
DPI for Application Identification Control Explained Clearly
Deep Packet Inspection (DPI) for application identification lets you see what’s really happening inside your network traffic, beyond…

Deep Packet Inspection (DPI) for application identification lets you see what’s really happening inside your network traffic, beyond…
Deep Packet Inspection (DPI) lets a network tell the difference between a harmless cat video and a serious…

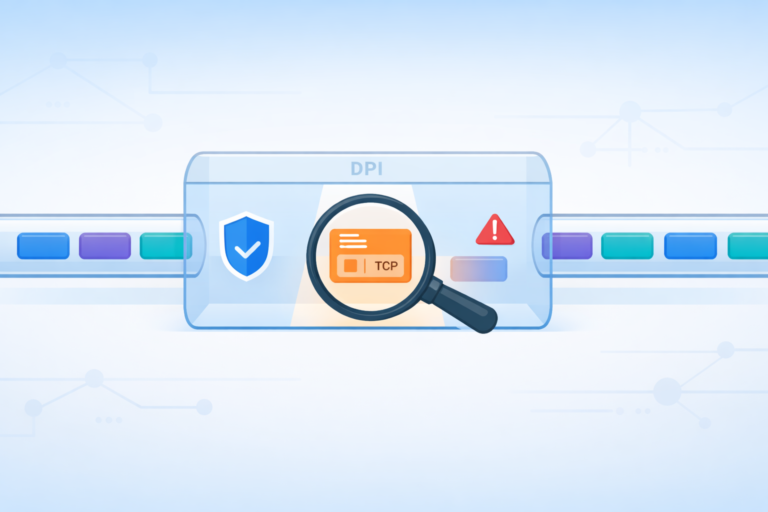
Deep Packet Inspection (DPI) is a method of inspecting not just where network data is going, but exactly…

Deep Packet Inspection (DPI) lets you actually see what’s inside your network traffic, not just where it’s going. …

Deep Packet Inspection (DPI) is a method of examining both the headers and the full payload of data…

AI is already reshaping security operations, turning noisy, chaotic environments into clearer, more manageable ones for SOC teams. …