Real time network traffic analysis inspects live packets and flows to expose security threats and performance problems immediately. Enterprises have used flow analysis since Cisco introduced NetFlow in 1996 to understand what was truly happening on their links.
We’ve seen networks fail long before dashboards showed a problem, which is why this immediate visibility is critical. This piece explains how it works, where it’s most effective, and how teams apply it today to optimize performance and detect threats faster. Read on to see how modern networks stay observable and secure under real pressure.
Quick Wins – Turning Live Traffic into Insight
- Real-time network traffic analysis provides immediate insight into bandwidth usage, latency, and threats.
- Packet capture and flow analysis serve different roles and scale differently.
- When we use Network Threat Detection, live traffic data becomes actionable instead of reactive.
What Is Real-Time Network Traffic Analysis?
Real-time network traffic analysis inspects live packets or aggregated flows to reveal usage, latency, and threats as they happen, enabling a fast response. It works by observing data crossing switches, routers, and virtual links. Analysts see activity immediately, not hours later from logs. In our early work, this simple shift closed critical blind spots.
The method uses either real-time packet capture (PCAP) or summarized flow records. According to research published via ResearchGate, modern systems often utilize “Apache Kafka and stream processing… using Apache Flink version 1.17” to ensure that the system can “detect threats with high accuracy and low latency, maintaining scalability under high-throughput conditions.”
Beyond raw visibility, this capability is central to threat detection. As explained in the IBM Think Blog on Network Detection and Response:
“NDR tools continuously monitor and analyze network activity and traffic patterns in real time to identify suspicious activity that might indicate a cyberthreat… because NDR solutions monitor both north-south (exit and entry) and east-west (internal) network traffic, they can detect both intrusions at the network perimeter and lateral movement within the network.” – IBM Think Blog
A live view quickly shows what matters:
- Bandwidth patterns and top-consuming devices or applications.
- Abnormal spikes, like a misconfigured job we once saw consuming 40% of a core link in minutes.
- Performance metrics for latency, jitter, and packet loss.
The common goals are performance tuning, capacity planning, and security monitoring. Continuous monitoring like this shortens response times by improving situational awareness.
These insights appear on dashboards that refresh every few seconds, providing immediate visibility into active devices and faster anomaly response. This immediacy fundamentally changes how teams operate.
How Do Packet Capture and Flow-Based Analysis Differ?
Packet capture and flow-based analysis are fundamentally different. PCAP examines every single packet for complete detail, while flow analysis summarizes conversations to handle scale and speed.
You capture packets using span ports or network taps, often relying on specialized tools for capturing network packets to maintain inspection accuracy at higher speeds. This gives you full visibility from layers 2 through 7 for deep inspection. In our own troubleshooting, we still turn to PCAP to diagnose strange protocol errors or sessions that just don’t form correctly.
The practical differences are clear in a few key areas:
- Data depth: PCAP offers full payloads, while flows provide metadata only.
- Resource overhead: Capture needs high CPU and storage; flows use far less.
- Typical use: We use PCAP for debugging and forensics, and flows for ongoing monitoring.
- Scale limit: PCAP struggles at high speeds, but flows are built for large networks.
The distinction becomes clearer in practice.
| Aspect | Packet Capture | Flow-Based Analysis |
| Data depth | Full payload visibility | Metadata summaries only |
| Resource overhead | High CPU and storage | Lower CPU and memory |
| Typical use | Debugging and forensics | Ongoing monitoring |
| Scale limit | Struggles at high speed | Designed for large networks |
Packet capture supports forensic analysis, while flows power real-time dashboards and alerts.
Which Tools Provide Real-Time Network Visibility?
Real-time visibility uses tools from packet analyzers to flow collectors and dashboards, balancing detail, scale, and alerting for your network’s size.
In our work, a visibility stack starts with collection: routers export flows, switches give port stats, and sensors capture packets where necessary. These feeds power dashboards that refresh every second.
Modern platforms focus on real-time dashboards, alerting, and correlation. When we deploy Network Threat Detection, live telemetry feeds directly into anomaly detection and behavioral analytics, so data drives action immediately.
This integration aligns with what the Forbes Technology Council on real-time cyber threat intelligence emphasizes:
“Intelligence on its own isn’t particularly useful. It needs to be integrated, in real time, with a larger platform that delivers a layered cybersecurity posture. Logically, threat intelligence and related analytics are key capabilities for any modern cybersecurity platform, which needs to be able to collect and analyze CTI [Cyber Threat Intelligence] for better security automation.” – Forbes Technology Council
Teams usually judge tools on a few key points:
- Packet inspection offers deep protocol insight but is resource-intensive.
- Flow analytics scales to large networks but lacks payload details.
- Dashboards enable fast comprehension but depend entirely on the quality of the underlying data.
Teams typically evaluate tools based on three dimensions.
| Capability | Strength | Limitation |
| Packet inspection | Deep protocol insight | Resource intensive |
| Flow analytics | Scales to large networks | Limited payload detail |
| Dashboards | Fast comprehension | Dependent on data quality |
The strongest setups integrate packet data, flows, and alerts into a single workflow. That integration is where real-time analysis becomes operational instead of observational.
What Techniques Enable Scalable Real-Time Monitoring?

Scalable real-time monitoring mixes flow protocols, smart sampling, and efficient storage to keep latency down while maintaining useful visibility.
Flow protocols like NetFlow, IPFIX, and sFlow are the foundation, typically integrated through structured data sources collection pipelines that unify telemetry before analysis.
But sampling isn’t the whole solution. Time-series storage systems had to evolve to handle the flood of metrics efficiently. Visualization layers then turn those metrics into the real-time dashboards operators rely on.
Several techniques make this work:
- Flow exporters on routers and switches.
- Sampling rates carefully tuned for different link speeds.
- Time-series databases optimized for rapid data ingestion.
- Threshold alerts linked directly to established baseline behavior.
Together, these pieces enable effective anomaly detection without crushing your infrastructure. This approach is what keeps analysis fast and actionable, even as a network grows. Our own tools apply these principles, using threat models to focus sampling and baselining on the highest-risk network segments.
What Are the Primary Use Cases for Real-Time Traffic Analysis?
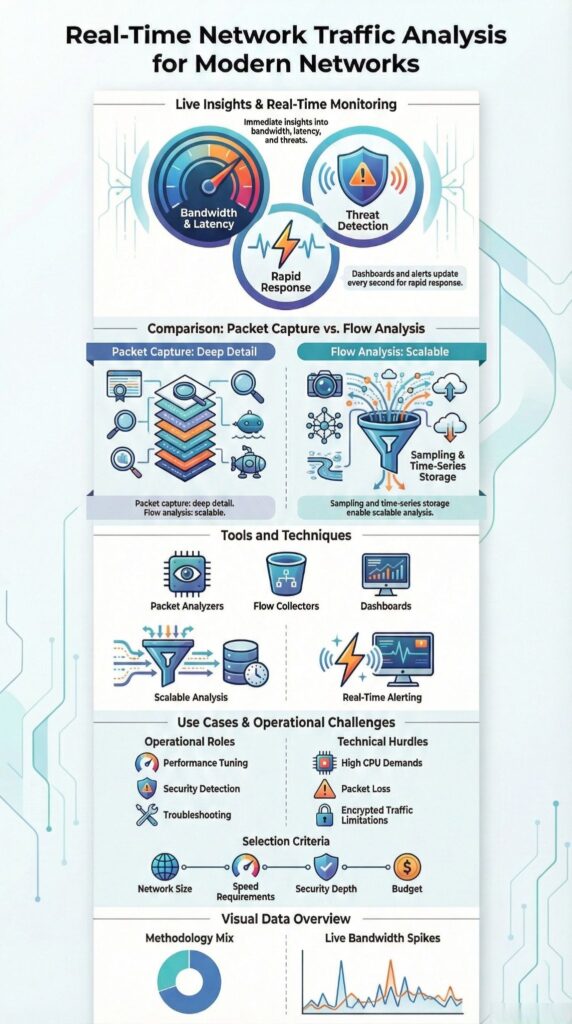
The main uses for real-time traffic analysis are performance tuning, security detection, and fast troubleshooting.
Performance teams watch live data to spot bandwidth hogs and streaming issues. In one deployment, we saw VoIP quality drop suddenly; the live dashboard immediately showed a spike in unplanned multicast traffic as the cause.
For security, real-time analysis detects DDoS patterns, intrusion attempts, and data exfiltration. Cloudflare’s 2023 research noted DDoS attacks surpassing 2 Tbps, where a detection delay is simply too expensive.
Cloud environments like AWS have extended these uses. Services such as VPC Flow Logs add rich metadata to flow data, enabling better cloud and hybrid network analytics.
Troubleshooting gets the fastest benefit. Live data cuts down resolution time by showing latency, packet loss, and protocol activity together in one view.
The core applications are straightforward:
- Performance optimization by identifying top-consuming devices and applications.
- Security event correlation to support proactive threat hunting.
- Faster troubleshooting with immediate, contextual network data.
In our Network Threat Detection work, these uses come together. It lets teams move from a reactive stance to a coordinated response, guided by the specific risks outlined in our threat models.
What Challenges Limit Accuracy at High Network Speeds?
Credits : INFOSEC TRAIN
Accuracy falls apart at high network speeds because of packet loss, CPU bottlenecks, and storage limits.
High-speed links show the weakness of software-based inspection. Standard servers often fail above 10 Gbps. Intel’s own performance data shows packet drops spike without specialized hardware acceleration.
Deep packet inspection gets very costly at this scale. Storage is another hurdle, full capture fills disks in no time. We’ve watched ring buffers on busy links overwrite crucial evidence in just minutes.
Modern network complexity adds more noise. Virtual overlays, encrypted traffic, and container networking obscure the clear views we used to have. ENISA reports that over 80% of enterprise traffic is now encrypted, which hides content from simple inspection.
A few factors usually create the bottleneck:
- Packet loss when trying to capture at full wire speed.
- CPU exhaustion from running deep inspection.
- Alert fatigue caused by overly noisy telemetry data.
Hybrid designs help by mixing selective, high-fidelity packet capture with broader, flow-centric monitoring. Our approach uses threat models to decide precisely where that detailed capture is needed, so we can maintain accuracy without breaking the infrastructure.
FAQ
What is real time network traffic analysis and why is it important?
Real time network traffic analysis examines network activity as it happens instead of relying on historical logs. It uses network traffic monitoring, real-time packet capture, and flow analysis to track bandwidth usage, latency, jitter, and packet loss.
This approach allows teams to detect problems immediately, maintain stable performance, and prevent small issues from becoming outages.
How does real time traffic monitoring reveal abnormal network behavior?
Real time monitoring compares live traffic against established baseline patterns. Anomaly detection highlights unusual bandwidth spikes, unexpected top talkers, or unfamiliar protocols.
These changes often indicate security threats, misconfigurations, or application failures. Threshold alerts ensure teams receive timely notifications, enabling faster investigation and reducing the risk of prolonged service disruption.
What types of data are analyzed during real time traffic inspection?
Real time analysis relies on packet inspection, flow records, and metadata extraction. Full packet capture supports deep packet inspection, while flow data explains communication paths and volume.
Application layer analysis clarifies protocol hierarchy, HTTP traffic breakdown, and DNS query behavior. Together, these data sources provide accurate context for troubleshooting and performance assessment.
How does real time traffic analysis improve performance and capacity planning?
Continuous monitoring enables precise bandwidth usage tracking, latency measurement, and QoS monitoring.
Time-series data reveals recurring congestion patterns and growth trends. These insights support informed capacity planning and structured troubleshooting workflows. By identifying bottlenecks early, teams reduce mean time to resolution and ensure the network scales reliably with demand.
How does real time traffic analysis support security investigations?
Real time analysis strengthens security investigations by correlating traffic behavior with potential threats.
It helps identify intrusion attempts, data exfiltration activity, and malware indicators through behavioral analytics and encrypted traffic analysis. Immediate visibility supports forensic analysis and threat hunting, allowing security teams to respond quickly and limit the impact of active incidents.
Real-Time Network Traffic Analysis in Practice
Real-time network traffic analysis works when live data drives action, not just fills a screen. Mixing packet inspection, flow analysis, and behavioral context gives teams the clarity they need under pressure. As networks get faster and more traffic becomes encrypted, this method stays critical for maintaining visibility and building resilience.
To implement this approach with integrated threat intelligence, explore the features of our Network Threat Detection platform.
References
- https://www.ibm.com/think/topics/ndr
- https://www.forbes.com/sites/forbestechcouncil/2018/05/22/real-time-cyber-threat-intelligence-is-more-critical-than-ever/