Network packet broker benefits include better visibility, lower monitoring waste, and stronger security operations. We often see teams add more tools but still miss key context because packets arrive duplicated, delayed, or fragmented. A smarter observability layer helps clean and direct traffic where it matters most.
As network links grow from 10G to 100G and workloads spread across campuses, data centers, and cloud platforms, traffic becomes harder to manage. We often recommend Network Threat Detection first because it relies on accurate, timely data. The right setup can also improve ROI. Keep reading to see how it works in practice.
Quick Wins: Network Packet Broker Benefits at a Glance
If you need the short version, these points sum up how NPBs improve visibility, reduce waste, and support stronger network operations.
- A network packet broker (NPB) centralizes traffic from TAPs, SPAN ports, and cloud mirrors so tools share the same view.
- NPBs reduce waste through traffic filtering, packet deduplication, and packet load balancing.
- Security and operations teams gain faster detection, cleaner telemetry, and longer life from existing tools.
What Is a Network Packet Broker and How Does It Work?
A network packet broker sits between traffic sources and monitoring tools. Its job is simple: collect traffic, clean it up, and send each tool only what it needs. Instead of connecting every tool to every switch, teams build one managed traffic layer.
In practice, we have seen this remove a lot of messy cabling and one-off workarounds. Engineers no longer need to keep adding direct feeds each time a new tool appears. That alone saves time.
An NPB can receive traffic from network TAPs, SPAN ports, routers, switches, and virtual taps. Then it applies policy before forwarding data. Choosing the right tap media also matters, especially when comparing different fiber optic network Taps types for higher-speed links.
Common functions include:
- Traffic aggregation from many links
- Packet filtering by IP, VLAN, port, or protocol
- Packet steering to security or performance tools
- Packet replication when multiple tools need the same feed
- Packet slicing to trim unneeded payload data
We often compare it to air traffic control. Packets still move, but now routes make sense. Security teams get threat traffic. Performance teams get application traffic. Everyone works from cleaner inputs.
How Do NPBs Improve Network Visibility?
Many networks grow in pieces. One team adds cloud sensors, another adds branch monitoring, and someone else runs separate tools in the data center. Over time, every platform sees only part of the picture. That is how blind spots start.
A network packet broker helps by pulling those feeds into one visibility layer. It can send the same trusted packet view to operations, security, and engineering teams. We have watched outage calls move faster once everyone reviewed the same timeline instead of arguing over dashboards.
Modern environments also use overlays and tunnels. Good brokers can interpret VXLAN, GRE, and GENEVE, which matters in virtualized and multi-cloud networks. When teams debate captures methods, understanding network Taps vs. SPAN/mirror ports often helps close visibility gaps early.
Visibility gains often include:
- Better east-west traffic insight inside data centers
- Stronger north-south monitoring at the perimeter
- Cleaner packet capture for root cause work
- Shared telemetry for NetOps and SecOps
- Faster checks when users report slowness
As Zero Trust designs add more internal traffic paths, clear visibility becomes more important. Teams cannot protect what they cannot clearly see.
How Do NPBs Reduce Tool Overload and Waste?
Many monitoring and security tools charge by throughput, storage, or licensed capacity. When every packet gets copied everywhere, costs rise fast. Worse, analysts end up sorting through noise instead of useful signals.
That is where an NPB earns its keep. It filters traffic first, then forwards only what matters. We have seen organizations recover large amounts of capacity after removing duplicate mirrored traffic that several tools were processing at once.
Rather than buying another appliance right away, some teams gain room simply by managing feeds better. Physical deployments also benefit from solid copper network tap considerations and install planning before traffic loads increase.
Useful waste-reduction features include:
- Packet filtering to keep only needed flows
- Packet deduplication to remove repeated traffic
- Packet slicing to keep headers and trim payloads
- Traffic prioritization for business-critical apps
- Packet buffering during sudden spikes
Our teams often pair this with threat models and risk analysis tools. That helps decide which traffic deserves inspection and which traffic can be reduced. Better choices at the packet layer usually mean lower spend higher up the stack.
Good data beats more data almost every time.
Why Are NPBs Valuable for Security Operations?
Credits: Profitap
Security tools work best when the data they receive is complete, timely, and relevant. If feeds are delayed, duplicated, or missing key sessions, alert quality drops. False positives rise, and real threats can hide in the noise.
That is why many teams begin with Network Threat Detection. Detection quality depends on packet quality. We regularly help organizations map risks first, then tune traffic flows so controls inspect what matters most.
An NPB can steer selected traffic to IDS/IPS, SIEM integration pipelines, packet capture tools, and forensic platforms. It can also separate routine backup traffic from suspicious lateral movement, which makes triage easier.
Security benefits often include:
- Better threat detection and anomaly spotting
- Cleaner feeds for deep packet inspection (DPI)
- Improved support for SSL/TLS decryption workflows
- Faster evidence gathering during incidents
- Better checks on segmentation policy traffic
We have seen SOC teams cut investigation time once noisy traffic was filtered out. Mature security programs know the lesson well: strong tools matter, but clean telemetry matters almost as much.
Are Network Packet Brokers Worth It for Mid-Sized Networks?
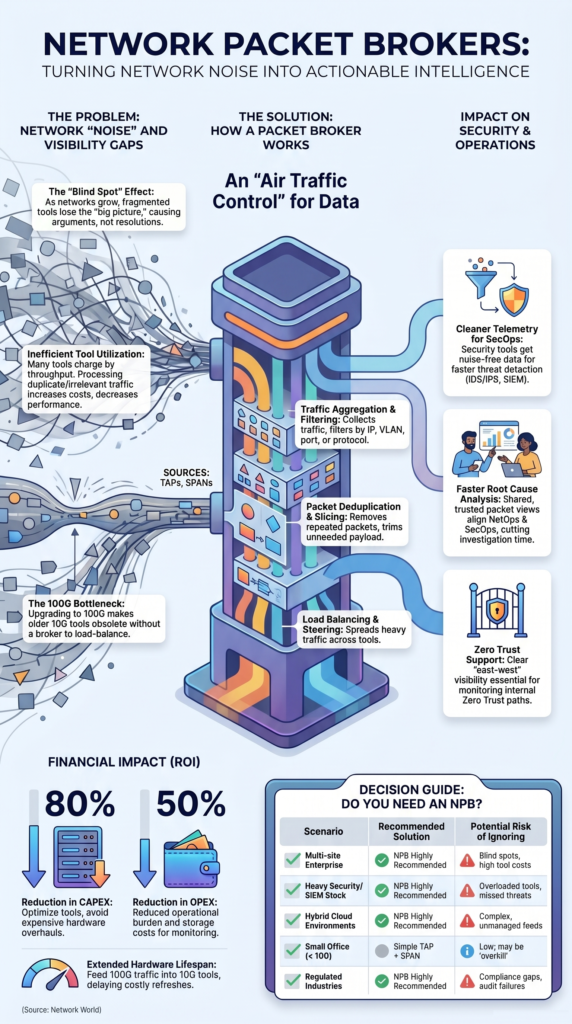
The answer depends less on company size and more on complexity. Some mid-sized organizations gain value quickly. Others run well with simpler designs for years.
We have seen both cases. A single office with modest traffic and one monitoring platform may not need another layer. But a business with multiple sites, growing cloud workloads, and heavy inspection needs often reaches a tipping point sooner than expected.
Data from Network World demonstrates
“Network packet brokers optimize incident analysis by enabling IT and Security Operations to gain situational awareness and security intelligence… enterprises can realize an 80% reduction in capex and a 50% reduction in opex, since NPBs make it possible to concentrate and optimize network tools for better performance.” – Network World
Compliance pressure can also change the math. Use this quick guide:
| Scenario | NPB Likely Worth It | Simpler Alternative |
| Multi-site enterprise | High | Limited |
| Heavy IDS/IPS and SIEM stack | High | Noisy direct feeds |
| Small office under 10G | Low | TAP + SPAN ports |
| Regulated industry | High | Risk of gaps |
| Hybrid cloud with many tools | High | Complex manual feeds |
Our advice is usually straightforward: look at operational pain. If teams keep fighting blind spots or overloaded tools, an NPB deserves a serious review.
What ROI Benefits Do NPBs Deliver?
Return on investment usually comes from avoiding waste, delaying upgrades, and helping staff solve issues faster. Those gains often add up more than people expect.
Consider a company moving to a 100G network while several tools still support 10G. Replacing every appliance at once can be expensive. A broker can load balance traffic across existing tools or send only selected flows to older systems.
We have seen teams extend hardware life by years with this approach. That frees budget for projects with higher risk impact, such as stronger detection coverage or better response workflows.
Common ROI drivers include:
- Longer life for monitoring appliances
- Better sharing across multi-vendor tools
- Lower storage costs through filtering
- Faster troubleshooting and less downtime
- Fewer emergency purchases during spikes
- Better analyst time spent on real issues
Our own risk analysis work often shows hidden costs tied to poor visibility: slow investigations, missed threats, and reactive buying. Once leaders include those costs, the business case becomes clearer.
ROI is not only hardware savings. It is smoother operations.
When Can an NPB Become Overkill?
Not every network needs a packet broker. Sometimes the smarter move is fixing basic architecture first. We agree with engineers who warn against buying complex platforms before solving simple problems.
If traffic volumes are modest, one security stack has spare capacity, and visibility gaps are rare, direct connections may be enough. Smaller environments can often do well with TAPs, flow logs, and thoughtful design.
Insights from Keysight indicate
“The real challenge lies in efficiently funneling data from the network to each tool that needs it… If you only have a few network segments, and relatively few analysis tools, the two may be connected directly.” – Keysight
We have also seen cases where an NPB was installed but no one owned policy tuning. Over time, stale rules built up and the extra layer became more burden than benefit.
Warning signs of overbuying include:
- Low traffic growth
- Few monitoring tools
- Minimal east-west traffic
- No retention or compliance pressure
- No clear owner for operations
- Stable performance with current tooling
Our rule is practical: buy technology to remove a bottleneck, not to create one. If teams cannot point to real pain today or clear growth tomorrow, patience may be the better investment.
FAQ
How does a network packet broker improve network visibility?
A network packet broker improves network visibility by collecting traffic from SPAN ports, network TAPs, and cloud networks into one observability layer. It filters duplicate packets, balances traffic loads, and sends clean data to monitoring tools and security tools. This setup gives teams real-time visibility across campus networks, WAN links, and data center environments.
When should teams use NPB instead of direct packet mirroring?
Teams should use an NPB instead of direct packet mirroring when SPAN ports cause overload, dropped packets, or limited traffic control. An NPB adds packet filtering, packet deduplication, packet slicing, and packet steering before forwarding traffic. These features protect monitoring tools, improve tool performance, and support high-speed networks with heavy traffic volumes.
Can a packet broker help security operations teams detect threats faster?
Yes, a packet broker helps security operations teams detect threats faster by sending clean traffic to IDS/IPS tools, SIEM platforms, and threat detection systems. It improves SOC visibility, anomaly detection, and network forensics by removing duplicate data and excess noise. Analysts can review accurate packet capture data and respond faster.
How does traffic aggregation reduce monitoring tool costs?
Traffic aggregation reduces costs by combining traffic feeds from many links into fewer monitoring tools. A network packet broker lets teams share one tool across several network segments, improve tool consolidation, and extend appliance lifecycle. Teams avoid buying duplicate devices while still maintaining network performance monitoring and capacity planning coverage.
Is a network packet broker useful in hybrid cloud environments?
Yes, a network packet broker is useful in hybrid cloud and multi-cloud environments because traffic moves across virtualized networks, SD-WAN links, and data centers. It helps teams correlate traffic, manage encrypted traffic flows, and maintain network visibility. Teams gain centralized management and consistent monitoring across changing infrastructure.
Better Visibility Matters When Networks Get Busy
You feel the strain when traffic grows, tools overlap, packets get messy, and your team spends more time sorting noise than finding risk. It slows everything down.
That’s why many teams start with NetworkThreatDetection.com to uncover hidden gaps first, then use an NPB to control packet flow as complexity grows. If you want smarter visibility that scales with demand, start here and talk with our team today.
References
- https://www.networkworld.com/article/712418/infrastructure-management-network-packet-brokers-increase-visibility-and-performance.html
- https://www.keysight.com/us/en/assets/3120-1272/brochures/What-Is-a-Network-Packet-Broker-And-Why-Do-You-Need-One.pdf