Creating Custom IDS Signatures: Boost Network Threat Detection Precision
Basic IDS signatures fall short in today’s threat landscape, they’re like using a store-bought mosquito net against determined…
Basic IDS signatures fall short in today’s threat landscape, they’re like using a store-bought mosquito net against determined…
Think of signature detection as your building’s grumpy security guard, he knows exactly who doesn’t belong, but might…

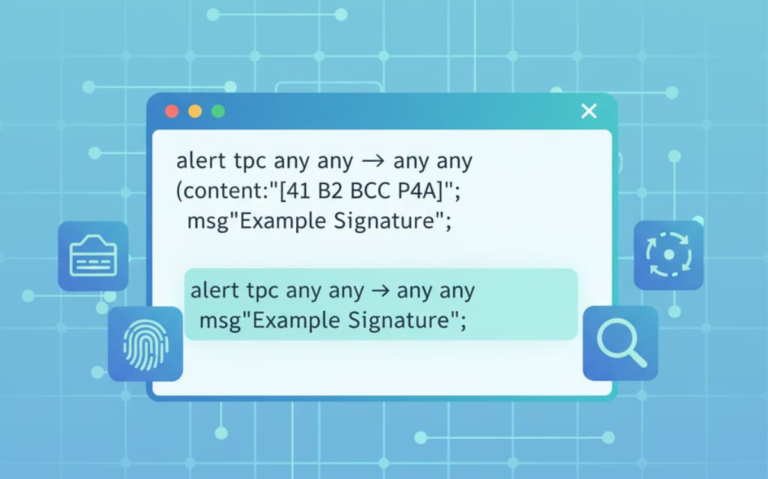
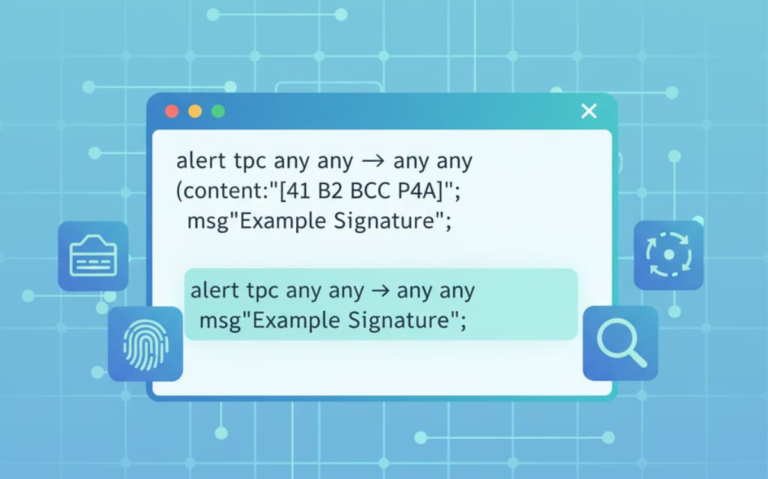
Security teams rely on a simple trick to catch bad code, they match what’s coming in against a…

Network security teams rely on pattern matching to catch threats, just like cops matching fingerprints at a crime…

When it comes to threat hunting, Network Detection and Response (NDR) stands as a crucial ally. NDR gives…

The NDR incident response workflow is a step-by-step process that organizations use to spot network threats quickly, stop…