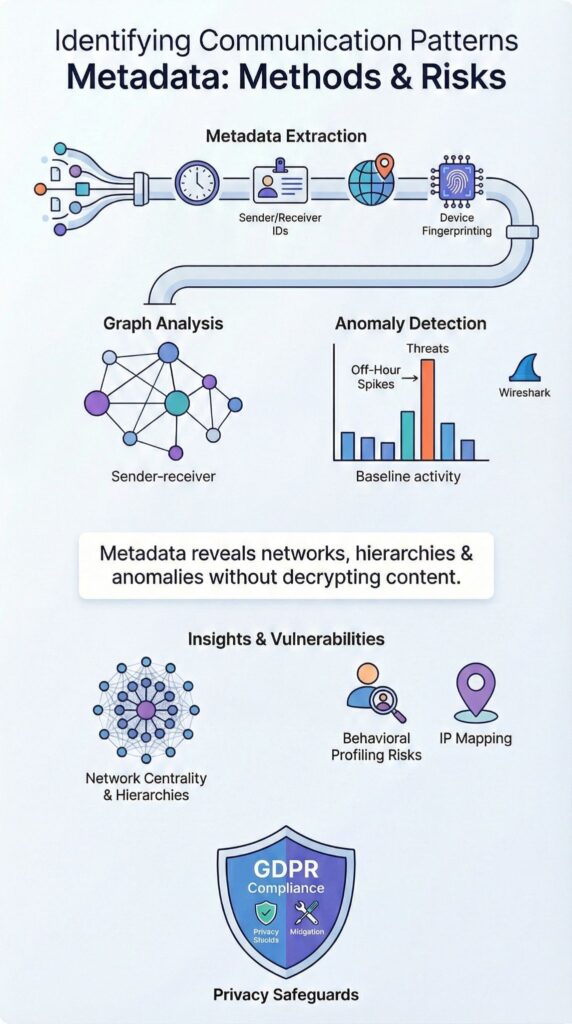
Communication patterns metadata captures non-content signals such as timestamps, sender and receiver IDs, IP addresses, and message frequency to reveal behavioral structures without accessing message bodies. Analysts have demonstrated that pattern data alone can map networks at large scale, showing relationships and activity clusters without reading any content.
Reporting from The Guardian highlighted how bulk metadata collection mapped millions of connections after the 2013 NSA disclosures. Understanding timing, context, and correlation turns metadata into actionable insight. Keep reading to learn how communication patterns metadata works, where it is applied, and how organizations can leverage it responsibly.
Quick Wins – Spotting Threats Through Metadata Patterns
- Identifying communication patterns metadata reveals networks, hierarchies, and anomalies without decrypting content.
- Security teams rely on Network Threat Detection, graph analytics, and anomaly detection metadata to flag insider threats and C2 communication signatures.
- Even encrypted traffic exposes behavioral fingerprints, raising privacy and compliance considerations under GDPR.
What Is Communication Metadata and What Can It Reveal?
Communication metadata captures non-content interaction data, exposing behavioral, relational, and temporal patterns without revealing message bodies.
It includes timestamps, sender and receiver identifiers, IP geolocation, protocol signatures, and device fingerprints, structured through disciplined NTD data sources collection methodologies that normalize telemetry across flow logs, DNS records, and endpoint events.
In our enterprise investigations, we’ve seen simple sender-receiver graphs reveal more than expected. Peak hour analysis and message volume trends often expose reporting lines or hidden coordination channels, even without reading message text.
Key metadata elements we focus on include:
- Message volume over time and timestamp clustering
- Directional flow analysis and reciprocity metrics
- Device type, IP geolocation, and protocol signatures
- Session duration and reconnection frequency
When mapped with tools like Wireshark or Neo4j graph databases, these elements form attribute-rich networks.
We apply centrality measures such as betweenness and eigenvector metrics to uncover influential nodes and hidden structures. This approach makes communication metadata central to threat modeling, digital forensics, and social network analysis, providing actionable insight without exposing content.
How Are Communication Patterns Identified from Metadata?

Analysts identify communication patterns by aggregating timestamps, frequency distributions, network logs, and contact graphs to detect anomalies and behavioral shifts. First, time-based signals are analyzed.
We perform peak hour analysis and time series decomposition to spot unusual bursts. For example, a 40 percent spike in off-hours activity often signals lateral movement or insider threats.
Next, contact networks are visualized. Using Neo4j, nodes and weighted edges reveal centrality and clustering. In one case we handled, a single account showed abnormal betweenness centrality across five departments, highlighting a potential insider threat before exfiltration occurred.
Core identification workflow includes:
- Metadata extraction from NetFlow and sFlow
- Log parsing via ELK stack or Splunk
- Supervised pattern labeling and unsupervised anomaly clustering
- Flow-based analysis for C2 communication signatures
As highlighted by Australian Signals Directorate & multiple national CSIRTs / gov
“Centralised event log access and correlation … enable network defenders to make agile and informed decisions based on prioritisation of alerts and analytics.” – Australian Signals Directorate
At Network Threat Detection, we operate on encrypted traffic metadata without payload inspection. Flow analysis quickly surfaces C2 intervals, while graph and statistical modeling refine attribution using stochastic block and latent space models.
What Are Common Use Cases for Metadata Pattern Analysis?
Metadata pattern analysis powers cybersecurity monitoring, insider risk detection, social network mapping, and digital forensic reconstruction. In cybersecurity monitoring, we track anomalies in flow metadata to detect spam campaigns, botnet coordination, and lateral movement.
For insider threat detection, we focus on after-hours login spikes and cross-department communication bursts. Combining peak hour analysis with session duration stats frequently uncovers policy violations before sensitive data leaves the network.
Key social network and forensic applications include:
- Mapping communication graphs to identify influencers and gatekeepers via centrality measures
- Detecting hidden clusters with community detection and link prediction
- Reconstructing timelines from NetFlow metadata and endpoint telemetry
- Correlating logs to reduce suspect devices from thousands to a handful
Insights from Microsoft Expanded Cloud Logs Implementation Playbook (CISA gov)
“This event provides a record of outgoing communications … and associated metadata … This event helps to identify communication patterns and establish timelines in threat actor interaction.” – CISA gov
In our experience, these approaches turn communication patterns metadata into actionable intelligence. They provide measurable outcomes for threat detection, risk assessment, and forensic investigations, supporting both operational decisions and strategic security planning.
How Do Chatbots and Platforms Use Metadata Patterns?
Chatbots and platforms leverage metadata patterns like interaction timing, phrasing trends, and session signals to improve responses, while real-time inference differs from persistent surveillance. We’ve observed that most systems rely on prompt engineering metadata and user intent clustering within active sessions rather than long-term storage of identities.
User discussions on Reddit in 2025 highlighted concerns about behavioral profiling, noting filler phrase detection and style shifts.
In practice, session metadata such as duration, device sync, and conversation context informs optimization without retaining full identity graphs, mirroring how network metadata session records are correlated in security environments to model behavior without inspecting payloads
Key distinctions we emphasize include:
- Real-time contextual inference versus long-term storage
- Normalizing chat logs for model improvement
- Metadata signing outputs to ensure integrity
- Conversation memory active only when enabled by user settings
Through controlled testing and prompt research playbooks, we’ve seen that apparent rapport-building signals are probabilistic, not persistent identity markers. Still, cross-platform metadata traces and federated learning models raise privacy considerations, underscoring the need for careful handling of session and behavioral metadata at scale.
What Tools Are Used to Visualize and Detect Metadata Patterns?

Analysts turn metadata into actionable insight using packet analyzers, graph databases, and SIEM platforms. In our experience, combining endpoint telemetry, flow records, and anomaly detection engines helps security teams monitor networks of 100+ employees efficiently and detect suspicious patterns early.
| Tool | Primary Function | Best For |
| Wireshark | Packet capture analysis | Packet level inspection and protocol signatures |
| Neo4j | Graph database modeling | Contact network visualization and centrality measures |
| ELK Stack | Log aggregation | Metadata extraction pipelines |
| SIEM platforms | Correlation rules | Threat hunting metadata |
These tools support structured analyzing connection logs insights workflows that prioritize :
- JA3 hashes and TLS fingerprint detection
- DNS tunneling pattern identification
- HTTP header anomalies and user agent monitoring
- Temporal network dynamics modeling
We recommend starting with Network Threat Detection for flow-based analysis across encrypted traffic metadata.
From there, graph enrichment and attribute-rich network modeling, including exponential random graph models or VAR networks, can deepen understanding. Visualization remains critical: a well-structured sender-receiver graph often highlights risk faster than thousands of raw log lines.
What Privacy Risks Arise from Identifying Communication Patterns Metadata?
Credits : cPacket
Even without accessing message content, metadata can reveal identities, relationships, and behavioral fingerprints that may qualify as personal data under GDPR.
We’ve seen firsthand how analysis of timestamp clustering and weighted edges can uniquely fingerprint individuals, even when traffic passes through Tor or VPNs, and how repeated patterns over weeks or months increase re-identification risk.
The General Data Protection Regulation, enforced in 2018, treats certain metadata as personal data if it can directly or indirectly identify someone.
Key privacy risks include:
- Mapping relationships through contact frequency
- Inferring location via IP geolocation
- Profiling behavioral patterns with centrality measures
- Cross-platform traces that enable deanonymization
Balancing insight with privacy requires careful safeguards. We implement metadata sanitization techniques like k-anonymity, differential privacy noise injection, and obfuscation. Documentation under GDPR Article 30 and proportional SIEM correlation rules ensures compliant and responsible use.
Communication patterns metadata delivers powerful visibility for threat detection and network analysis, but our experience shows disciplined governance is essential to prevent misuse, protect individuals, and maintain organizational trust.
FAQ
How does communication metadata analysis reveal hidden behavior patterns?
Communication metadata analysis examines who communicates, when they communicate, how frequently they interact, and through which channels. By reviewing network traffic patterns, packet capture insights, and sender receiver graphs, analysts can identify consistent interaction structures without accessing message content.
Timestamp clustering and frequency distributions reveal temporal communication bursts. These techniques support behavioral profiling comms and strengthen digital forensics metadata investigations across complex, attribute-rich networks.
What tools help map sender and receiver relationships clearly?
Analysts use contact network visualization and social network analysis to interpret sender receiver graphs accurately. Communication graph theory provides measurable indicators such as reciprocity metrics, directional flow analysis, and centrality measures networks.
Metrics including betweenness centrality comms and eigenvector centrality metadata identify influential participants. Community detection graphs and modularity clustering patterns further expose subgroups within large communication datasets.
How can anomaly detection metadata flag suspicious communication?
Anomaly detection metadata establishes behavioral baselines using message volume trends, peak hour analysis, and off-network activity spikes. It evaluates session duration stats, idle timeout patterns, and reconnection frequency to detect deviations from expected behavior.
Flow-based analysis and metadata extraction pipelines supply SIEM correlation rules and structured threat hunting metadata. This method exposes lateral movement patterns, C2 communication signatures, and beaconing detection intervals.
Why are temporal network dynamics important in investigations?
Temporal network dynamics explain how communication relationships change over time rather than remaining static. Time-series decomposition comms, Fourier transform frequencies, and wavelet analysis bursts reveal cyclical or irregular shifts in activity.
Granger causality tests and VAR models networks assess directional influence between actors. Stochastic block models, exponential random graph models, and latent space models comms provide structured insight into evolving clusters and edge case comms patterns.
How do privacy risks appear within communication metadata?
Privacy risk metadata becomes visible through IP geolocation mapping, device fingerprinting, and user agent patterns that uniquely identify individuals or systems. Cookie tracking metadata and referrer chain analysis expose browsing pathways.
Even encrypted traffic metadata, tor traffic patterns, and proxy chaining metadata leave identifiable traces. Metadata sanitization methods, obfuscation techniques comms, differential privacy metadata, and k-anonymity networks reduce exposure and strengthen protection.
Identifying Communication Patterns Metadata in Practice
Identifying communication patterns metadata allows organizations to detect threats, map networks, and anticipate behavioral shifts without accessing message content. We rely on Network Threat Detection to extract insights from encrypted traffic while limiting intrusive inspection.
Graph modeling, anomaly detection, and statistical analysis refine context and attribution. Proper implementation surfaces insider threat indicators, beaconing intervals, and community clusters before harm occurs.
Teams combining flow-based analysis, metadata enrichment, and compliance-aligned governance maintain operational and regulatory advantage. Start strengthening your Network Threat Detection strategy today.
References
- https://media.defense.gov/2024/Aug/21/2003530453/-1/-1/0/JOINT-CSI-BEST-PRACTICES-EVENT-LOGGING-THREAT-DETECTION.PDF
- https://www.cisa.gov/sites/default/files/2025-01/microsoft-expanded-cloud-logs-implementation-playbook-508c.pdf


