Investigating endpoint compromise EDR requires turning endpoint telemetry into actionable insights to confirm breaches, assess impact, and contain threats before they spread. In our experience, endpoints often reveal attacker activity long before network logs show anomalies, making them critical for rapid response.
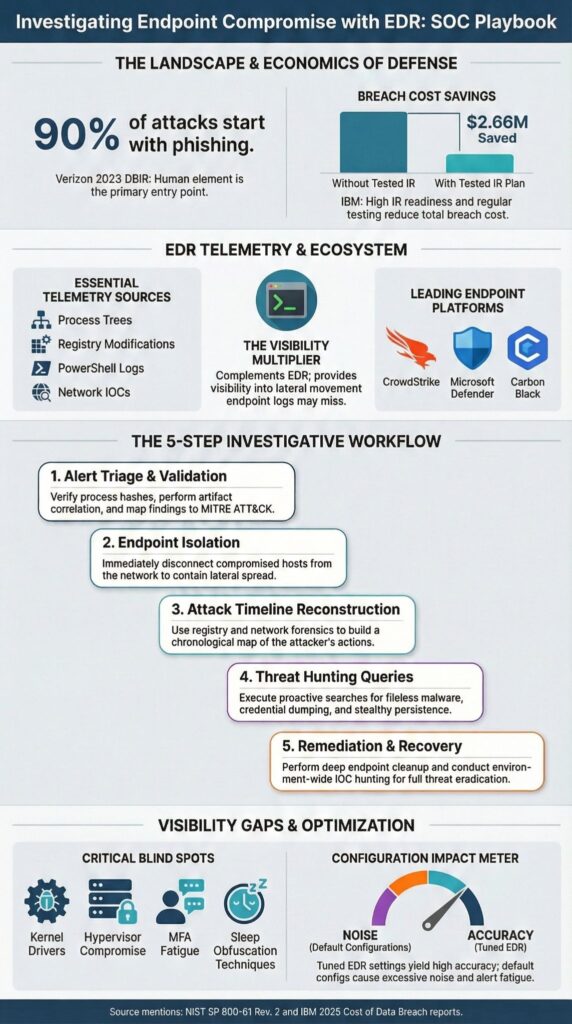
Behavioral analytics, process tree reconstruction, and command-line monitoring help analysts distinguish real compromises from false positives. According to the Verizon 2023 Data Breach Investigations Report, over 90% of breaches start with phishing, highlighting why endpoint visibility is the first line of defense.
Keep reading to learn our step-by-step approach to strengthen your incident response process.
Quick Wins – Investigating Endpoint Compromise
- Effective endpoint compromise investigation depends more on configuration and process than vendor choice.
- Network Threat Detection should complement endpoint detection response to expose lateral movement and pivot activity early.
- Structured triage, telemetry validation, and disciplined containment reduce breach impact and dwell time.
What Is Investigating Endpoint Compromise with EDR?
Investigating endpoint compromise with EDR means leveraging platforms like CrowdStrike and Microsoft Defender to analyze endpoint activity, registry changes, and network connections, allowing us to reconstruct attacker behavior and stop lateral movement before it spreads.
As highlighted by IBM
“Forensics enables remote gathering of forensic information for an investigation, which helps support forensic analysis and reconstruction of an attacker’s activities.” – IBM
We use process tree analysis, command-line forensics, and registry activity monitoring to confirm the scope of a breach and validate malicious actions.
EDR works best as part of a layered defense strategy. While endpoint telemetry is critical, we always correlate findings with network traffic and NetFlow to verify lateral movement and attacker pivots.
Core telemetry sources we rely on include:
- Process creation and parent-child relationships for behavioral reconstruction
- Registry hive and SAM access monitoring for persistence detection
- PowerShell logging and script-based forensics for attack context
- Network IOC extraction from endpoint logs to validate connections
This structured telemetry provides the backbone for thorough endpoint compromise investigations, giving analysts the evidence needed to act confidently and quickly.
How Does the Core EDR Investigation Process Work?
The core EDR investigation process combines alert triage, endpoint isolation, forensic reconstruction, threat hunting queries, and remediation workflows into a repeatable methodology. In our experience, following a structured approach reduces dwell time and improves evidence quality.
Insights from Wikipedia
“…tools primarily focused on detecting and investigating suspicious activities (and traces of such) and other problems on hosts/endpoints.” – Wikipedia
Key steps include:
- Alert Triage and Validation: Analysts verify process hashes, check reputation databases, and review command-line activity.
- Endpoint Isolation: Isolating affected endpoints prevents lateral movement while preserving forensic integrity. This step protects adjacent systems and ensures evidence is not overwritten.
- Timeline Reconstruction: Correlate process trees, registry changes, and network logs to map the attack chain. Persistence indicators often include scheduled tasks and registry Run keys.
- Threat Hunting with Queries: Use EDR search capabilities to uncover fileless malware, PowerShell anomalies, or living-off-the-land execution patterns, helping identify patient zero.
- Remediation and Recovery: Apply endpoint removal, credential resets, and persistence cleanup.
This layered workflow ensures that EDR is used as an investigative engine rather than just an alerting tool, balancing speed with accuracy.
What Are the Most Common EDR Blind Spots?

EDR blind spots often appear in areas where endpoint sensors have limited visibility or inconsistent telemetry.
In our experience, sophisticated attackers exploit gaps in kernel-level process injection detection, hypervisor compromise, and in-memory credential scraping to bypass endpoint controls. Misconfigured or under-resourced agents can leave partial blind zones, which create opportunities for stealthy lateral movement or privilege escalation.
Common blind spots we observe include:
- SAM registry access without alerting – critical system modifications may go unnoticed.
- Sleep obfuscation bypass techniques – malicious activity during sleep or low-power states evades detection.
- Living-off-the-land tool abuse – attackers leverage native utilities like PowerShell or WMI to avoid signature-based detection.
- Alert fatigue management failures – high volumes of low-signal alerts obscure high-risk behaviors, delaying analyst response.
We have seen firsthand that even well-tuned EDR can miss early-stage credential dumping or process injection attempts. That is why we treat Network Threat Detection as a foundational validation layer.
By correlating endpoint telemetry with network activity, anomalous pivot behavior, NetFlow irregularities, and lateral movement attempts can be identified, even when endpoint sensors do not report them.
Why Configuration Matters More Than Vendor Choice
In our experience, the effectiveness of an EDR deployment often depends more on configuration and tuning than the brand itself.
Even the most advanced platform can underperform if critical telemetry is disabled or detection rules are misaligned. Properly tuned systems reduce noise, improve analyst efficiency, and increase detection depth across endpoints.
A simplified comparison illustrates the difference:
| Factor | Well Tuned EDR | Default Configuration |
| Alert Accuracy | High signal clarity | High noise volume |
| Coverage | Full telemetry enabled | Sensor telemetry gaps |
| SOC Efficiency | Reduced alert fatigue | Analyst overload |
| Detection Depth | Behavioral analytics optimized | Minimal anomaly detection |
We’ve seen deployments fail because PowerShell logging was off or endpoint data normalization policies were incomplete. To maximize effectiveness, we focus on:
- Baseline behavior monitoring to spot anomalies early
- Custom detection rules mapped to MITRE ATT&CK endpoint tactics
- Threat intelligence integration for IOC correlation
- Zero trust enforcement to limit lateral movement
When these controls align with disciplined workflow, endpoint threat detection becomes proactive rather than reactive, enabling faster, more confident incident response.
How Do Attackers Bypass EDR Controls?
Attackers often bypass EDR by blending malicious activity into legitimate system behavior, exploiting gaps in telemetry, or abusing built-in tools.
In our field experience, common tactics include LOLBin abuse, reflective DLL injection evasion, sleep obfuscation bypass, and credential dumping targeting memory. These techniques let adversaries operate under the radar of default EDR configurations.
We frequently observe:
- PowerShell or WMI execution with logging disabled prior to attack
- Cobalt Strike beaconing masked through encrypted C2 channels
- Active Directory enumeration preceding domain-wide compromise
- Hypervisor-level attacks bypassing endpoint isolation
- Living off the land EDR abuse to hide lateral movement
Automated alerts help surface unusual activity, but we always combine them with manual investigation to validate intent. Artifact correlation hunting across hosts and pivot analysis using network telemetry often reveals attacks that endpoints alone miss.
By layering EDR with Network Threat Detection, we can detect anomalies like irregular beacon intervals, unusual data exfiltration patterns, or hidden lateral movement. This integrated approach reduces dwell time and strengthens response accuracy.
Our experience shows that organizations relying solely on default EDR settings risk missing subtle but critical attacker behaviors, making layered telemetry and proactive detection essential.
What Does a Practical SOC Triage Checklist Look Like?
Credits : Cloud360 Training
A structured triage checklist is essential for investigating endpoint compromise efficiently, reducing mean time to respond, and improving containment. In our experience, SOC teams that standardize their workflow handle alerts faster, maintain consistency, and reduce human error.
We build our endpoint compromise assessment around repeatable, high-confidence steps:
- Confirm the host’s business criticality and risk exposure
- Identify indicators of user and privileged account compromise
- Review suspicious process tree lineage for anomalous activity
- Extract network IOC artifacts from endpoint logs
- Map behaviors to MITRE ATT&CK endpoint techniques
- Preserve volatile memory dumps and perform disk imaging for forensics
Beyond these steps, we integrate normalized endpoint telemetry into broader XDR and SIEM pipelines. This ensures logs, alerts, and endpoint data align across consoles and monitoring tools.
Consistency is key. When teams follow a structured checklist, they can validate alerts faster, prioritize high-risk incidents, and reduce dwell time.
By combining procedural discipline with layered visibility, from endpoint to network, SOC operations become more predictable, repeatable, and resilient. Confidence gained from structured triage directly translates into faster containment and stronger investigative outcomes.
FAQ
What are the first steps in endpoint compromise investigation?
The first step in an endpoint compromise investigation is to validate the alert through proper SOC alert triage and confirm it within your endpoint detection response console.
You should follow documented initial triage steps and immediately apply an evidence preservation protocol. Perform endpoint telemetry analysis and review suspicious activity monitoring logs to understand the timeline before making any system changes.
How does the EDR triage process reduce alert fatigue?
A structured EDR triage process reduces alert fatigue by prioritizing alerts based on risk and verified indicators. Teams use baseline behavior monitoring and endpoint anomaly detection to separate real threats from normal activity.
Behavioral analytics EDR helps analysts focus on high-confidence signals. Clear escalation paths and defined workflows improve incident response endpoint speed and overall SOC productivity.
How can I detect lateral movement and credential abuse?
You can detect lateral movement detection activity by reviewing remote login events, AD enumeration detection logs, and unusual shared resource forensics patterns. Investigate signs of credential dumping investigation and privileged account compromise.
Combine IOC hunting endpoint queries with network connection triage data. Map findings to MITRE ATT&CK endpoint techniques to support accurate attack chain mapping and pivot detection endpoint confirmation.
When should I perform memory forensics during investigation?
You should perform memory forensics EDR when you suspect fileless malware EDR, process injection detection, or DLL injection detection. Capture a volatile memory dump before shutting down the system.
Use the Volatility framework EDR to analyze suspicious process tree behavior and command line forensics artifacts. This method supports ransomware investigation EDR and validates potential C2 communication detection findings.
How do I assess breach scope and contain the endpoint?
To assess breach scope, conduct a breach scope assessment supported by forensic timeline reconstruction. Use artifact correlation hunting to connect endpoint telemetry with network IOC extraction and exfiltration analysis endpoint results.
Apply containment strategies endpoint such as endpoint isolation techniques while documenting remediation workflows EDR. Confirm process hash verification results and complete persistence removal techniques to prevent reinfection.
Strengthen Endpoint Compromise Investigations with Structured EDR
Investigating endpoint compromise requires more than deploying agents, it demands layered monitoring, disciplined telemetry tuning, and continuous validation. Combining endpoint and network visibility accelerates detection, reduces dwell time, and improves alert management.
Teams that align telemetry with Network Threat Detection gain measurable benefits: faster incident resolution, reduced risk exposure, and stronger zero-trust endpoint maturity.
Structured EDR processes, purple team validation, and proactive threat hunting empower SOCs, CISOs, and analysts to respond confidently, systematically, and with operational resilience, turning reactive endpoint management into a repeatable, high-confidence defense strategy.
References
- https://www.ibm.com/products/qradar-edr/features
- https://en.wikipedia.org/wiki/Endpoint_detection_and_response