We’ve been watching the Iran-linked PLC attacks unfold, and here’s what stopped us cold: this isn’t a sophisticated espionage campaign. It’s a walkthrough. Federal agencies confirmed in early April that threat actors are probing internet-facing industrial controllers, and we found thousands of those controllers just sitting there, exposed, right in the United States.
THREE SURPRISING FINDINGS
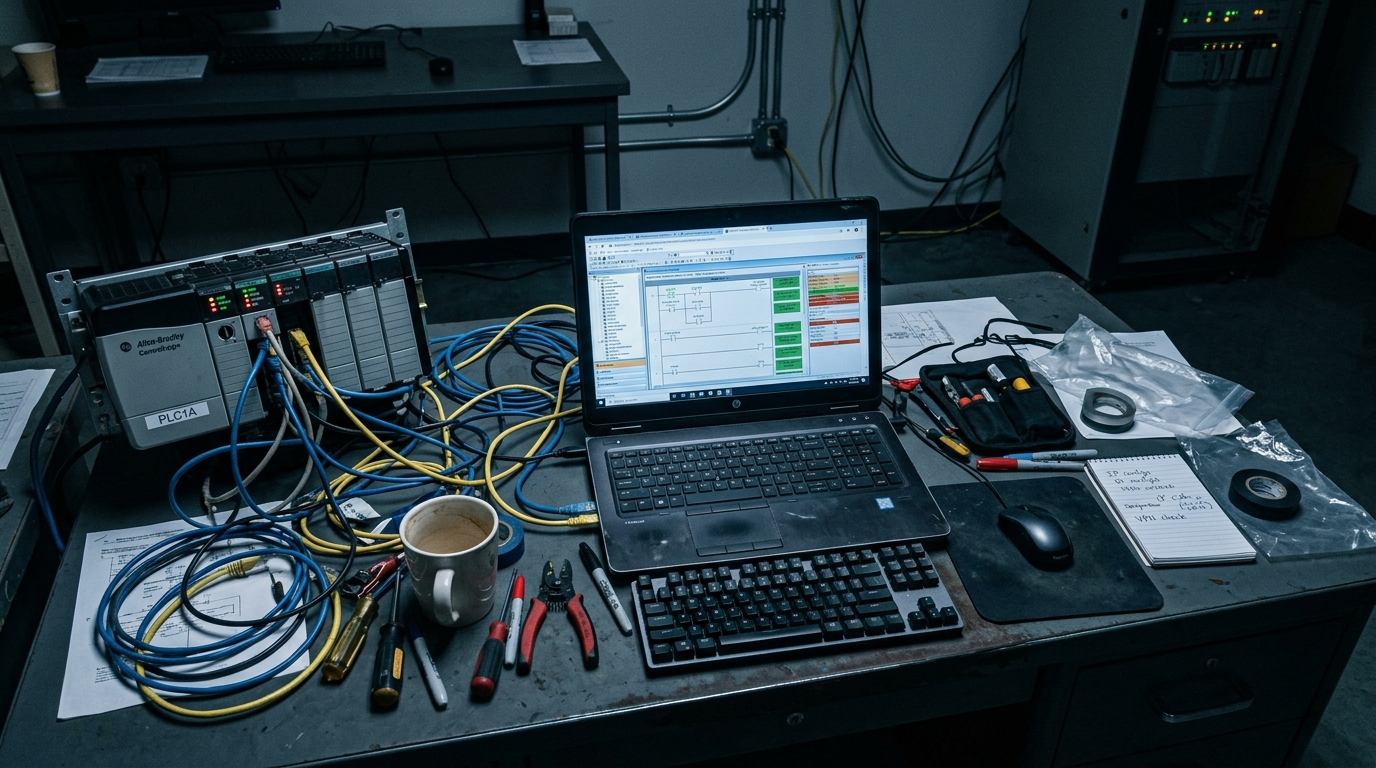
The exposure problem is bigger than any single threat actor We expected to write about one group’s tactics. Instead, we found 5,219 internet-facing Rockwell/Allen-Bradley hosts globally, with 74.6% located in the United States. That’s 3,891 industrial devices that attackers don’t need to break into, they just need to reach.
This isn’t only an IT security problem When we looked at the Dragos data, the physical reality hit us: 1,693 ransomware attacks on industrial organizations in 2024, and according to Dragos’s incident response data, 75% of OT ransomware cases caused partial shutdowns while 25% caused full operational shutdowns. This is about pumps stopping, valves failing, and screens going dark.
The campaign is operationally simple, not technically advanced CISA’s advisory made one thing brutally clear: attackers are using legitimate vendor tooling and probing standard OT ports like 44818 and 502. That means basic visibility and exposure reduction matter more than hunting for zero-day exploits.
KEY FINDINGS
Our analysis draws from five primary sources: CISA, Censys, Dragos, Check Point Research, and IBM. Here’s what we found:
- 5,219 internet-exposed Rockwell/Allen-Bradley hosts identified globally (Censys ARC advisory, April 7, 2026)
- 74.6% of that exposure (3,891 hosts) located in the United States (Censys ARC advisory, April 7, 2026)
- 3 critical infrastructure sectors explicitly targeted: Government Services/Facilities, Water & Wastewater Systems, and Energy (CISA Advisory AA26-097A, April 7, 2026)
- 5 OT-related ports defenders must scrutinize: 44818, 2222, 102, 22, and 502 (CISA Advisory AA26-097A, April 7, 2026)
- At least 75 Unitronics devices compromised in the previous Iran-linked campaign, using default passwords (Censys citing CISA AA23-335A, referenced April 2026)
- 1,693 ransomware attacks targeting industrial organizations in 2024 (Dragos 2025 OT Cybersecurity Year in Review, February 25, 2025)
- 87% year-over-year increase in industrial ransomware incidents (Dragos 2025 OT Cybersecurity Year in Review, February 25, 2025)
- 672 ransomware incidents reported worldwide in March 2026 alone (Check Point Research via Infosecurity Magazine, April 9-10, 2026)
- 40% of March’s ransomware attacks linked to just the top three threat groups (Check Point Research via Infosecurity Magazine, April 9-10, 2026)
- USD 4.88 million average global cost of a data breach (IBM Cost of a Data Breach Report 2024, July 30, 2024)
WHAT THIS MEANS FOR SECURITY LEADERS AND SOC TEAMS
Here’s the uncomfortable truth we keep coming back to: most OT risk starts before the exploit. You don’t need perfect threat prediction. You need earlier visibility into exposed PLCs, unusual protocol traffic on ports like 44818 and 502, remote-access pathways you didn’t authorize, and cross-environment attack signals before manipulation becomes downtime.
For critical infrastructure operators, water, energy, government facilities, the message is straightforward. The attackers are scanning. They’re using Shodan the same way your contractors do. They’re looking for default credentials and open engineering ports. Your job isn’t to build an impenetrable fortress. It’s to see the probe, understand its intent, and block it before the project file gets extracted or the HMI display gets manipulated.
EXPERT QUOTE
Attributed to company founder (cybersecurity expert with decades of OT/ICS experience):
“Geopolitical cyber campaigns succeed not because nation-states have better exploits, but because industrial environments are still reachable, weakly segmented, or insufficiently monitored. We keep seeing the same pattern: exposed PLCs, default credentials, open remote-access pathways. Defenders don’t need perfect prediction. They need earlier visibility into exposed devices and unusual protocol traffic before manipulation becomes downtime. That’s the gap we built Network Threat Detection to close.”
METHODOLOGY NOTE
Our findings synthesize primary-source data from CISA Advisory AA26-097A (April 7, 2026), Censys ARC exposure assessment (April 7, 2026), Dragos 2025 OT Cybersecurity Year in Review (February 25, 2025), Check Point Research March 2026 threat update (reported April 9-10, 2026), and IBM Cost of a Data Breach Report 2024 (July 30, 2024).
This story isn’t ultimately about Iran. It’s about exposure. Thousands of industrial devices are visible, reachable, and vulnerable, and geopolitical actors are simply the most motivated exploiters of that condition. The defense isn’t predicting which nation-state attacks next. It’s removing the conditions that make attacks possible in the first place.
Read the complete analysis with full methodology on our blog → Network Threat Detection: Your Best Defense Against Iran-Linked PLC Attacks
Learn more about our network threat detection platform → OT Network Detection & Response Solutions