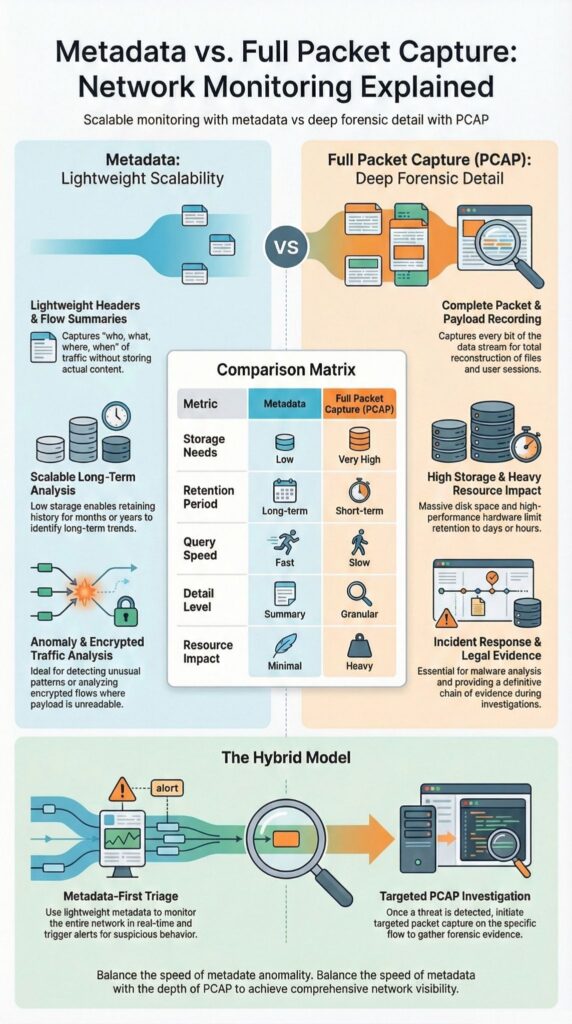
Metadata vs full packet capture serve complementary roles in network security. Metadata enables scalable monitoring, letting teams track traffic patterns, detect anomalies, and maintain visibility without storing every packet. Full PCAP provides complete forensic detail, essential for reconstructing attacks and performing deep protocol analysis.
Modern security operations rely on tools like NetFlow, IPFIX, and Wireshark to balance storage, speed, and investigative depth.
The National Institute of Standards and Technology (NIST) emphasizes that visibility is critical for incident detection and response. Keep reading to understand the tradeoffs, differences, and how to apply each approach in building smarter Network Threat Detection strategies.
Quick Wins – Metadata First, PCAP When Needed
- Metadata supports scalable, long term network traffic analysis with significantly lower storage and CPU overhead.
- Full packet capture enables complete payload reconstruction for incident response and legal evidence collection.
- Most mature teams use a hybrid model, prioritizing Network Threat Detection through metadata first, then escalating to targeted PCAP.
What Is Metadata in Network Monitoring?
Metadata captures packet headers and flow summaries, IP addresses, ports, timestamps, and byte counts, without storing full payloads, often cutting storage needs by up to 90% compared to full PCAP. It focuses on structured flow data, using technologies like NetFlow v9, sFlow, and IPFIX to export compact records summarizing communication between endpoints.
The value of metadata is also validated by government standards. As noted in NIST Special Publication 800‑150, Guide to Cyber Threat Information Sharing:
“Network flow data contains information such as: • Source IP address … Port and protocol information, • Byte counts, and • Timestamps.” – NIST
This confirms that the metadata captured from flows provides meaningful insight without needing full packet payloads, supporting scalable monitoring and threat detection.
Key characteristics we rely on include:
- Lightweight monitoring across distributed networks
- Fast Elasticsearch indexing and low search latency
- Long-term retention measured in months
- Efficient bandwidth monitoring and baseline tracking
At Network Threat Detection, metadata often forms the starting point for scalable behavioral analytics, UEBA workflows, and machine learning-driven flow analysis, providing actionable insights while keeping CPU and disk usage low.
What Is Full Packet Capture (PCAP)?

Full packet capture records every packet, including headers and payloads, enabling deep forensic reconstruction. On high-speed links, this can generate terabytes of data daily.
The tradeoff of full PCAP versus metadata is emphasized by educational research. As described in Less is More with Intelligent Packet Capture (SEI / Carnegie Mellon University):
“These alternatives provide forensic value and use significantly less disk space than full packet capture, but lack the complete packet payloads needed to fully confirm the presence of malicious activity on the network.” – Carnegie Mellon University
This highlights that while full PCAP gives complete forensic detail, it comes with significant storage and resource costs compared to metadata-based monitoring.
Full capture provides capabilities we rely on for advanced investigations:
- Deep packet inspection (DPI)
- File carving and malware extraction
- Full session reconstruction
- Detailed forensics and evidence collection
From our experience, continuous capture without filtering quickly strains disk space, compression, and indexing. In high-throughput environments, circular buffers and selective retention are often necessary within 24 to 72 hours to keep operations sustainable while supporting threat modeling and risk analysis workflows
How Do Metadata and Full PCAP Compare Side by Side?

Metadata focuses on efficiency and scalability, supported by structured metadata session records, while full PCAP delivers complete forensic detail and payload visibility.
In most enterprise SOCs, metadata covers roughly 90% of daily monitoring needs, with PCAP reserved for escalations. This aligns with operational feedback from Security Onion users and broader security forums.
| Aspect | Metadata | Full Packet Capture |
| Storage | Low, headers and flow records only | High, full payload retention |
| Retention | Months to years | Days to weeks |
| Query Speed | Fast indexed searches | Slower reconstruction workflows |
| Detail | Communication patterns and trends | Complete payload reconstruction |
| Resource Impact | Minimal CPU and disk | High CPU, disk, bandwidth |
We’ve found that metadata supports key operational benefits:
- Rapid query performance for large datasets
- Faster alert triage and incident prioritization
- Efficient correlation rules across distributed networks
- Scalable monitoring even in high-volume or encrypted traffic
Full PCAP remains critical when packet reassembly, fragmentation handling, or deep protocol decoding is required, though it comes with higher CPU, disk, and storage costs.
At Network Threat Detection, programs that lead with metadata achieve sustained real-time monitoring, allowing our threat models and risk analysis tools to detect patterns and threats effectively without overwhelming infrastructure.
When Does Metadata Make More Sense?
Metadata is ideal for broad anomaly detection, encrypted traffic analysis, and long-term retention across distributed environments, particularly when aligned with disciplined data sources collection practices.
With over 90% of web traffic encrypted, payload inspection alone often leaves blind spots. We’ve seen that relying on header-level indicators, like JA3 fingerprints, TLS metadata, and flow duration, can reveal C2 communication, beaconing, and exfiltration patterns without decrypting content.
Two realities shape modern monitoring. First, HTTPS inspection can add latency and privacy concerns. Second, structured metadata provides actionable insights while respecting data minimization principles. Metadata is particularly effective in:
- Identifying consistent 60-second beacon intervals
- Detecting abnormal byte count spikes
- Spotting suspicious destination IP clusters
- Recognizing TOR traffic, VPN use, or proxy connections
At Network Threat Detection, we rely on metadata-driven baselining, entropy analysis, and deviation scoring to detect DNS tunneling or domain generation algorithms without touching payloads.
For teams focused on scalable Network Threat Detection, metadata delivers coverage across cloud, on-premises, IoT, and OT environments, enabling actionable threat intelligence while keeping operational overhead low.
When Is Full Packet Capture Necessary?
Credits : SharkFest Wireshark Developer and User Conference
Full PCAP is required when precise payload reconstruction is needed for breach validation, malware analysis, or legal defensibility, especially when detailed session data generation is necessary to validate attack timelines.
During active incident response, ambiguity can slow containment. Analysts often need to reconstruct sequence numbers, verify ACK tracking, calculate RTT, or extract files transferred during suspected exfiltration.
Full capture is particularly valuable for:
- Reverse engineering malware traffic
- Confirming sensitive data leakage
- Investigating insider threats
- Supporting regulatory or legal evidence
In ICS and OT environments, PCAP supports analysis of Modbus, DNP3, and Profinet traffic, which may not be fully represented in exported flow records.
We’ve used selective, triggered recording tied to high-severity alerts so payload capture activates only when deviation scoring exceeds defined thresholds. This method preserves forensic depth while limiting disk and CPU impact.
Continuous full capture across large enterprises introduces high resource demands, packet broker requirements, and scaling challenges.
In our experience, most teams benefit from selective deployment rather than universal capture, allowing us to maintain actionable threat modeling, risk analysis, and operational efficiency without overwhelming infrastructure.
FAQ
What is the difference between metadata vs PCAP in practice?
Metadata vs PCAP differs in scope and depth of visibility. Metadata relies on packet headers and flow data, including source IP, destination IP, source port, destination port, protocol type, timestamp, byte count, and packet count.
Full packet capture stores packet payloads in addition to headers. Metadata supports lightweight monitoring and better storage efficiency, while full PCAP enables packet reassembly, protocol decoding, and detailed application layer analysis.
When should I choose flow data over full packet capture?
Flow data such as NetFlow, sFlow, IPFIX, NetFlow v9, and IP flow information export is effective for bandwidth monitoring, anomaly detection, and traffic baselining.
It records flow duration, AS numbers, ToS, DSCP, input interface, and output interface with lower resource overhead. Full PCAP is more suitable for digital forensics and malware analysis, but it significantly increases CPU usage and disk space requirements.
Can metadata support incident response and threat hunting?
Metadata extraction can support incident response, threat hunting, and network forensics when implemented correctly.
Analysts can identify C2 communication, lateral movement, DNS tunneling, HTTP tunneling, and data exfiltration patterns using session data and bidirectional flows. Techniques such as JA3 fingerprints, TLS metadata, GeoIP mapping, entropy analysis, and beaconing detection help reduce false positives during alert triage without storing encrypted payloads.
What are the limitations of full PCAP in large networks?
Full PCAP limitations become clear in high-speed capture environments such as 100Gbps networks.
Continuous capture increases disk space consumption and creates challenges for indexing speed, search latency, and query performance. Techniques such as packet slicing, payload truncation, compression techniques, circular buffers, and selective capture can reduce the impact. However, long-term retention and scalability remain more difficult than header-only analysis.
Is a hybrid approach better for modern network traffic analysis?
A hybrid approach often provides balanced visibility and operational efficiency. Flow exporters connected to network taps, SPAN ports, or ERSPAN generate flow records for real-time monitoring, while triggered recording preserves full packets during specific events.
This model supports retrospective analysis, forensic timelines, performance troubleshooting, and root cause analysis while addressing privacy concerns and enabling data minimization.
Metadata vs Full Packet Capture: Choosing the Right Strategy
Most mature programs use metadata for continuous monitoring and selective PCAP for high-risk segments. Metadata is ideal for scalable retention, low storage overhead, and ongoing traffic analysis, while full PCAP is reserved for confirmed incidents, malware analysis, or legal evidence.
At Network Threat Detection, starting with metadata provides broad coverage and fast anomaly detection, with PCAP filling investigative gaps. Explore how to operationalize intelligent Network Threat Detection in your environment
References
- https://nvlpubs.nist.gov/nistpubs/specialpublications/nist.sp.800%E2%80%91150.pdf
- https://www.sei.cmu.edu/library/less-is-more-with-intelligent-packet-capture/