The value of network metadata analysis improves threat detection, accelerates incident response, and preserves privacy by focusing on connection details rather than inspecting full payloads. With global cybercrime projected to cost $10.5 trillion annually, organizations need detection methods that cut storage demands and speed up investigations.
By leveraging enriched flow records, DNS query logs, and TLS handshake information, teams can trace attacks without wading through massive packet captures. This approach delivers context, scale, and speed that traditional methods struggle to match. Keep reading to see how network metadata analysis is changing the way security teams detect and respond to threats.
Quick Wins – Why Network Metadata Scales
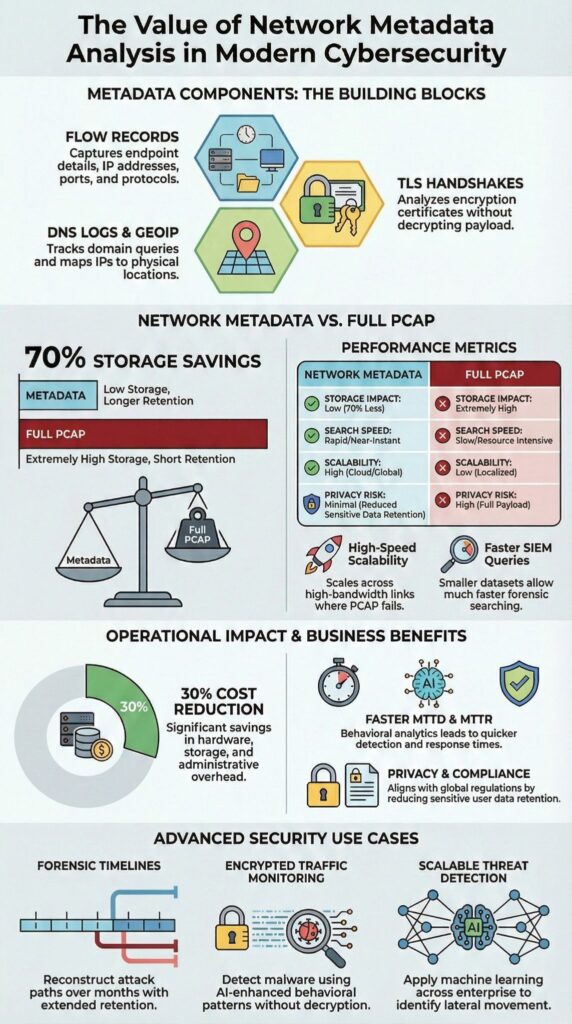
- Network metadata provides scalable visibility with up to 70% lower storage overhead than full PCAP in large environments.
- Behavioral analytics built on flow metadata improves MTTD reduction and MTTR improvement.
- Network Threat Detection platforms use metadata to detect lateral movement, C2 communication metadata, and exfiltration patterns without decrypting traffic.
What Is Network Metadata Analysis and Why Does It Matter?
Network metadata analysis tracks IPs, ports, protocols, timestamps, and flow volumes without storing full payloads, a practice central to network metadata collection that helps teams maintain scalable visibility and reduce storage overhead. It turns raw traffic into structured telemetry using formats like NetFlow, IPFIX, sFlow, Zeek metadata, and Suricata logs.
Instead of saving every packet, metadata focuses on connection details and bidirectional flows. This reduces storage, improves privacy, and supports compliance.
Teams monitor attacker behavior through patterns, not payloads. Common practices include:
- Flow metadata: session duration, byte and packet counts
- DNS query logs and TLS handshake data
- Protocol metadata and port scan detection
- Metadata enrichment with geoIP and reputation scoring
When integrated with AI-driven security platforms, metadata analysis enables scalable feature extraction and dimensionality reduction, helping teams detect threats faster while keeping sensitive data protected. By focusing on context over content, organizations can respond quickly without storing excessive data.
How Does Network Metadata Enable Scalable Threat Detection?

Network metadata analyzes flow patterns instead of full payloads, allowing real-time anomaly detection across millions of connections. This reduces mean time to detect (MTTD) and speeds up containment decisions.
Full packet inspection is rarely feasible at high throughput, especially with east-west traffic, IoT devices, and OT ICS flows. Using network session records derived from flow metadata allows detection at scale without payload inspection.
Detection starts by baselining traffic with behavioral analytics. Effective metadata-driven detection includes:
- Monitoring DNS query logs for DGA activity
- Tracking beaconing flows tied to C2 communications
- Identifying abnormal IPs and unusual protocol activity
- Detecting RDP brute force attempts and Kerberos anomalies
Enriched flow records feed into SIEM pipelines and threat hunting workflows. Machine learning applies supervised classification and unsupervised anomaly detection to flag deviations from baseline traffic.
The real-world value of metadata analysis is supported by research. As highlighted in a Virginia Tech federal cybersecurity workshop report:
“Workshop 1 validated the technical concept that the analysis of metadata about network traffic would significantly enhance the federal government’s cybersecurity capabilities.” – Virginia Tech
This reinforces that metadata-driven detection is not just theory, it measurably strengthens threat detection capabilities at scale.
Network Metadata vs. PCAP: Which Approach Delivers More Value?
From our experience, PCAP captures full payloads, but metadata gives us enterprise-wide visibility with far lower storage requirements and better scalability for networks exceeding 10 Gbps sustained traffic. Both approaches have their place, but the operational impact is very different.
| Feature | Network Metadata | PCAP |
| Storage Overhead | Lower, no payload retention | High storage demand |
| Scalability | Enterprise-wide coverage | Limited by storage costs |
| Privacy Impact | Reduced sensitivity | High due to content |
| Forensic Depth | Behavioral context | Full payload detail |
| Query Performance SIEM | Faster indexed searches | Slower bulk retrieval |
We’ve found that metadata delivers value in specific ways:
- Scalable threat hunting across millions of connections per hour
- Compliance monitoring without storing sensitive payloads
- DDoS baselining and SYN flood detection
- Encrypted traffic analysis and behavioral modeling
PCAP remains essential for situations where full payload reconstruction is required, such as deep protocol analysis or detailed forensic investigation. In practice, we combine both approaches: Network Threat Detection handles behavioral analytics, while lightweight packet capture provides the depth needed to confirm suspicious activity.
This hybrid model strengthens our threat models, keeps risk analysis actionable, and ensures our network security measures adapt to emerging threats.
How Is Network Metadata Used in Real World Forensics?

Network metadata helps investigators reconstruct attacker behavior using DNS logs, flow records, and certificate data, allowing C2 infrastructure to be traced without decrypting payloads.
During incident response, we rely on DNS query logs, JA3 fingerprints, TLS handshake information, and geoIP metadata to identify suspicious domains.
During incident response, we rely on DNS query logs, JA3 fingerprints, TLS handshake information, and geoIP metadata to identify suspicious domains. Timestamp metadata and session duration flows let us map lateral movement across segmented networks. Key forensic applications include:
- Identifying exfiltration through abnormal byte counts
- Detecting passive reconnaissance and active probing
- Tracing supply chain compromises via unusual domain generation patterns
- Supporting legal and compliance reviews with attribution evidence
The academic perspective confirms this approach. As noted on the University of Michigan Safe Computing site:
“Threat detection focuses on metadata associated with network traffic, such as the source and destination IP addresses, DNS activity …” – University of Michigan
This emphasizes that leveraging metadata is a recognized best practice for forensic reconstruction and proactive threat hunting.
How Does Network Detection and Response Leverage Metadata?
In our experience, Network Detection and Response (NDR) platforms use metadata flows to establish baselines of normal behavior and spot malicious activity without needing to decrypt traffic.
Unlike traditional IDS that rely on static signatures, NDR emphasizes context-driven security built on behavioral analytics models. We ingest normalized metadata from multiple sensors and centralize it into data lake repositories for faster analysis and correlation.
Key NDR metadata capabilities we rely on include:
- Correlating IOCs across threat intelligence feeds
- Real-time analytics for beaconing and unusual flows
- Risk scoring based on anomaly detection
- AI-enhanced unsupervised anomaly detection
We position Network Threat Detection as the first operational layer in this architecture. It provides vendor-agnostic flows and integrates with network metadata analysis tools to enrich connection data with reputation scoring and actionable insights.
In cloud-first environments with endpoint blind spots, metadata-driven NDR closes visibility gaps. Our teams track IoT device traffic, OT ICS flows, and east-west movement that traditional controls often miss.
The results are tangible: faster MTTD, improved detection coverage, and consistent MTTR reductions across hybrid infrastructures. By combining behavioral models with real-world metadata, we strengthen threat detection and make our risk analysis actionable against emerging threats.
What Are the Business and Compliance Benefits of Network Metadata Analysis?
Credits : Lumu Technologies
Network metadata analysis helps reduce infrastructure costs, improve compliance posture, and support AI-driven analytics across enterprise data environments.
In our work, we’ve seen organizations integrate metadata into centralized platforms and achieve up to 30% operational savings. This comes from avoiding full payload retention while still maintaining a complete audit trail, making investigations faster and storage far more efficient.
The business advantages we observe include:
- Lower storage and compute requirements
- Privacy-compliant logging aligned with GDPR network metadata rules
- Faster audit response using searchable timestamp metadata
- Scalable SIEM ingestion and query performance
Metadata also plays a key role in AI and machine learning initiatives. By feeding normalized schemas, dimensionality-reduced flows, and historical trend analysis into feature extraction pipelines, it creates structured inputs that drive advanced analytics.
From our perspective, executives prioritize both risk reduction and cost control. Network metadata analysis delivers on both fronts. It strengthens context-aware security while keeping sensitive content protected, and it integrates directly into our threat models and risk analysis tools, helping us address emerging threats efficiently across hybrid network environments.
FAQ
How does network metadata analysis improve threat detection accuracy?
Network metadata analysis improves detection accuracy by examining network metadata, flow metadata, and network traffic metadata for behavioral patterns.
Teams analyze threat detection metadata, anomaly detection flows, and behavioral analytics network signals to identify suspicious activity. Reviewing source IP metadata, destination port flows, and protocol identifiers allows analysts to detect malicious behavior early and significantly reduce false positives.
Can metadata replace full packet capture in investigations?
Metadata can replace full packet capture in many investigations because it serves as a practical full PCAP alternative.
Analysts rely on NetFlow records, IPFIX data, and lightweight packet capture to review bidirectional flows, session duration flows, and byte counts network patterns. This method supports detailed network forensics, enables accurate forensic timelines network, and reconstructs attack sequences without excessive storage costs.
What role does metadata play in tracking lateral movement?
Metadata plays a critical role in lateral movement tracking across internal systems. By analyzing east-west traffic metadata, connection metadata, and timestamp metadata, security teams identify abnormal internal communication patterns.
Evidence from RDP brute force logs, Kerberos anomalies, and failed SMB signing checks reveals attacker progression. This visibility strengthens Network Detection Response and accelerates containment decisions.
How does metadata analysis reduce response time and operational costs?
Metadata analysis reduces response time by leveraging network telemetry for real-time analytics metadata and historical trend analysis. Structured SIEM metadata ingestion, supported by normalized metadata schemas and enriched flow records, improves investigation speed and query performance SIEM.
Organizations achieve measurable MTTD reduction, consistent MTTR improvement, and efficient scalable threat hunting through storage efficient analysis and bandwidth optimization.
Is network metadata analysis compliant with privacy regulations?
Network metadata analysis supports compliance when organizations implement strict controls. Privacy compliant logging focuses on metadata instead of content, aligning with GDPR network metadata requirements.
Clearly defined retention policies flows, protected audit trail metadata, and controlled metadata enrichment minimize exposure. Continuous compliance monitoring network oversight and remediation of cloud log gaps and endpoint blind spots ensure lawful and defensible operations.
The Value of Network Metadata Analysis Moving Forward
Network metadata analysis enables scalable threat detection, faster forensics, and compliance-aligned visibility without storing full payloads. As networks span cloud, IoT, and OT systems, we rely on Network Threat Detection to baseline encrypted traffic, detect anomalies, and close endpoint blind spots.
Investing in enriched flow records, AI-enhanced metadata, and behavioral analytics reduces MTTD and strengthens resilience. Metadata forms the foundation for modern NDR and threat hunting. Start strengthening your Network Threat Detection strategy today.
References
- https://nationalsecurity.vt.edu/content/nationalsecurity_vt_edu/en/about/news/2024/third-workshop-report-on-value-of-capturing-metadata-on-network-traffic-to-enhance-threat-detection
- https://safecomputing.umich.edu/protect-the-u/protect-your-unit/network-security-management/network-security-threat-detection