
Detecting Known Malware Signatures: Why It’s Still Essential for Network Security
When it comes to catching malware, detecting known malware signatures remains a cornerstone of cybersecurity. At its core,…

When it comes to catching malware, detecting known malware signatures remains a cornerstone of cybersecurity. At its core,…

When it comes to zero day threats, the challenge is clear: they’re unknown vulnerabilities, which makes them nearly…

Signature database updates are the backbone of effective network threat detection. These databases store unique threat signatures,malware patterns,…
Basic IDS signatures fall short in today’s threat landscape, they’re like using a store-bought mosquito net against determined…
Think of signature detection as your building’s grumpy security guard, he knows exactly who doesn’t belong, but might…

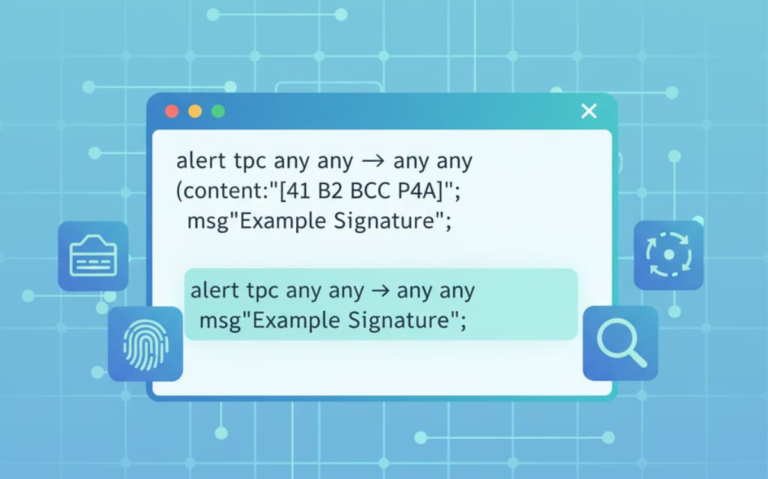
Security teams rely on a simple trick to catch bad code, they match what’s coming in against a…