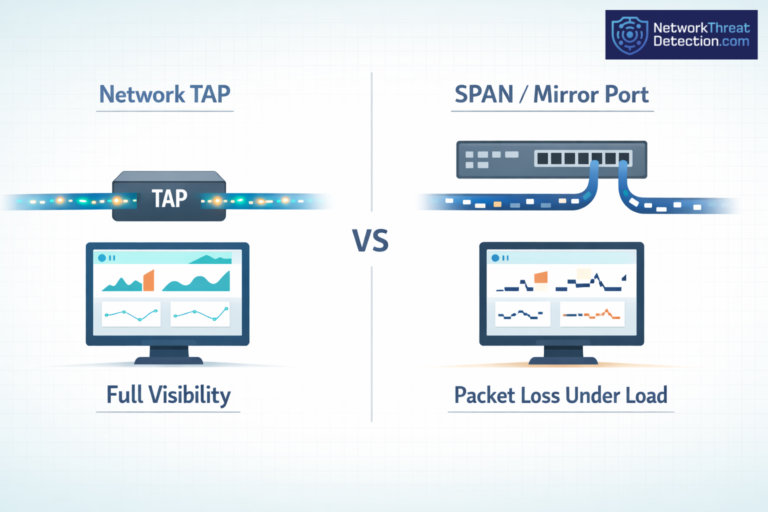
Network Taps Vs. SPAN/Mirror Ports: What Matters
Network taps see every packet. SPAN ports can miss some when traffic spikes. That gap shows up fast…
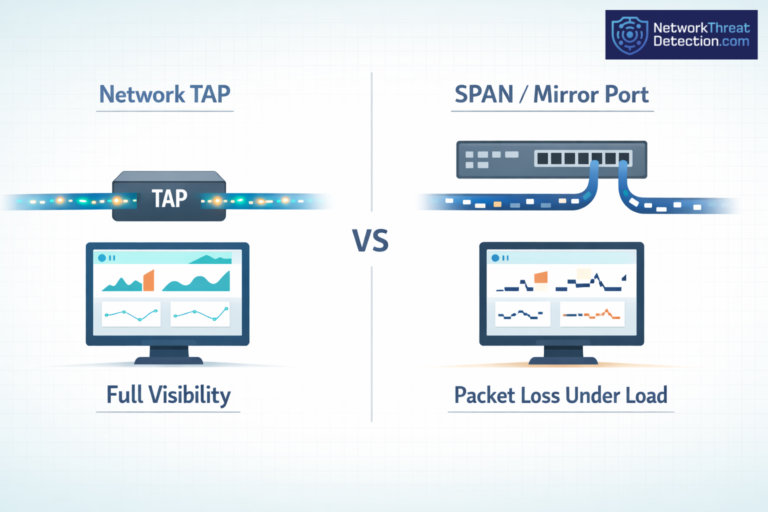
Network taps see every packet. SPAN ports can miss some when traffic spikes. That gap shows up fast…

Lock down cloud storage logs so they cannot be changed, lost, or quietly accessed. These records track activity…
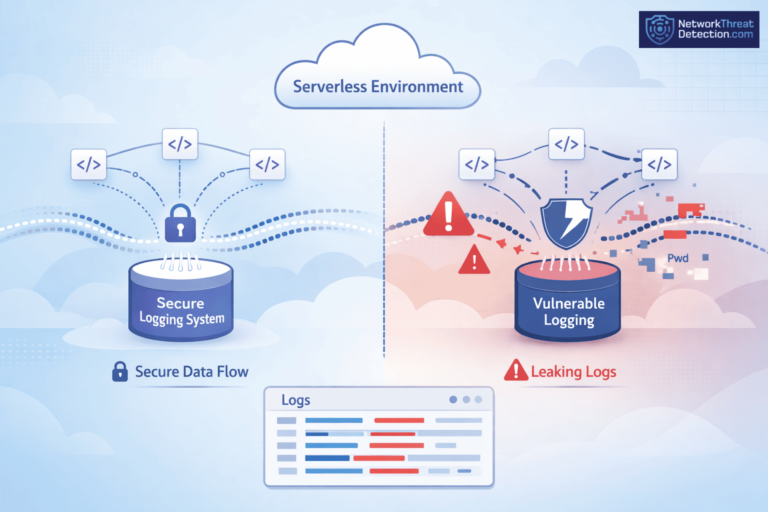
Logs cause problems when no one pays attention to what they hold. Teams use them every day to…

Kubernetes audit log monitoring keeps track of every API call in your cluster, showing who did what and…

Analyzing VPC flow logs security starts with seeing who’s talking across your cloud network, which ports they use,…

Centralizing cloud logs SIEM means bringing logs from AWS, Azure, and GCP into one place for clearer threat…