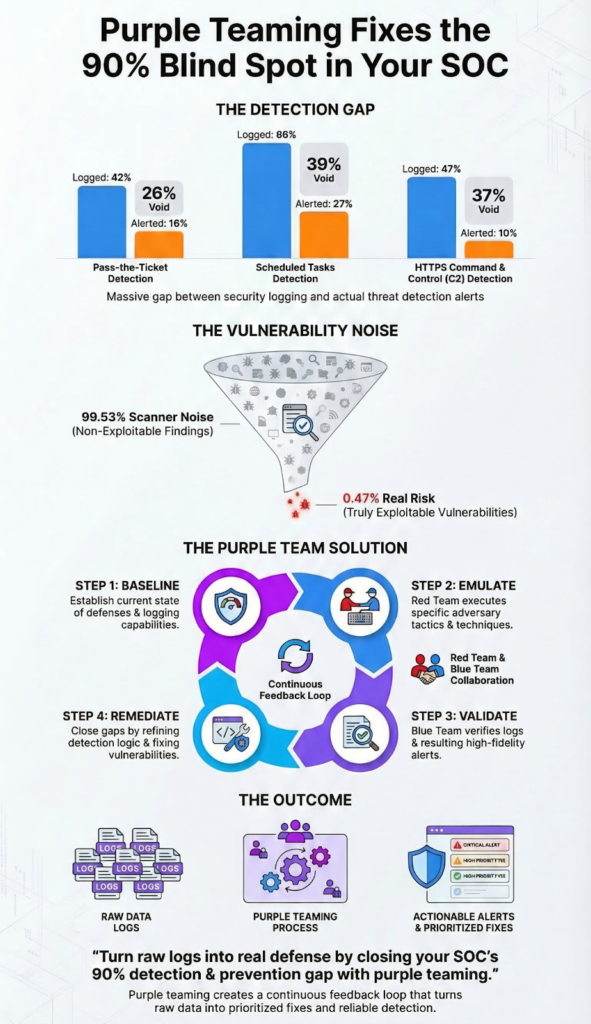
It’s because you’re collecting data, not detecting threats. That 90% gap isn’t about missing logs, it’s about your tools failing to see the attack inside them. Consider this: while 42% of pass-the-ticket attacks are logged, only 16% trigger an alert.
Your team has the puzzle pieces, but the picture never forms. Purple teaming directly addresses this by forcing your red and blue teams to collaborate, turning that collected data into a coherent, actionable defense.
It’s the practice that closes the chasm between what you see and what you can stop. Keep reading to learn how to transform your visibility into real security.
Purple Teaming in Action: Closing Detection & Prevention Gaps Fast
This section captures how purple teaming sharpens real-world defense by focusing only on what truly matters.
- Purple teaming converts passive logging into active detection by validating which security events actually trigger alerts.
- It cuts through 99.53% of vulnerability scanner noise to focus remediation on the 0.47% of flaws that are truly exploitable.
- The process directly attacks “security debt” by creating a continuous feedback loop that prioritizes and fixes critical risks faster.
The Moment the Mirage Became Real

I remember the first time we saw it. We were reviewing a routine threat simulation, something about lateral movement. The logs were full, pages and pages of event IDs. The red team was confident they’d slipped through.
The blue team pointed to the logs, saying, “See? We captured it.” But no alert had fired. The SIEM had dutifully recorded the pass-the-ticket attempt, a 42% rate according to the Purple Perspective 2026 report by Security Risk Advisors, but the rule to flag it never tripped, highlighting how detecting threats hidden inside normal-looking network activity remains one of the hardest gaps to close.
That was the moment the “logging mirage” became real for us. We had all the data, but none of the intelligence. The attack was right there, hiding in plain sight.
This isn’t an isolated failure. It’s the standard. Security Risk Advisors’ 2026 Purple Perspective report paints a stark picture of this detection gap. It’s not that techniques go completely unseen. They’re often recorded.
- Pass-the-ticket attacks are logged 42% of the time.
- Scheduled task persistence shows up in logs 66% of the time.
- Even stealthy HTTPS command and control over port 443 gets logged 47% of the time.
The problem is the next step. Logging is passive. Detection is active. The jump from one to the other is where defenses crumble, particularly when authentication logs and user activity signals fail to translate into actionable alerts.
The Logging Mirage: When Visibility Isn’t Security

You build your security stack for visibility. You deploy agents, you tune parsers, you ensure logs flow from every endpoint and server. The dashboard fills with green checkmarks. Visibility achieved.
But here’s the uncomfortable truth Security Risk Advisors uncovered: high logging rates create a dangerous illusion of safety. It’s a mirage. Your team has the raw feed, but the analysis engine, the part that decides what’s normal and what’s malicious, is lagging far behind, especially when endpoint signals aren’t properly correlated with network context through integrating EDR capabilities into broader security workflows.
Data from Network Threat Detection demonstrates
“These findings confirm that security teams are drowning in data but starving for context. At Network Threat Detection, we go beyond simple logging to model attack paths and prioritize risks based on actual exploitability and business impact, turning that 42% log rate into a 100% validated defense.” – Network Threat Detection
Take scheduled tasks, a common persistence mechanism. The logs catch it two-thirds of the time. That feels good. Yet, an alert is generated in only 27% of cases.
Where did the other 39% go? They vanished into the noise floor, lost between benign system activity and poorly tuned correlation rules. The same story repeats. The log is the potential; the alert is the action. Without the alert, the log is just a historical footnote written after the breach.
The Data Behind the Detection Gap
This gap is quantified, and it’s wider than most teams want to admit. The following table from the Purple Perspective report illustrates the chasm between having data and having defense.
| Attack Technique | % Logged | % Alerted | The “Gap” |
| Pass-the-Ticket | 42% | 16% | 26% |
| Scheduled Tasks | 66% | 27% | 39% |
| HTTPS C2 (Port 443) | 47% | 10% | 37% |
This table isn’t just numbers. It’s a direct map of your SOC’s blind spots. The “Gap” column is where attackers live and operate freely. The most shocking line is that last one.
Nearly half of all HTTPS command and control traffic is seen, but only one in ten instances screams for attention. That’s a 90% blind spot for one of the most common exfiltration paths.
This gap explains the broader statistic that keeps CISOs up at night. A separate analysis suggests traditional SIEMs detect only about 21% of MITRE ATT&CK techniques on average. Think about that.
A framework designed to catalog adversary behavior, and the core tool of the SOC misses nearly 80% of its documented techniques. It’s not because the techniques are invisible. It’s because the logic connecting the logged events into a story of attack is missing or misfiring.
Purple team exercises are designed to find these logic gaps. They don’t just test if you see an action, they test if you understand its intent.
Why Your Vulnerability Scanner Is Crying Wolf
Credits: Simply Cyber – Gerald Auger, PhD
So you focus on prevention. You run your scanners weekly, and the report lands with thousands of findings. Critical, High, Medium. The team groans. The backlog stretches for months. But what if almost all of it was a distraction? Data from Hadrian’s 2026 Offensive Security Benchmark is jarring.
According to research from Hadrian, out of tens of thousands of vulnerability scanner findings, only 0.47% prove to be exploitable in a real-world environmen.
Let that number sink in. For every 200 vulnerabilities flagged, less than one poses an immediate, realistic threat. The other 199? They might be in code paths no attacker can reach, require credentials they don’t have, or be protected by a compensating control the scanner can’t see.
This is the 99.53% noise problem. It paralyzes teams. It’s no wonder 95% of security leaders report dissatisfaction with their ability to prioritize remediation based on real-world risk. They’re sifting through a mountain of gravel looking for the one piece of uranium.
Cutting Through the Noise with an Offensive Lens
Purple teaming cuts through this noise by applying an offensive lens. The red team doesn’t care about the CVSS score. They care, “Can I use this to get a shell?” They test the path. When they find that one exploitable flaw in a hundred, it gets immediate, validated context.
The blue team no longer sees “CVE-2024-12345, Critical.” They see, “This is the SQL injection on the customer portal that let us exfiltrate the database. Here’s the proof.”
The conversation shifts from theoretical risk to proven exploitability. This is how you move from a 95% dissatisfaction rate to confident action. You stop chasing ghosts and start hunting threats.
- It shifts focus from quantity (2,090 attacks per week, globally) to quality (which one will target us?).
- It replaces generic severity scores with evidence of actual access gained.
- It turns a sprawling list into a targeted punch list for the patching team.
This approach is what we built into our own philosophy at Network Threat Detection. We start by assuming the scanner is mostly wrong, and then prove what’s right. It’s the only way to keep your head above water.
How Security Debt Fuels the Prevention Crisis
This noise creates a backlog. The backlog becomes debt. And security debt, like any debt, accrues dangerous interest. Veracode’s 2026 report found that 82% of organizations now carry this debt, known vulnerabilities that remain unremediated over time.
According to SecurityBrief Asia, the most alarming part is that 60% of the most severe, exploitable flaws have been left unresolved for more than a year. We find things faster than we can fix them, and the critical items get lost in the shuffle.
Think about that for a year. A flaw with a public exploit, something that could give an attacker initial access or let them move laterally, just sitting there. Marked as “Critical” in a ticketing system, maybe.
But not fixed. Why? Because the team is overwhelmed by the 99.53% of non-exploitable noise. Because the alert for the associated TTP never fired, so the perceived urgency faded. The gap between detection and prevention isn’t just technical, it’s cultural and procedural.
It’s a system designed to find problems, but not optimized to solve the right ones.
Attacking Debt with a Continuous Feedback Loop
Purple teaming attacks this debt directly. By its very nature, it creates a continuous feedback loop focused on closure. An exercise doesn’t end with a report. It ends with a debrief. “Here’s how we got in. Here’s what didn’t alert.
Here’s the one vulnerability we used.” The output isn’t another ticket for the bottom of the pile. It’s a validated, contextualized, and prioritized action item.
It has a story attached to it, a demonstration of business impact. This makes it politically and practically easier to mobilize resources and get it done. You’re not just patching a bug, you’re closing a documented breach path. That’s how you stop adding to the 60% pile.
The exercise proves the risk is real, not just a line on a compliance checklist. It turns abstract debt into concrete action.
Building Your Purple Team Workflow: From Blind Spot to Control
Implementing this isn’t about hiring a new team. It’s about changing the rhythm of the ones you have. It’s a workflow that synchronizes offense and defense into a single, iterative cycle. The goal is to systematically convert your 42% log rate into a 100% detection and prevention rate for the techniques that matter most to your organization.
The Four-Step Cycle for Closing Gaps
Start by baselining. Honestly assess your current coverage. If the average SIEM detects 21% of ATT&CK techniques, where do you stand? Map your alert rules to the framework. The gaps you see are your starting point for exercises. Next, emulate.
Don’t just run a generic scan. Have your red team or a tool execute specific, relevant TTPs. Try that HTTPS command and control over port 443. Can your tools see it? More importantly, will they yell about it?
Then, validate. This is the core of the purple moment. Gather the red and blue teams. The red team shows what they did. The blue team shows what they saw. Did the 47% log happen? Did the 10% alert? If not, why? Tune the rule, add a new data source, adjust the threshold.
Finally, remediate. Take the findings, especially any exploitable vulnerabilities uncovered, and move them to the top of the pile. You’re not prioritizing based on a score, but on proven weaponization.
- Baseline against the MITRE ATT&CK framework.
- Emulate with precise, realistic attack simulations.
- Validate detection and alerting in a joint session.
- Remediate based on proven exploitability, not theoretical scores.
This cycle turns sporadic testing into a continuous engine for improvement. It breaks down the walls between the team that finds flaws and the team that fixes them. Every exercise makes your detection sharper and your prevention more targeted.
You stop worrying about the 2,090 global attacks and start focusing on the handful of paths an attacker would actually use against you. It’s how you build a defense that learns.
FAQ
What is purple teaming and how does it find detection and prevention gaps?
Purple teaming combines red team blue team collaboration to run cybersecurity exercises that expose detection gaps and prevention gaps. It uses threat simulation and adversary emulation based on real-world threats.
This approach improves security posture assessment, highlights security monitoring gaps, and enables better vulnerability identification through continuous feedback loop and actionable insights.
How does purple teaming improve incident response and security resilience?
Purple teaming strengthens incident response improvement by testing security control testing and defensive evaluation in real scenarios. It enhances security resilience through attack simulation, faster attack detection speed, and better vulnerability remediation.
With ongoing red team feedback and blue team training, organizations achieve stronger cyber defense enhancement and more effective breach prevention strategies over time.
What tools and techniques are used during purple teaming exercises?
Purple teaming uses tactics techniques procedures aligned with the MITRE ATT&CK framework. Teams run threat hunting exercises, penetration testing, and ransomware simulation. Tools like SIEM optimization, EDR gaps analysis, and XDR integration help identify weaknesses.
Techniques such as behavioral analytics gaps review and anomaly detection enhancement improve detection of advanced threats.
Where do most detection and prevention gaps usually appear?
Detection gaps often appear in endpoint detection gaps, network security gaps, and cloud security gaps. Common issues include IAM vulnerabilities, privilege escalation detection failures, and lateral movement prevention weaknesses.
Prevention gaps also exist in phishing detection gaps, insider threat prevention, and misconfiguration prevention, especially across third-party vendor assessment and supply chain risk detection.
How can teams apply lessons from purple teaming to improve security?
Teams should focus on lessons learned implementation after each exercise, using post-exercise debrief sessions. Improving cross-team communication, toolset interoperability, and security team collaboration is key.
Applying zero trust validation, defense in depth testing, and continuous security awareness training helps close gaps and supports long-term maturity model advancement and stronger overall security culture building.
From Data to Defense: The Purple Team Mandate
The 90% detection gap isn’t a mystery. It’s the natural result of disconnected tools and siloed teams. Purple teaming is the deliberate practice of closing that gap, turning raw logs into real detection, cutting through noise, and transforming security debt into action. It shifts teams from passive monitoring to actively proving what actually works.
If you want to operationalize that shift, platforms like Network Threat Detection help teams model real attack paths, prioritize exploitable risks, and uncover blind spots before attackers do. With continuous threat intelligence and frameworks like MITRE ATT&CK, it enables SOC teams to move faster, reduce noise, and focus on the threats that truly matter.
References
- https://sra.io/press-release/press-release-security-risk-advisors-releases-the-purple-perspective-2026-report/
- https://hadrian.io/de/blog/more-than-two-thirds-of-security-teams-struggle-to-keep-up-with-the-growing-number-of-vulnerabilities
- https://securitybrief.asia/story/security-debt-surges-as-legacy-vulnerabilities-pile-up


