
Evaluating NDR Vendor Solutions: How to Choose for Effective Network Threat Detection
Evaluating NDR vendor solutions means looking beyond marketing claims to assess how well each platform suits your network’s…

Evaluating NDR vendor solutions means looking beyond marketing claims to assess how well each platform suits your network’s…

Network Detection and Response tools are key to spotting threats lurking in your network before they cause serious…

Cloud networks are messy. Most security teams can’t keep up with all the traffic flowing through their systems,…
Security teams are drowning in network traffic these days. Basic firewall rules don’t cut it when attackers slip…
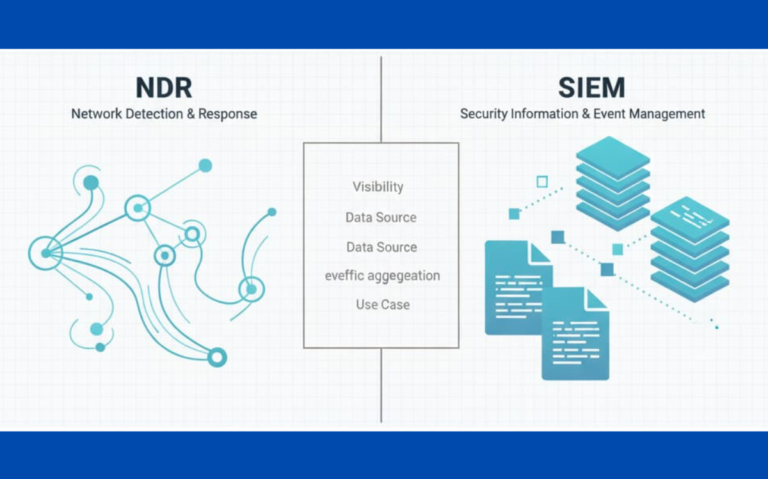
Think of your network like a house, you need both security cameras (NDR) and a detailed guest book…

Watching network traffic used to mean staring at endless data streams. Network Detection and Response changed that mess.…