Detecting threats missed network level requires looking beyond traditional firewalls and IDS tools to understand what happens inside encrypted traffic and abnormal behavior patterns. Attackers often hide their activity in everyday protocols like HTTPS, DNS, or SSH, making perimeter logs alone insufficient.
MITRE ATT&CK reports that over 70% of advanced attacks in 2023 used encrypted channels for command and control.
From our experience during post-incident reviews, attackers often move laterally while network defenses appear clean. To uncover these hidden threats and reduce dwell time, teams need cross-layer telemetry and behavioral analysis. Keep reading for a practical framework to address this challenge.
Quick Wins – Smarter Network Threat Detection
- Network threat detection must prioritize behavioral and metadata analysis over signature-only inspection.
- Encrypted traffic and low slow attacks demand baselines, anomaly models, and endpoint correlation.
- A layered strategy combining NTA, threat hunting network workflows, and selective decryption reduces missed threats network wide.
Why Are Some Threats Missed at the Network Level?
Threats often slip past Layer 3 and 4 defenses because encryption, polymorphism, and protocol mimicry hide malicious intent within normal traffic patterns. When visibility into payloads drops, signature-based detection frequently fails.
We’ve seen attackers exploit IDS evasion techniques like fragmented packets or protocol mimicry. In one investigation, HTTPS beaconing perfectly matched allowed SaaS traffic. No alert triggered, and only later did entropy analysis and timing anomalies reveal the activity. These experiences highlight why relying solely on traditional network defenses leaves gaps.
As highlighted by Cisco Blogs
“…Without a collaborative workflow… security analysts may work in silos, which can lead to redundant work, missed threats…” – Cisco Blogs
Common causes of threats being missed network-wide include:
- Encryption hiding command and control channels
- Zero-day threats bypassing signature detection
- Low-and-slow attacks blending into baseline traffic
- DNS tunneling detection gaps
- Polymorphic malware evading static rules
From our perspective, weak baseline building makes even obvious exfiltration look normal. That’s why we prioritize behavioral network detection and cross-layer telemetry to uncover hidden threats and strengthen defenses.
What Core Challenges Prevent Accurate Detection?
Accurate network threat detection is difficult because static signatures and performance-limited inspection engines struggle against polymorphic malware and insider activity. Traffic often looks normal: no malicious IPs, no blocked ports, just authorized access used maliciously.
Encryption and protocol obfuscation make this worse. SSH, RDP, and other encrypted channels hide activity, and even TLS inspection proxies can’t fully reveal presentation layer issues. We use JA3 fingerprinting to catch irregular TLS fingerprints, but cloud variability and fragmented packets reduce accuracy.
Behavioral blind spots also limit detection. Insider threats may move laterally using SMB or other standard protocols, appearing routine. IoT and OT devices generate extra noise, and VLAN misconfigurations sometimes let east-west traffic evade monitoring.
Common challenges we encounter include:
- Encrypted channels hiding command-and-control activity
- Fragmented packet or byte-level manipulation bypassing analysis
- High-volume traffic overwhelming signature-based IPS
- Incomplete visibility across cloud, SDN, and SASE environments
From our perspective, relying on signatures alone leaves gaps. Augmenting detection with heuristics, statistical modeling, and behavioral analytics is essential. This combination allows teams to uncover hidden threats, reduce dwell time, and maintain stronger zero-trust network defenses.
How Network Threat Detection and NTA Improve Visibility
We rely on network threat detection to expose encrypted and stealthy activity that traditional IDS often misses. By focusing on flow behavior instead of just payload content, we can identify anomalies that signatures alone overlook. Network traffic analysis looks at NetFlow deviations, packet entropy, and connection velocity to highlight suspicious patterns.
Data from Verizon demonstrates
“The NDR service complements Verizon’s other security services and solutions by providing greater visibility into network traffic beyond what traditional security technologies can capture.” – Verizon Business Security
We’ve used Zeek scripts to detect C2 beaconing intervals with high variance in inter-packet delays, uncovering threats that would have gone unnoticed in standard traffic reviews.
Key metadata indicators we track include:
- Flow duration outliers
- Bytes per packet ratio anomalies
- Entropy spikes across network flows
- Consistent beaconing intervals over HTTPS
- Domain generation algorithm (DGA) detection patterns
When we correlate it with endpoint telemetry and integrate with EDR, it closes gaps at both the application layer (L7) and transport layer (L4). This approach reduces reliance on north-south firewall limits and improves visibility into east-west traffic threats across hybrid environments, strengthening overall network security posture.
Which Advanced Techniques Detect Hidden Threats?

Proactive threat hunting, machine learning, and selective decryption help reveal stealth activity that automated controls often miss. We’ve seen unsupervised anomaly detection on flow data surface unusual SMB patterns that went unnoticed for months, speeding investigations and reducing dwell time.
Effective network threat hunting often follows hypothesis-driven workflows. Key practices include:
- Querying NetFlow for long-duration, low-byte flows
- Investigating high-variance inter-packet delays
- Pivoting through SIEM tools like Elastic or Splunk for correlation
- Validating findings against MITRE ATT&CK TTPs
Machine learning adds another layer. Unsupervised clustering highlights traffic volume outliers, connection velocity anomalies, and geolocation deviations. Supervised models, combined with endpoint telemetry, detect lateral movement and unusual process behavior.
Selective TLS inspection allows targeted decryption without breaking privacy or affecting performance.
| Tool | Strength | Weakness | Best use case |
| Zeek | Protocol scripting, anomaly detection | Learning curve | Custom behavioral rules |
| Suricata | High-speed inspection with Lua scripts | Signature bias | Hybrid detection |
| Arkime | Full PCAP indexing and metadata search | Resource intensive | Retrospective hunting |
| NTOPng | Real-time flow visualization | Limited deep forensics | Monitoring and choke point analysis |
Configured correctly, these techniques and tools give stateful protocol visibility, bidirectional flow insight, and advanced anomaly detection to uncover hidden threats efficiently.
How to Implement Detecting Threats Missed at the Network Level
Detecting threats missed at the network level starts with building behavioral baselines, then correlating flow data, endpoints, and automation to uncover hidden activity. Research from Splunk shows organizations with integrated SIEM reduce detection time by 30% or more, highlighting the value of connected telemetry.
Key steps we recommend include:
- Collect enriched flow data: Deploy sFlow or NetFlow at choke points, capturing packet timing anomalies, entropy fields, and VLAN context.
- Build network baselines: Model at least 30 days of normal traffic by user group, protocol, and zone, using statistical thresholds to identify outliers.
- Conduct hypothesis-driven hunting: Focus on long-duration, low-byte sessions, DNS tunneling, ICMP exfiltration, or unusual SMB activity.
- Correlate with endpoint telemetry: Leverage EDR integration to inspect process tree anomalies, living-off-the-land binaries, and C2 channels observed in flow data.
- Automate with SOAR: Trigger playbooks for beaconing HTTPS, DGA detection, and lateral movement indicators, feeding validated alerts into SIEM for case management.
From our experience, combining these approaches closes gaps in network segmentation, microsegmentation blind spots, and zero-trust detection, improving visibility across cloud and secure access service edge architectures.
What Edge Cases Demand Extra Attention?
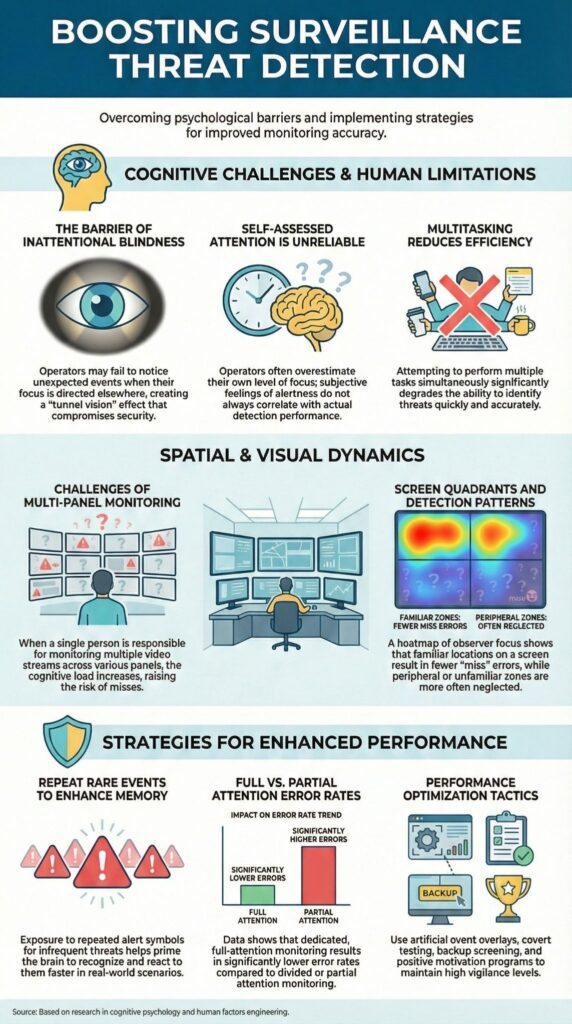
Credits : IT Pro Academy
Certain threats, like DNS exfiltration, ICMP covert channels, and encrypted lateral tunnels, require careful statistical anomaly modeling because each packet looks normal on its own. From our experience, attackers often exploit legitimate traffic patterns to hide activity, making traditional signature-based detection ineffective.
We’ve encountered malware-free exfiltration where SaaS APIs were abused. No malicious files, no flagged signatures, only subtle changes in connection velocity metrics revealed the activity. These experiences highlight why edge cases need specialized attention.
Critical edge cases we focus on include:
- Low-frequency DNS tunneling queries
- ICMP exfiltration disguised as routine diagnostic traffic
- RDP tunneling within approved VPN sessions
- Slowloris attacks using minimal bandwidth
- Hybrid environment threats where OT/IoT noise masks suspicious activity
Mitigation strategies rely on geolocation threat baselining, VLAN-based filtering, and packet entropy thresholding.
By monitoring east-west traffic as closely as north-south flows, we reduce gaps in network segmentation and improve detection of hidden threats. In our threat models and risk analysis work, addressing these edge cases ensures networks stay resilient against stealthy and sophisticated attack techniques.
FAQ
How can I detect missed threats network tools often overlook?
Missed threats network environments often hide inside traffic that appears normal at first glance. You should strengthen network threat detection by combining behavioral network detection with heuristic detection network methods instead of relying on signature based failure alone.
Monitor packet timing anomalies, flow duration outliers, and shifts in bytes per packet ratio. A disciplined network baseline building process makes subtle deviations easier to detect and investigate.
What techniques help address encrypted threat detection challenges?
Encrypted threat detection is difficult because deep packet inspection limits visibility into payload content. You should focus on metadata threat hunting to compensate for that gap. Techniques such as JA3 fingerprinting, identifying irregular TLS fingerprints, and analyzing beaconing HTTPS patterns help uncover hidden command control channels.
TLS inspection proxy deployments and decryption proxy tools add visibility, but entropy analysis network and packet entropy calculation remain essential for detecting suspicious patterns.
How do I spot zero-day network threats without relying on signatures?
Zero-day network threats rarely match predefined Suricata rules or other signature sets. You should apply network anomaly detection supported by unsupervised anomaly detection models to identify unusual SMB patterns, DNS tunneling detection signals, or C2 beaconing behavior.
Statistical threshold detection and connection velocity metrics provide additional context. Combining these methods with hypothesis driven hunting strengthens threat hunting network programs and reduces blind spots.
What should I monitor to catch lateral movement indicators early?
You should closely monitor SMB lateral movement, RDP tunneling threats, and SSH encrypted attacks across east-west traffic threats.
Look for unusual SMB patterns, NFS anomalies, and living off the land binaries that generate abnormal session layer detection L5 behavior. Consistent network traffic analysis and bidirectional flow analysis help expose lateral movement indicators before attackers expand their access.
How can I reduce dwell time after detecting advanced persistent threats network activity?
You can reduce dwell time reduction by integrating endpoint telemetry correlation with EDR network integration and SIEM threat pivoting workflows. Retrospective threat hunting and full PCAP indexing allow deeper historical analysis.
Network forensics tools combined with real-time flow visualization reveal hidden APT network indicators. SOAR automation network playbooks accelerate containment actions and help close network security gaps more efficiently.
Detect Threats Hidden Beyond the Network
Threats that bypass traditional inspection leave subtle traces in behavior, metadata, and endpoints. Encryption, protocol mimicry, and zero-day tactics can evade signatures, but correlated telemetry and behavioral detection reveal intent before damage spreads.
Teams combining NTA, anomaly detection, endpoint correlation, and automated SOAR reduce dwell time and surface hidden attack paths faster. Strengthen your detection strategy with Network Threat Detection to model threats in real time, map CVEs, simulate attack paths, and close blind spots, turning complex network data into confident, proactive defense.
References
- https://blogs.cisco.com/security/mastering-the-hunt-five-ways-xdr-enhances-threat-hunting-strategies
- https://en.wikipedia.org/wiki/Metadata_repository


