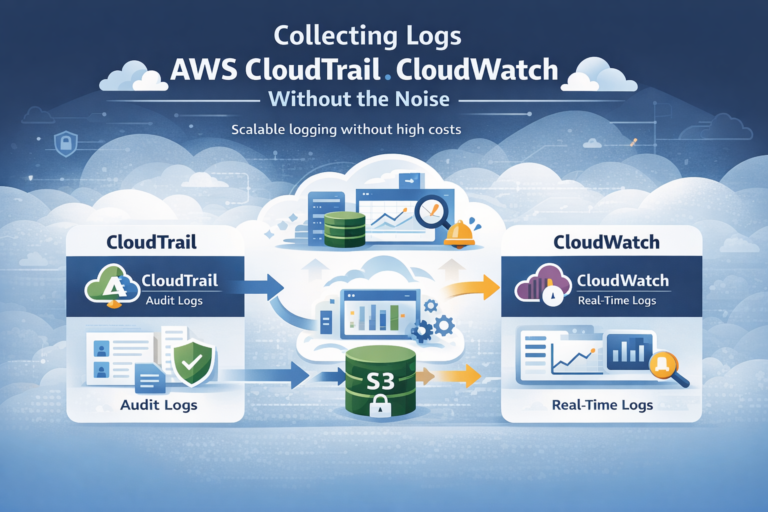
Collecting logs AWS CloudTrail CloudWatch works best when you treat it as a system, not a checkbox. It…

Cloud logs are the activity records from services like AWS, Azure, and Google Cloud. We use them to…