Using metadata for threat hunting means analyzing structured network, endpoint, and cloud signals to detect adversary behavior without inspecting full packet payloads.
Even when over 80% of enterprise traffic is encrypted via TLS, according to the Google Transparency Report, metadata fields like file hashes, IP addresses, process lineage, and session patterns reveal lateral movement, command and control beaconing, and suspicious activity.
Modern attackers leverage encryption and short dwell times, making payload-only approaches insufficient. We’ve seen lightweight metadata surface threats faster than traditional deep packet inspection. To design scalable, defensible hunting workflows across all environments, keep reading for practical guidance.
Quick Wins – Scaling Threat Hunting with Metadata
- Threat hunting metadata enables scalable analysis across encrypted traffic, endpoints, and cloud environments.
- Hypothesis driven hunts mapped to MITRE ATT&CK reduce false positives and improve dwell time reduction.
- Combining network, endpoint, and cloud metadata produces higher confidence detections than siloed analysis.
What Is Metadata in Threat Hunting and Why Does It Matter?
Metadata captures contextual details, file hashes, IP addresses, timestamps, and process lineage, that let security teams hunt threats at scale without digging into full payloads.
We rely on NetFlow records, Zeek logs, Sysmon events, JA3 fingerprints, user agent strings, and timestamp anomalies to understand behavior without storing every packet. Metadata like source IP, destination port, byte counts, and TLS fingerprints frequently exposes patterns attackers try to hide.
In a recent analysis by Metadata Pilot Planning Workshop (National Security at Virginia Tech / federal cybersecurity)
“By rapidly analyzing this data with a variety of existing and emerging cybersecurity tools, detection and incident response, threat hunting, and damage assessments could be accelerated.” – Virginia Tech
Key benefits we see in metadata-first hunting include:
- Faster indexing than raw logs or full PCAP
- Lower storage costs with compact datasets
- Rapid pivoting across network, endpoint, and cloud data
- Reduced reliance on signature-based detection
From our experience building Network Threat Detection, starting with metadata scales efficiently, accelerates investigations, and surfaces attacker behavior that would otherwise go unnoticed.
How Do Metadata Pivots Work in MITRE ATT&CK–Driven Hunts?

Metadata pivots let hunters move across datasets to validate suspicious behavior without relying on signatures. Starting with a MITRE ATT&CK tactic, we define what abnormal looks like in structured fields such as process lineage, LDAP activity, or ticket volume.
For example, Kerberoasting spikes show unusual service ticket requests in Windows event logs and Sysmon events. DCSync attempts often expose LDAP replication metadata from non-domain controllers. These patterns create natural pivot points for investigation.
As noted by NSA | Manage Cloud Logs for Effective Threat Hunting (Defense.gov)
“Analyze logs … normalize and enrich them with context and metadata, such as IP addresses, user identities, and timestamps. … Analyze logs … investigate and analyze the root cause of an incident and identify any suspicious or anomalous activity.” – NSA
A typical workflow includes:
- Forming a hypothesis aligned to MITRE ATT&CK tactics
- Querying structured fields like process lineage or network metadata
- Correlating across endpoint telemetry, network flows, and logs
- Validating statistical outliers against baseline behavior
In our experience, we often pivot from a suspicious IP in NetFlow records to DNS query logs, then into endpoint metadata like parent-child process chains.
Which Metadata Sources Provide the Most Hunting Value?

Metadata from network, endpoint, cloud, and firewall sources uncovers different slices of attacker behavior, and aligning these feeds through disciplined data sources collection practices strengthens normalization, enrichment, and cross-layer correlation.
In our experience, combining these sources and correlating events across layers improves detection accuracy and reduces false positives. Normalization and enrichment turn raw logs into actionable signals.
Key sources and use cases include:
| Metadata Source | Example Tool | Key Fields | Primary Use Case |
| Network | Zeek | SrcIP, DstPort, JA3 hashes | C2 beaconing detection |
| Endpoint | Elastic Security | ParentHash, ProcessID, command line arguments | Living off the land detection |
| Cloud | Microsoft Defender | ResourceID, API calls | Privilege escalation |
| Firewall | Palo Alto Panorama | UserID, AppID | Victim segmentation |
Practical insights we rely on include:
- Beaconing patterns in network flows, often every 60 seconds
- Rare or suspicious process executions in endpoint telemetry
- Unusual registry changes and PowerShell activity
- Anomalous cloud API calls or resource modifications
When we integrate these feeds into Network Threat Detection, metadata normalization, field extraction, and cross-source correlation are essential. Behavior alignment across network, endpoint, and cloud layers increases detection confidence, reduces false positives, and highlights actionable threats before they escalate.
How Can KQL Be Used for Advanced Metadata Hunting?
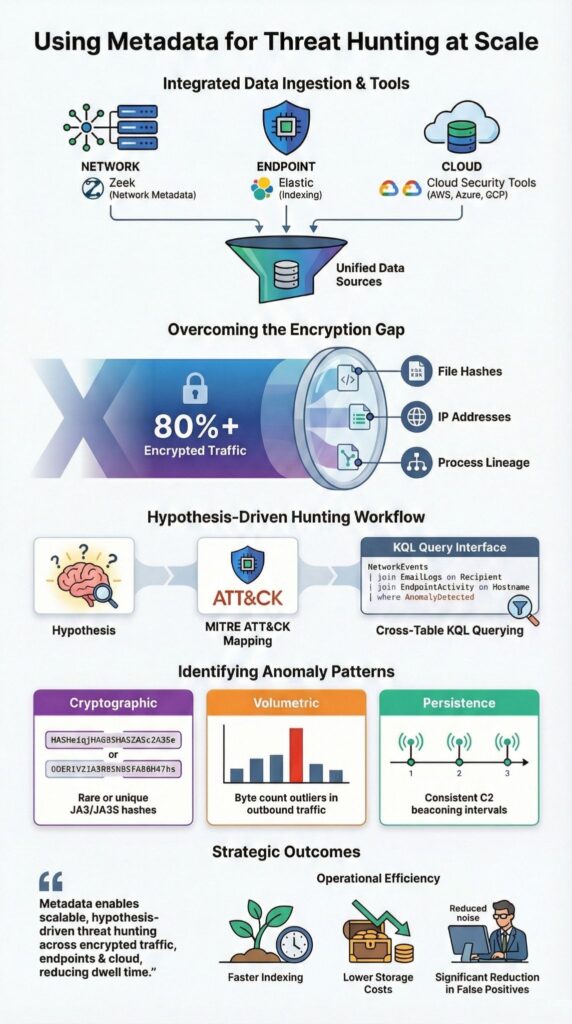
KQL allows us to join metadata tables like DeviceNetworkEvents and EmailUrlInfo, enriching investigations with behavioral context and threat intelligence without manual log exports. In large enterprises, terabytes of daily logs can overwhelm analysts unless queries are structured, precise, and optimized for performance.
Within Azure Sentinel and Microsoft Defender, we leverage KQL for advanced hunting across network, endpoint, and email metadata. A typical workflow includes:
- Spotting suspicious IPs or domains in network connection metadata
- Joining with email metadata to identify phishing or malicious links
- Filtering by threat intelligence verdict and severity score
- Pivoting into endpoint telemetry for parent-child process activity
In practice, we often correlate URL reputation, file hashes, and threat intelligence feeds in a single query, allowing analysts to surface subtle communication patterns in metadata that indicate coordinated phishing, lateral movement, or beaconing.
This approach reduces manual triage, accelerates response times, and ensures analysts focus on actionable signals rather than noise.
Metadata joins enable exactly that, linking signals across layers quickly, letting hunters validate hypotheses, uncover lateral movement, beaconing, or compromise indicators, and prioritize remediation before incidents escalate.
How Do Zeek and Elastic Support PCAP Derived Metadata in OT and ICS Environments?
Zeek converts PCAP captures into structured metadata, while Elastic provides scalable indexing, search, and behavioral analytics for OT and ICS threat hunting. In industrial networks, full deep packet inspection can disrupt sensitive control systems, so lightweight metadata extraction is both safer and more practical.
Zeek produces logs like conn.log, dns.log, and ssl.log from PCAP, capturing TLS fingerprints, JA3 hashes, DNS queries, and flow durations without storing payloads, effectively utilizing network metadata session records to preserve forensic value without full packet retention.
Elastic then indexes these fields, enabling rapid search, anomaly detection, and statistical baselining.
From our experience deploying Network Threat Detection in OT environments, we focus on:
- Detecting SMB anomalies on unusual ports
- Identifying rare protocol usage in microsegmented networks
- Spotting byte count outliers for exfiltration detection
- Applying statistical baselining to industrial protocol flows
OT traffic tends to be predictable. When deviations appear, they stand out clearly in metadata-only analysis. This makes lightweight, flow-based threat hunting both scalable and operationally safe, letting us monitor ICS networks without risking system stability.
What Are Common Anomaly Detection Patterns in Metadata?
Credits : Progress Flowmon
Metadata-based anomaly detection works by first establishing a baseline of normal behavior and then flagging deviations that stand out statistically, such as rare JA3 hashes, abnormal byte counts, or unexpected protocol usage. In practice, analysts focus on the top 1–5% of deviations from the baseline to balance sensitivity with noise reduction.
We’ve seen rare JA3 hashes indicate custom malware, while unusual IP geolocation shifts often reveal compromised VPN accounts. Consistent C2 beaconing intervals with identical byte counts frequently point to automated command channels.
Common hunting patterns we track include:
- Baseline average bytes per flow and flag outliers
- Detect rare process execution and unusual parent-child relationships
- Identify RDP brute force metadata spikes
- Monitor unusual data volume patterns for potential exfiltration
Machine learning techniques like isolation forests or unsupervised clustering can help at scale, but in our experience, simple behavioral analytics grounded in statistical baselines remain the most reliable starting point. By layering ML on top of clear metadata pivots, we achieve both speed and accuracy in threat detection.
FAQ
What is threat hunting metadata and why does it matter?
Threat hunting metadata refers to structured contextual data about system and network activity rather than full packet payloads. It includes network connection metadata, endpoint telemetry, Windows event logs, and cloud trail logs.
By analyzing threat hunting metadata, analysts can identify lateral movement indicators, rare process execution, and C2 beaconing patterns at an early stage. This metadata only analysis supports lightweight hunting and scalable threat detection without excessive storage requirements.
How does network flow analysis support proactive hunting?
Network flow analysis relies on NetFlow records, IPFIX records, and sFlow analysis to summarize traffic behavior across networks.
With accurate PCAP metadata extraction and a properly configured flow exporter, analysts can detect byte count outliers, port scanning patterns, and potential exfiltration detection signals. These flow summaries also expose suspicious IP geolocation changes and abnormal TLS fingerprints, which enable proactive hunting before attackers expand access.
Which endpoint logs are most useful during hunts?
Effective hunts depend on endpoint telemetry such as Sysmon events, process lineage tracking, parent child processes, and command line arguments. PowerShell logging, ETW events, and registry keys monitored provide visibility into living off the land techniques.
File creation events and file hashes, combined with hash reputation checks and IOC matching, validate suspicious activity. These data sources strengthen privilege escalation metadata analysis and investigative confidence.
How can hunters detect advanced persistence and credential abuse?
Hunters detect credential abuse by analyzing Kerberoasting detection patterns, DCSync attacks, and RDP brute force metadata within Windows event logs and VPN log analysis results.
SMB anomalies and lateral movement indicators often appear in unusual network connection metadata. Timestamp anomalies and domain generation algorithms assist with DGA detection. Applying MITRE ATT&CK mapping within a hypothesis driven hunting approach increases detection precision.
How do analytics and big data improve hunting maturity?
Behavioral analytics and UEBA metadata enhance anomaly detection rules by identifying machine learning anomalies through unsupervised clustering and isolation forests.
Analysts perform retrospective analysis using data lake queries, Spark SQL hunting, or BigQuery threat hunts across large datasets. Correlation rules, statistical baselining, and SIEM enrichment strengthen threat hunting maturity. These practices enable structured big data threat hunting supported by consistent metadata normalization.
Measuring Using Metadata for Threat Hunting Effectiveness
Metadata-driven threat hunting focuses on outcomes rather than raw alert volume. Teams should track validated threats, campaign attribution, and reductions in detection time.
In our experience, metadata pivoting frequently uncovers lateral movement before external alerts, providing early warning and actionable intelligence. This approach improves dwell time, enhances risk scoring, and leverages SOAR automation to turn structured metadata into a scalable, proactive defense.
Explore how we approach scalable Network Threat Detection in your environment.
References
- https://nationalsecurity.vt.edu/content/nationalsecurity_vt_edu/en/about/news/2023/vtnsi-publishes-two-workshop-reports-on-value-of-capturing-metadata-on-network-traffic-to-enhance-threat-detection.html
- https://media.defense.gov/2024/Mar/07/2003407864/-1/-1/0/CSI_CloudTop10-Logs-for-Effective-Threat-Hunting.PDF


