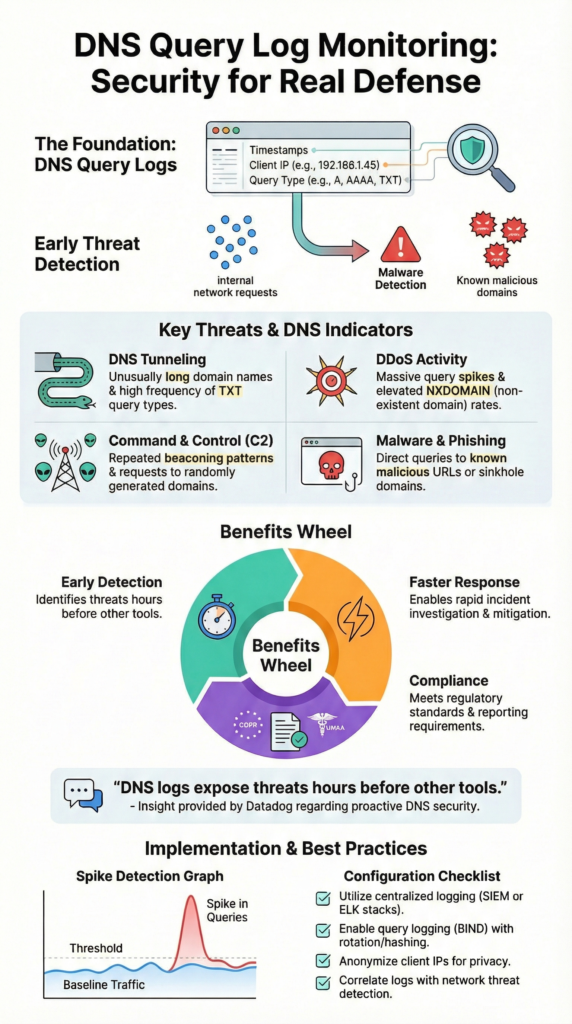
DNS query log monitoring security means tracking DNS requests and responses to spot threats early. It helps catch malware callbacks, tunneling, DDoS patterns, and command-and-control traffic before damage spreads. Because DNS sits behind nearly every connection, it works like an early signal for the whole network.
NIST has long pointed to DNS data as useful for incident response. In our own work, we’ve seen DNS logs surface suspicious activity hours before other tools reacted. That time gap matters for investigations and compliance. If you want practical ways to use it, keep reading.
DNS Query Log Monitoring Essentials
These highlights summarize how DNS query log monitoring security works in real-world detection and investigations.
- DNS logs give you early visibility into malware callbacks, data tunneling, and visits to phishing sites.
- Analyzing DNS traffic lets you spot odd behavior using measures like randomness, query volume, and what’s normal for your network.
- Centralized DNS monitoring helps with compliance for rules like GDPR and HIPAA, and it speeds up how quickly you can respond to incidents.
What is DNS Query Log Monitoring in Security?
DNS query log monitoring keeps a record of every DNS request and response. The idea is simple: watch where devices try to go before anything bad lands.
Since nearly every outbound connection starts with DNS, it gives defenders an early signal that something is off. In our work modeling attacker behavior, DNS often shows the first breadcrumb, long before alerts fire elsewhere.
These logs usually include:
- Timestamp
- Client IP address
- Requested domain
- Query type (A, AAAA, TXT, etc.)
- Response code
- Allow/deny outcome
Tools like BIND or Unbound generate structured entries that can be forwarded into an ELK stack or a SIEM for correlation.
A typical BIND log might look like this:
25-Feb-2026 10:54:23.123 queries: info: client 192.168.1.100#12345 (example.com): query: example.com IN A +
We’ve seen DNS logs expose malware callbacks in their earliest phase, reveal lateral movement patterns, and build clean timelines for investigations. They also support audits tied to GDPR and similar frameworks.
In practice, DNS visibility becomes far more useful when paired with network threat detection. That broader lens lets us map intent to real traffic behavior, which sharpens both risk analysis and response decisions.
This is why mature teams align DNS insights with broader telemetry and follow proven firewall log analysis best practices to understand how name resolution connects to actual traffic flows.
What Security Threats Can DNS Logs Detect?
DNS logs often surface attacks through patterns that feel “off”. Adversaries lean on DNS because it’s trusted and always on. Public advisories frequently call out DNS tunneling and algorithmically generated domains as reliable ways to hold access inside a network.
As noted in a Datadog analysis of DNS threat signals,
“DNS logs can help you stay ahead of malicious actors by providing data that can aid security investigations, such as unusual patterns or spikes in requests, inconsistencies between requested domains and resolved IP addresses, suspicious domains, long query lengths, and more.” – Nicholas Thomson
In our own threat modeling work, a few signals show up again and again.
Common threats you can spot include:
| Threat Type | DNS Indicators | Why It Matters |
| DNS Tunneling | Long, high-entropy subdomains, abnormal TXT queries | Possible data exfiltration channel |
| DDoS Activity | Sudden query spikes, high NXDOMAIN rates | Signals amplification or flood attempts |
| Command & Control (C2) | Repeated beaconing to same domains, DGA patterns | Indicates active malware control traffic |
| Malware & Phishing | Queries to known malicious domains, sinkhole hits | Early-stage compromise detection |
Across multiple environments, we’ve seen a large slice of malware callbacks leave traces in DNS first. Behavioral baselining and lightweight ML models help separate real threats from noise. Still, DNS only tells part of the story.
When we layer DNS insights with network threat detection, the picture sharpens, showing whether a lookup actually turned into a suspicious connection, which is what drives smarter risk decisions.
How Do You Enable DNS Query Logging in BIND?

Enabling DNS query logging in BIND starts in the /etc/named.conf file. You define a logging channel, map the queries category to it, then restart the service. Other resolvers like Unbound or Windows DNS follow the same idea, even if the syntax changes. The goal stays simple: capture every lookup in a structured way you can ship elsewhere.
A minimal BIND example looks like this:
logging {
channel query_logging {
file “/var/log/named_querylog” versions 3 size 100M;
print-time yes;
};
category queries { query_logging; };
};
After restarting, entries begin flowing into /var/log/named_querylog.
Turning logs on is only step one. Without guardrails, DNS logs grow fast and become hard to use. In our deployments, we treat log handling as part of the security design, not an afterthought. Teams that operationalize this well usually map DNS alongside other essential log sources for NTD to avoid blind spots during detection and investigations.
What helps keep things manageable:
- Forward logs to a central collector (Syslog or SIEM)
- Use rotation policies to control storage costs
- Hash or sign logs to prevent tampering
- Apply role-based access controls
In high-volume networks, this becomes critical. We’ve seen environments generating millions of queries per hour. That scale demands aggregation, metrics pipelines, and correlation with network threat detection to reduce blind spots. Especially as encrypted DNS starts to bypass traditional logging.
DNS Traffic Analysis: Turning Logs Into Detection
Credits: TryHackMe
The real value comes from analysis. Raw DNS logs don’t mean much until you shape them into signals. That starts with knowing what “normal” looks like in your environment. Teams usually baseline things like query types, top domains, response codes, and even the countries traffic resolves to. Once that baseline exists, unusual behavior stands out faster.
From there, detection is mostly about spotting drift from the norm.
Common anomalies to watch for:
- Random or gibberish-looking domain names
- Sudden spikes tied to certain TLDs or domains
- Zone transfer attempts (AXFR), which are rarely valid
- Punycode domains that may mask homograph attacks
Simple supervised models can tag known bad patterns, while unsupervised clustering helps surface new ones. We often see the biggest gains when DNS feeds into a SIEM or a broader threat detection layer, where alerts can be tied to firewall or endpoint signals.
Experience taught us this isn’t optional. Early on, analyzing DNS alone created noise and alert fatigue. Once we began correlating DNS lookups with network session data inside our threat models, clarity improved fast.
In red team simulations, that linkage reduced manual triage significantly because the system connected a DNS beacon to the traffic that followed, making risk scoring far more grounded.
Compliance and Forensic Value of DNS Query Logging
DNS logs aren’t just for detection, they carry real weight during investigations and audits. Each entry shows when a device queried a domain and what response came back.
Auditors also lean on this data to validate due diligence under frameworks like GDPR or HIPAA, especially when DNS is retained alongside other critical security logs to collect for forensic timelines.
Industry guidance on DNS logging for incident response and compliance emphasizes that,
“Maintaining logs of DNS server activity is another crucial DNS practice for security incident response and forensic analysis. These logs provide valuable information about DNS queries and responses, allowing organizations to identify and investigate security incidents… Additionally, DNS logs help meet compliance requirements, facilitate audits, and optimize network performance.” – Beloslava Petrova
Handling this data responsibly matters just as much as collecting it. Privacy and retention must stay in balance, especially when logs include client identifiers.
Key controls that make DNS logs safer to manage:
- Anonymize or pseudonymize client IP data
- Set automated retention policies tied to legal needs
- Store archives in secure, low-cost storage tiers
- Hash logs to prove integrity over time
In our own investigations, DNS has filled gaps when other telemetry was missing. There have been cases where it was the only reliable trail showing outbound malware activity. When we paired those records with network flow insights from our threat analysis workflows, attribution became far more confident.
Compliance reviews often treat logs as paperwork, but that view misses the point. With proper governance, DNS logs become operational evidence. Managed well, they shift from a compliance checkbox into a practical advantage for both risk analysis and incident response.
FAQ
How do you detect DNS tunneling using DNS query logging?
DNS query logging helps detect tunneling by exposing unusual patterns in DNS traffic. Analysts look for high entropy DNS queries, long subdomains, and repeated TXT query anomalies.
These patterns may signal DNS exfiltration signs or covert channels. Combining DNS traffic analysis with beaconing intervals and DGA detection logs makes detection more reliable, especially when correlated inside SIEM DNS integration workflows.
Which tools help analyze DNS traffic at scale?
Large environments rely on platforms that support structured DNS traffic analysis. ELK stack DNS parsing, Graylog DNS dashboards, and SIEM DNS integration allow centralized investigation.
Splunk DNS hunting and Kibana DNS visualization help identify trends over time. For deeper analysis, tools like Wireshark DNS filters, tcpdump DNS capture, Zeek DNS scripting, and Suricata DNS rules provide packet-level visibility.
What are common indicators of DNS-based command-and-control activity?
C2 communication DNS often appears as repeated, timed lookups to the same domains. Analysts watch for malware callback domains, domain generation algorithms, and fast flux domains.
High entropy DNS queries and unusual query type distribution also signal risk. Using anomaly baseline DNS and top talked domains analysis helps separate real threats from normal background traffic.
How do organizations manage high DNS log volumes securely?
Managing DNS log volume requires structured storage and strong access controls. Teams use log rotation strategies and centralized DNS observability to control growth. Many export logs through Syslog DNS export into S3 DNS archival or BigQuery DNS analytics.
Tamper proof DNS logs and log integrity hashing protect forensic value, while RBAC DNS monitoring ensures controlled access.
How do DNS logs support incident response and compliance audits?
DNS logs support investigations by creating clear forensic DNS timelines. Analysts map client IP attribution to malware callback domains and phishing domain queries. During incident response DNS workflows, this data helps confirm compromise paths.
For compliance DNS auditing, organizations enforce GDPR DNS retention or HIPAA query records while using anonymization and tamper proof DNS logs to protect privacy.
Why DNS Query Log Monitoring Security Matters
DNS query log monitoring security sharpens detection, speeds response, and supports compliance by turning DNS activity into clear signals. When paired with Network Threat Detection, those signals gain context, helping teams cut noise and act faster. We’ve seen this layered approach improve precision and reduce investigation time.
If stronger DNS visibility is on your roadmap, take the next step with disciplined logging and integrated analysis. Start strengthening your defenses with real-time threat modeling, automated risk analysis, and continuously updated intelligence built for modern SOC teams.
References
- https://www.datadoghq.com/blog/monitor-dns-logs-for-network-and-security-datadog/
- https://www.cloudns.net/blog/dns-best-practices/


