Iran-linked threat actors are actively targeting and disrupting U.S. critical infrastructure by exploiting exposed industrial controllers, and your best chance to stop them is by seeing them first. Federal agencies confirmed it in April 2026. Hackers affiliated with Iran’s IRGC are probing internet-facing programmable logic controllers (PLCs), manipulating data on control screens, and causing real operational shutdowns. They’re not using magic.
They’re walking through wide-open digital doors, thousands of them, right here in the United States. This isn’t a speculative threat. It’s a current campaign where network threat detection shifts from a best practice to the critical front line. Keep reading to understand the scale of exposure and the practical steps you can take before the next alert hits.
Key Statistics on Industrial Network Threats
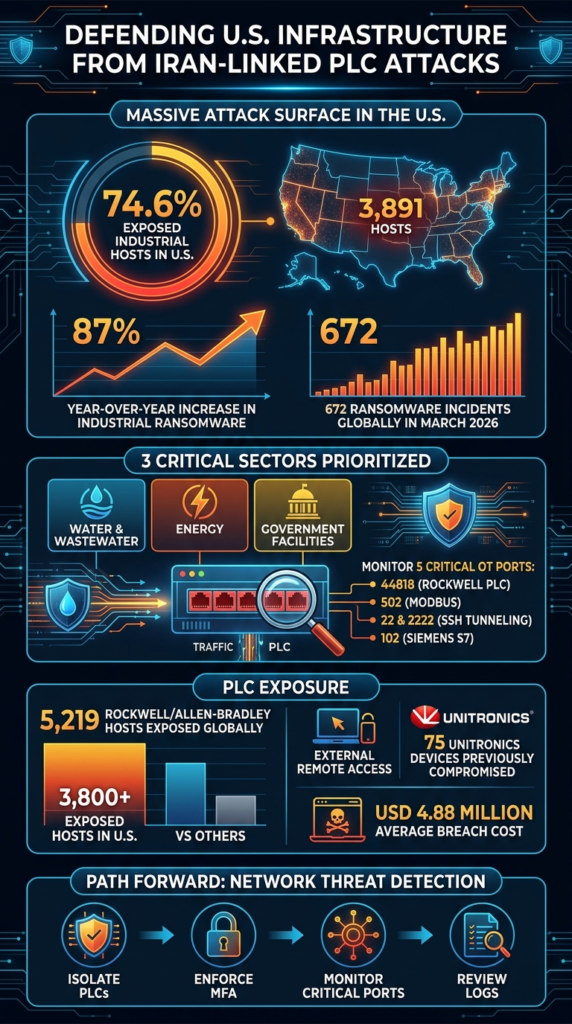
- The attack surface is massive and domestic, with over 3,800 exposed industrial hosts in the U.S. alone.
- These attacks succeed through operational simplicity, targeting known weaknesses like default credentials and unsecured ports.
- Proactive network visibility, not just prediction, is the most effective defense against these geopolitical campaigns.
- 5,219 – Total internet-exposed Rockwell/Allen-Bradley hosts identified globally, indicating a massive attack surface for unauthorized access.
- 74.6% – The portion of exposed industrial hosts located within the United States, making it the primary target for geographic-based campaigns.
- 3 – Specific critical sectors targeted in CISA Advisory AA26-097A, including Water & Wastewater, Energy, and Government Facilities.
- 5 – Critical OT-related ports (including 44818 and 502) that defenders must monitor to prevent PLC manipulation.
- At least 75 – Number of Unitronics devices compromised in previous Iran-linked campaigns, proving the repeatability of these tactics.
- 1,693 – Total ransomware attacks targeting industrial organizations in 2024, showcasing a relentless focus on physical disruption.
- 87% – The year-over-year increase in industrial ransomware incidents, signaling a rapid escalation in threat actor activity.
- 672 – Ransomware incidents reported worldwide in March 2026 alone, demonstrating the high volume of concurrent threats.
- 40% – Share of monthly ransomware attacks linked to just the top three threat groups, showing high concentration in actor capability.
- USD 4.88 million – The average global cost of a data breach in 2024, highlighting the severe financial impact of successful network penetrations.
5,219 Rockwell/Allen-Bradley Hosts Exposed Globally
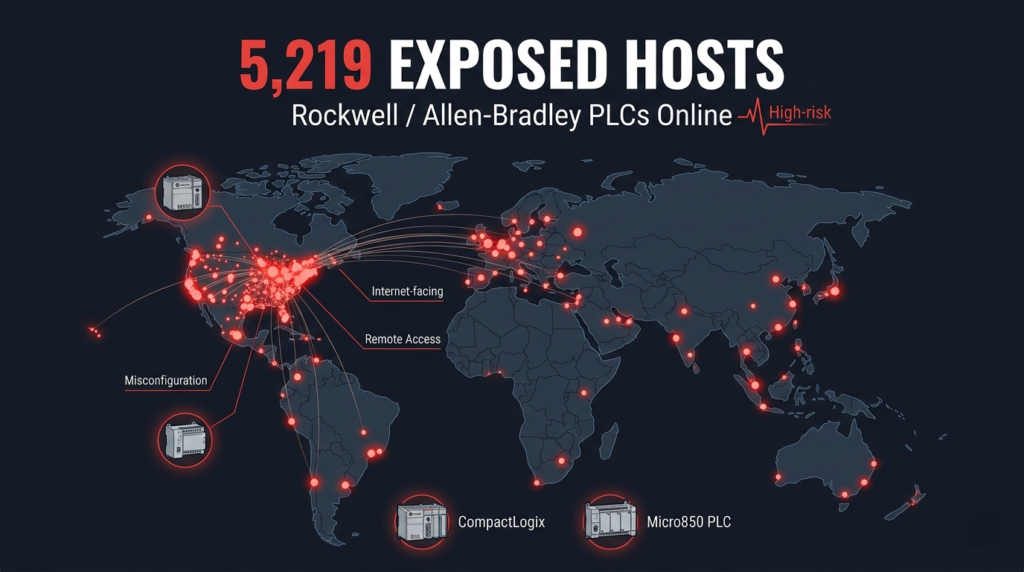
According to a Censys ARC Advisory report published on April 7, 2026, a total of 5,219 Rockwell/Allen-Bradley hosts have been identified as directly exposed to the public internet. This exposure rarely begins with malicious intent; more often, it is the result of operational needs that overlook security considerations.
For example, external contractors may require remote access to fix a pump failure at 2 a.m., or maintenance teams may forget to close temporary gateways.
The exposure of thousands of PLCs, including CompactLogix and Micro850 units, reflects a collision between operational convenience and security oversight. Because these devices are directly internet-facing, attackers such as the CyberAv3ngers group do not require sophisticated zero-day exploits.
According to Censys analysis, threat actors can simply use vendor engineering software like Studio 5000 Logix Designer to interact with PLCs once access is obtained via basic searches on Shodan or other sensor search engines.
74.6% of Exposed Industrial Hosts Are in the United States
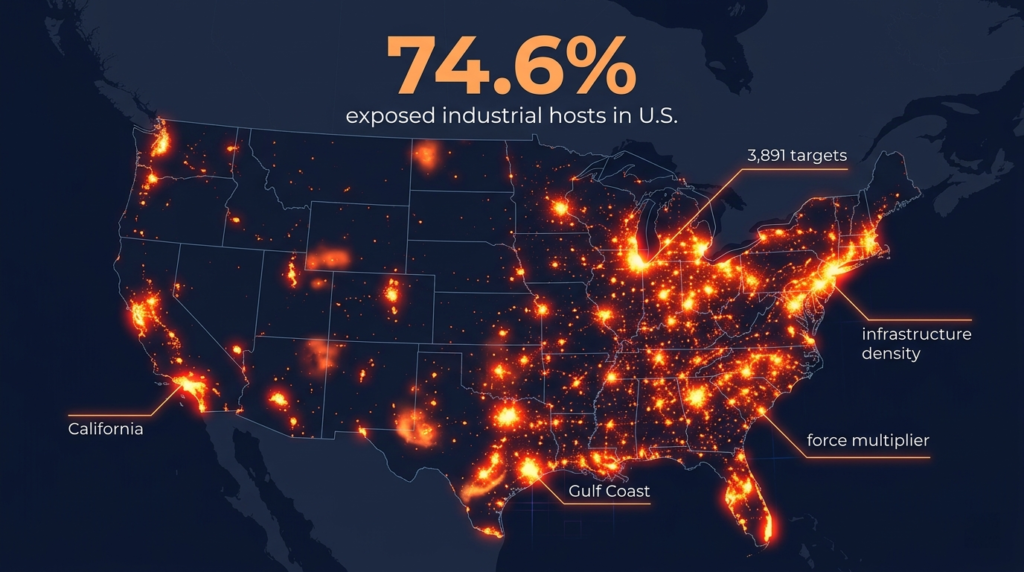
Based on data from the Censys ARC advisory / exposure assessment (April 7, 2026), 74.6% of all exposed industrial hosts are located in the United States, representing 3,891 specific targets. This high concentration is not coincidental, it reflects the density of infrastructure and the widespread use of legacy control systems across water, energy, and manufacturing networks.
According to warnings from CISA, this density acts as a “force multiplier” for attackers. Nation-state actors such as Iran have clear geopolitical motivations to target this region. With concentrated IP ranges, attackers can automate scanning efforts.
CISA warns that compromising a single device within a cluster can enable rapid lateral movement across networks that are supposed to be segmented, increasing the likelihood of successful “spray-and-pray” attacks.
Three Critical Infrastructure Sectors Are Prioritized

In CISA Advisory AA26-097A, released on April 7, 2026, cybersecurity authorities explicitly prioritized three critical infrastructure sectors: Government Facilities, Water & Wastewater Systems, and Energy. This selection is deliberate, as these sectors represent societal pressure points where disruption would cause maximum public impact.
Each sector has its own unique risk profile, but they share a common thread of using similar industrial control systems.
| Sector | Primary Risk Factor | Typical Industrial Asset Targeted |
| Water & Wastewater | Unmonitored remote access for SCADA systems | Unitronics & Rockwell PLCs |
| Energy | Protocol manipulation for grid stability | Power generation controllers, RTUs |
| Government | Service disruption & symbolic impact | Building management systems, HVAC controls |
The ultimate objective, as noted in the advisory, is to interact with PLCs to alter operational logic or manipulate HMI displays to conceal malicious actions.
Five Specific OT-Related Ports Demand Scrutiny
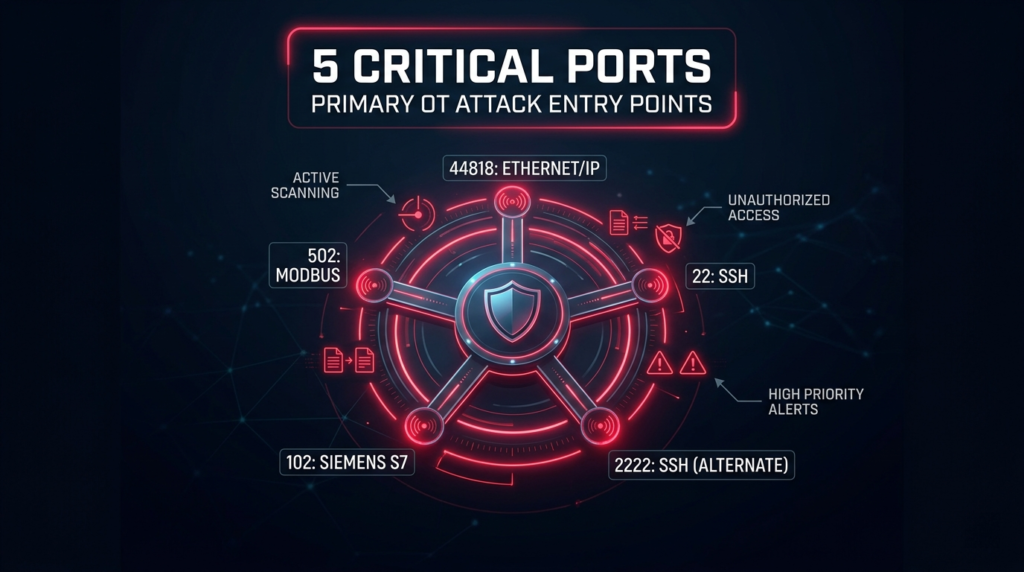
CISA Advisory AA26-097A instructs network defenders to closely monitor five specific ports that serve as primary entry points for OT attacks:
- Port 44818: Primary channel for Rockwell PLC commands (EtherNet/IP)
- Port 502: Used for Modbus protocol, often lacking authentication
- Ports 22 & 2222: Used for SSH tunneling and persistent remote access
- Port 102: Targets Siemens S7 PLC communications
According to CISA, threat actors actively scan these ports to identify “low-hanging fruit.” Connection attempts from unknown IP addresses or at unusual times should be immediately flagged as high-priority threat signals by security systems.
At Least 75 Unitronics Devices Were Previously Compromised
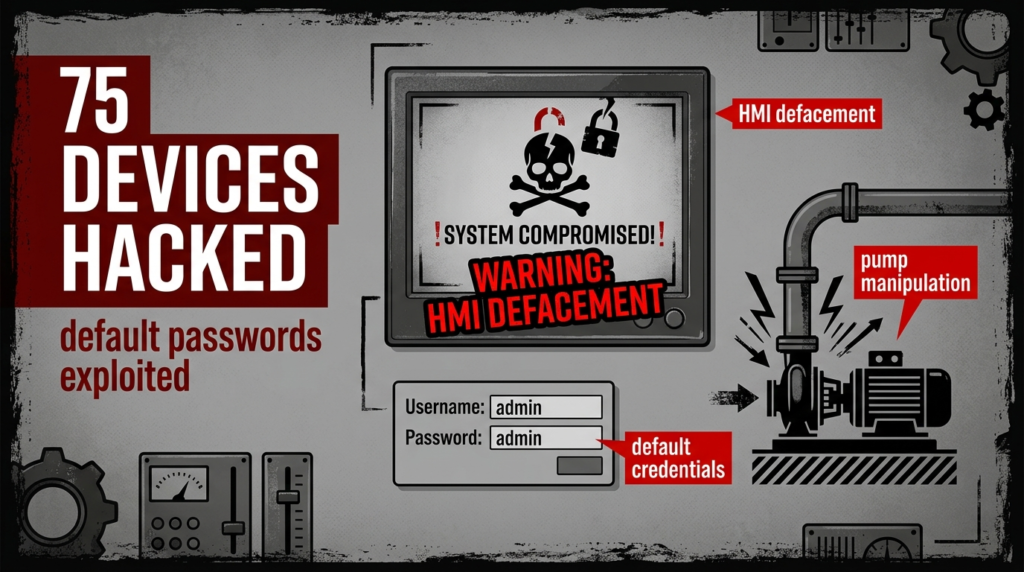
Referring to earlier Iran-linked attack campaigns, Censys (citing CISA AA23-335A) reported that at least 75 Unitronics devices were successfully compromised. Attackers relied on a simple yet effective tactic: exploiting default manufacturer passwords that had never been changed.
This historical incident serves as a blueprint for current Rockwell/Allen-Bradley attacks. Attackers gained access, defaced HMI screens with anti-Israel messages, and altered pump configurations. According to Censys analysis, this campaign functioned as a “live-fire” exercise for Iranian proxy hackers to determine which tactics generated the most disruption and alerts in smaller utilities with limited IT resources.
1,693 Industrial Ransomware Attacks Occurred in 2024

The Dragos 2025 OT Cybersecurity Year in Review report (February 25, 2025) revealed that 1,693 ransomware attacks targeted industrial organizations throughout 2024. This figure highlights a shift in criminal motivation, from data theft to the disruption of physical operations.
Attackers recognize that pressure to pay ransom increases significantly when safety systems or production processes (such as chemical mixing or pipeline valves) are taken offline. According to Dragos, IT/OT convergence has created new entry points, often starting with phishing emails in business networks and spreading into production environments that lack adequate antivirus or logging systems.
An 87% Year-over-Year Increase Changes Everything
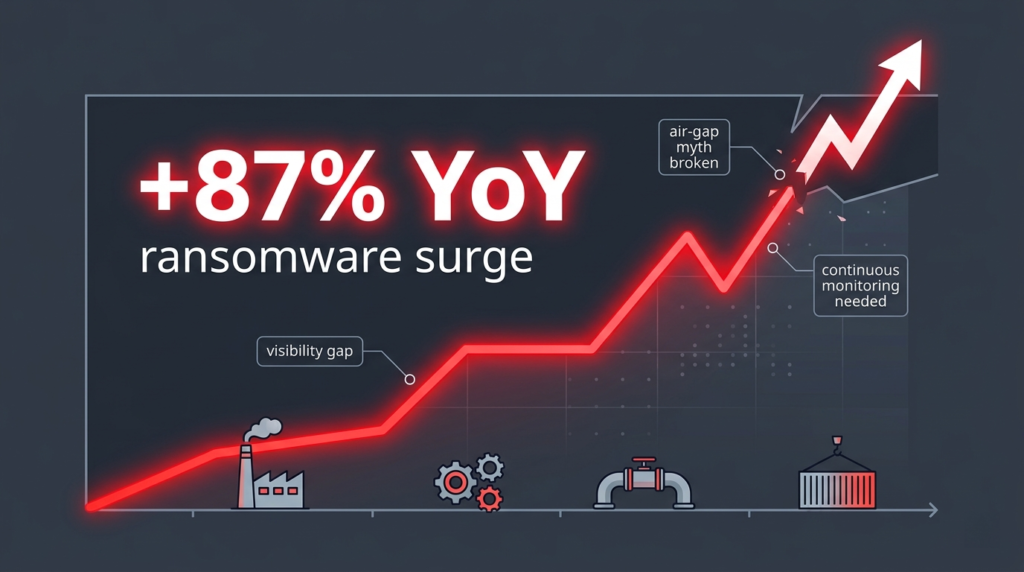
An 87% year-over-year increase in industrial ransomware attacks, as documented in the Dragos 2025 report, signals that traditional defense models are no longer sufficient. The myth of “air-gapping” has collapsed in the Industry 4.0 era, where nearly all systems are directly or indirectly connected.
Dragos emphasizes that visibility is the number one gap in industrial defense. With attacks increasing by 87%, organizations can no longer rely solely on reactive patching. The focus must shift to continuous network threat detection to identify protocol anomalies, such as Modbus commands originating from servers that have never previously communicated with PLCs.
672 Monthly Ransomware Incidents Reveal the Volume
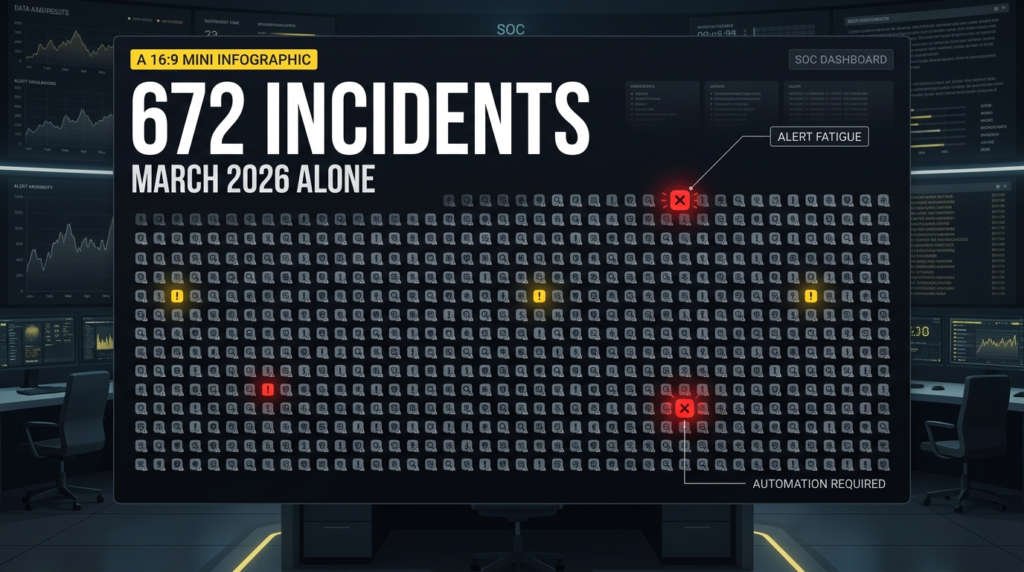
According to Check Point Research, as cited by Infosecurity Magazine (April 2026), 672 ransomware incidents were recorded globally in March 2026 alone. This massive volume creates “noise” that can obscure more targeted and sophisticated PLC intrusions.
The frequency of attacks renders manual monitoring obsolete. Security analysts cannot realistically triage hundreds of global incidents while also detecting subtle anomalies on ports like 44818. This reinforces the need for automation through Network Detection and Response (NDR) platforms to distinguish between background noise and targeted breach signals.
40% of Ransomware Is Concentrated Among Three Groups
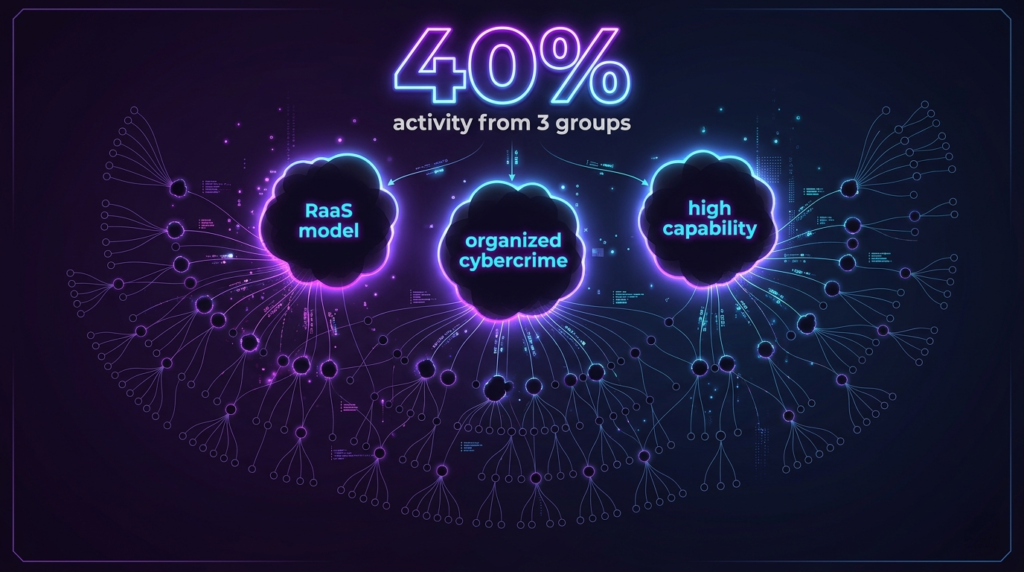
Check Point Research data (April 2026) shows that 40% of global ransomware activity is concentrated among just three major groups. This reflects the professionalization of cybercrime through the Ransomware-as-a-Service (RaaS) model, where elite developers lease their attack platforms to affiliates.
According to Infosecurity Magazine, this concentration means groups like LockBit and ALPHV have substantial R&D budgets to discover new vulnerabilities in SCADA software. They increasingly target the energy sector as a high-yield objective, forcing defenders to confront not just opportunistic hackers, but highly organized criminal enterprises.
A USD 4.88 Million Breach Cost Justifies OT Security Investment
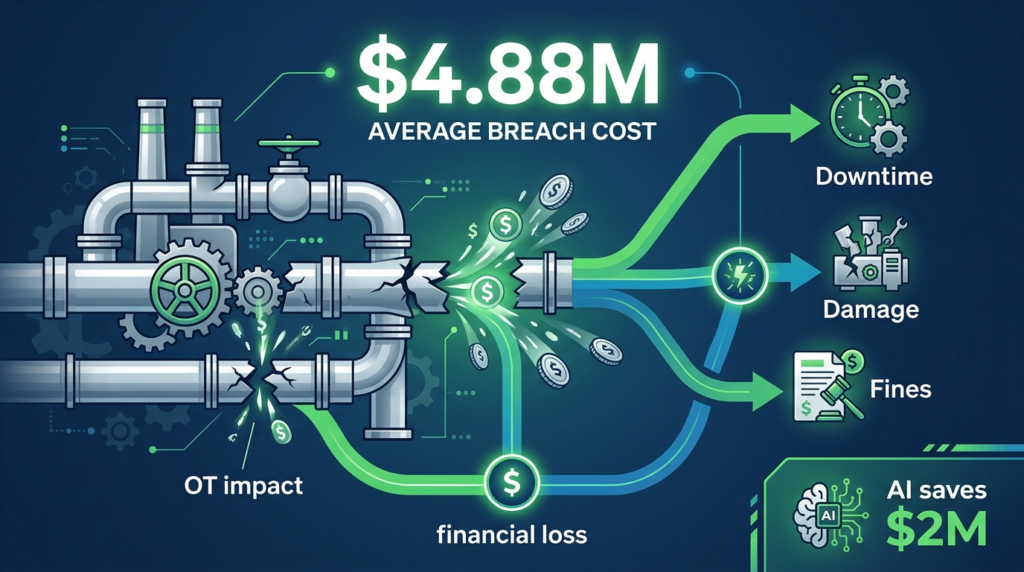
According to the IBM Cost of a Data Breach Report 2024 (July 30, 2024), the global average cost of a data breach has reached USD 4.88 million. For industrial organizations, this cost can be significantly higher when factoring in production downtime, physical equipment damage, and regulatory fines.
IBM data shows that organizations extensively using security AI and automation save nearly USD 2 million compared to those that do not. This provides a clear financial justification for investing in network segmentation and OT threat detection.
Visibility is no longer just a technical expense, it is a strategic business decision to protect profitability and operational resilience.
The Path Forward for Network Threat Detection
This isn’t just about nation-state actors, it’s about exposure. Thousands of industrial devices remain visible, reachable, and vulnerable. The priority isn’t predicting attackers, but removing the conditions that enable them.
Start with the basics: isolate PLCs from the internet, enforce MFA, monitor critical ports, and review logs for known indicators. Then go further, adopt continuous monitoring. Assume your network is being probed, and focus on detecting and stopping it early.
Ready to see what’s on your network before they do? Contact our team to start a proactive exposure assessment.