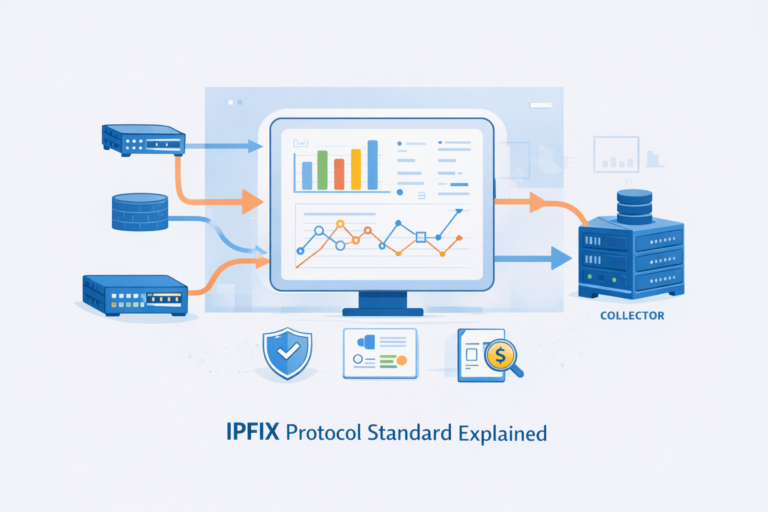
IPFIX Protocol Standard Explained for Real-World Networks
You need IPFIX if you want real visibility into your network, not just green lights on a dashboard.…
You need IPFIX if you want real visibility into your network, not just green lights on a dashboard.…
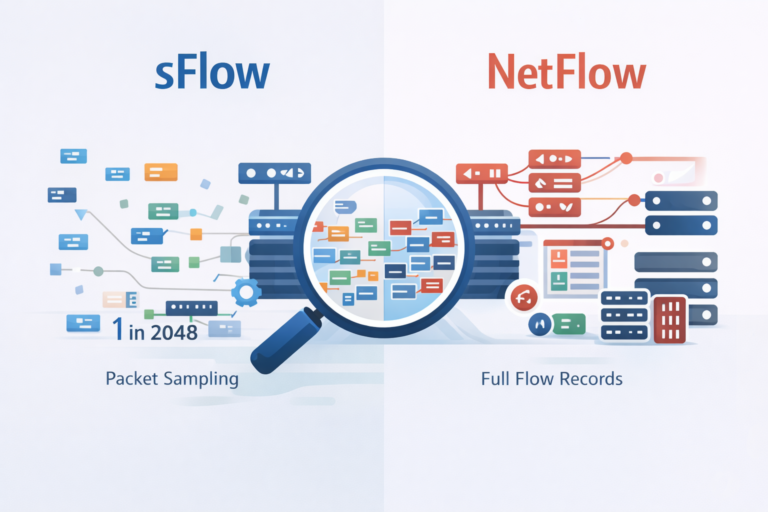
If you’re stuck choosing between sFlow and NetFlow, here’s the short version: go with sFlow for large, high-speed…

Network visibility isn’t about hearing every word, but understanding the conversation. NetFlow captures the metadata, the “who,” “how…
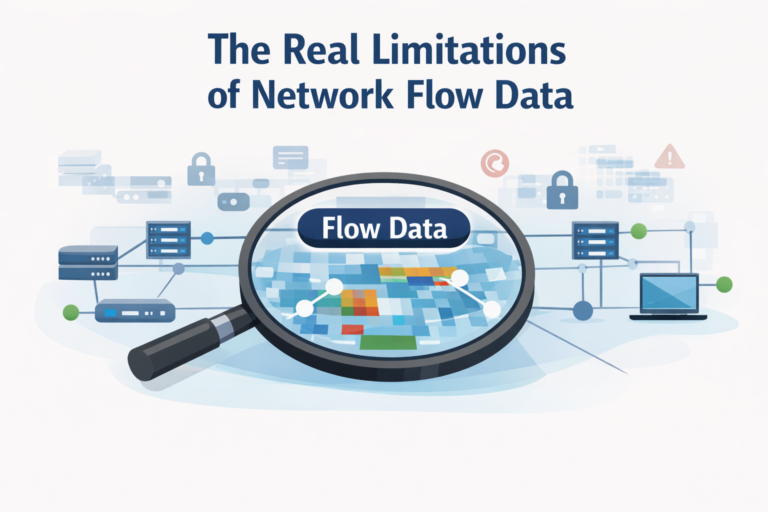
Network flow data gives you broad visibility across your environment, but it was never built to tell you…
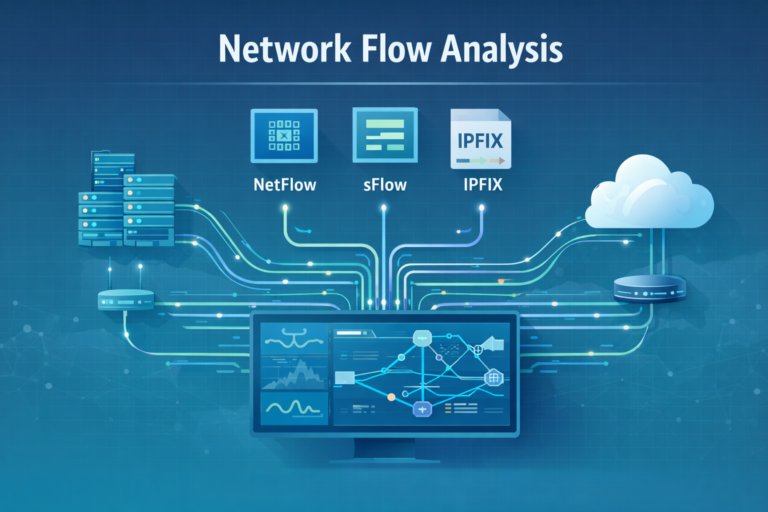
Network flow protocols quietly keep modern networks observable and honest. They turn raw traffic into structured telemetry, so…

Deep Packet Inspection (DPI) is basically when someone looks inside your data, not just where it’s going. Instead…