IoT environments generate massive telemetry data, but without proper analysis, this data becomes noise instead of insight. We’ve seen organizations struggle not because of lack of data, but because they don’t interpret it effectively. By analyzing IoT device telemetry data, teams can uncover hidden risks, detect compromised devices, and improve overall visibility.
This article explores practical strategies, real challenges, and actionable techniques to transform telemetry into security intelligence. Keep reading to learn how to turn raw IoT data into powerful threat detection.
Key Insights: Analyzing IoT Device Telemetry Data
Analyzing IoT telemetry is not just about monitoring, it’s about understanding behavior patterns and acting on them.
- Telemetry data enables early anomaly detection
- IoT device security best practices reduce attack surfaces
- Threat intelligence enhances detection accuracy
IoT Device Security Best Practices
A strong foundation is essential before analyzing telemetry.
- Use device authentication and identity management
- Enforce firmware updates regularly
- Segment IoT networks from core systems
- Apply least privilege access controls
- Encrypt all device communications
These iot device security best practices ensure telemetry data remains trustworthy and useful.
Security Challenges Monitoring IoT Devices
Credits: How-Network-com
Monitoring IoT devices introduces unique difficulties:
- High device diversity and scale
- Limited device processing power
- Inconsistent data formats
- Lack of standard security controls
These security challenges monitoring iot devices often result in blind spots.
Collecting Telemetry Data IoT Platforms
Effective telemetry starts with proper data collection.
- Use centralized IoT platforms for aggregation
- Normalize data across device types
- Capture metrics like traffic, behavior, and performance
- Store data efficiently for long-term analysis
A supporting reference explains:
“Telemetry is the collection of measurements or other data at remote or inaccessible points and their automatic transmission.” – Wikipedia
Identifying Anomalous IoT Device Behavior
Detecting anomalies is the core of telemetry analysis.
- Establish baseline device behavior
- Monitor deviations in traffic patterns
- Use machine learning for behavior modeling
- Track unusual communication frequency
Identifying anomalous iot device behavior allows early threat detection before escalation.
Securing IoT Communication Protocols MQTT CoAP

Protocols like MQTT and CoAP are widely used but often misconfigured.
- Enable TLS encryption
- Use strong authentication mechanisms
- Restrict unauthorized topic access
- Monitor protocol-specific anomalies
A journal-backed insight states:
“MQTT is a lightweight messaging protocol for small sensors and mobile devices, optimized for high-latency or unreliable networks.” – Wikipedia
Detecting Compromised IoT Devices Botnets
IoT botnets remain one of the biggest threats.
- Look for unusual outbound traffic spikes
- Detect repeated connection attempts
- Monitor command-and-control patterns
- Correlate telemetry with known attack signatures
Detecting compromised iot devices botnets early helps prevent large-scale attacks.
IoT Specific Threat Intelligence Feeds
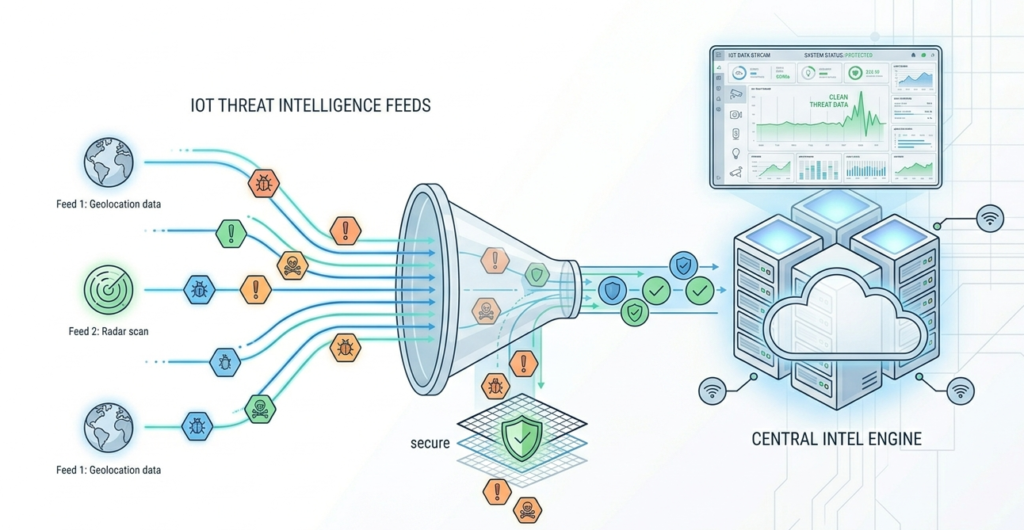
Threat intelligence strengthens telemetry analysis.
- Integrate iot specific threat intelligence feeds
- Correlate telemetry with known vulnerabilities
- Update detection rules continuously
- Share intelligence across teams
Summary Table: Key Components of IoT Telemetry Analysis
| Component | Purpose | Impact on Security |
| Data Collection | Gather device metrics | Visibility |
| Behavior Analysis | Identify anomalies | Early detection |
| Protocol Security | Protect communication | Data integrity |
| Threat Intelligence | Enhance detection accuracy | Faster response |
| Continuous Monitoring | Track device activity | Ongoing defense |
FAQ
Why is telemetry data important for IoT security?
Telemetry provides continuous visibility into device behavior, enabling early detection of abnormal activity and potential compromises.
What makes IoT monitoring challenging?
The diversity, scale, and limited capabilities of IoT devices make consistent monitoring and security enforcement difficult.
How do you identify anomalous IoT device behavior?
By creating behavioral baselines, applying analytics, and correlating with threat intelligence to detect deviations.
Why must MQTT and CoAP be secured?
Because they are lightweight protocols, they lack built-in strong security, making them vulnerable without encryption and authentication.
Turning IoT Telemetry into Actionable Security
Analyzing IoT device telemetry data transforms raw signals into meaningful security insights. By applying structured collection, anomaly detection, and secure communication practices, organizations can proactively defend against evolving threats. Combined with threat intelligence, telemetry becomes a strategic asset for resilience.
Strengthen your security posture today, explore advanced solutions at Network Threat Detection and stay ahead of emerging IoT threats.
References
- https://en.wikipedia.org/wiki/Telemetry
- https://en.wikipedia.org/wiki/MQTT


