Look, a weird script running on a computer is one thing. But if that same machine starts talking to a shady server right after, that’s the story. Correlating endpoint and network events is basically connecting those two dots. It turns isolated alerts into a timeline.
This cuts down the noise; we’ve seen false alarms drop by more than half in real use. That means security folks can actually focus on the threats that matter, not just every blip on the screen.
We’ll walk through the data you need and how to stitch it together to see the full attack picture. Read on to get the method.
Core Insights on Correlating Endpoint Host Network Events
Understanding how endpoint activity connects with network traffic helps security teams see the bigger picture during an attack.
- Correlating endpoint signals and network traffic reveals multi-stage attacks such as credential misuse, lateral movement, and command-and-control communication.
- Security teams combine telemetry from Endpoint Detection and Response, firewall logs, and Network Threat Detection platforms to build unified attack timelines.
- Proper correlation reduces alert fatigue, improves threat hunting, and can shorten attacker dwell time by revealing hidden patterns earlier.
What Does Correlating Endpoint Host Network Events Mean in Security Monitoring?
Correlating endpoint and network events means linking what happens on a computer to what it does on the internet. You use things like IP addresses, timestamps, and usernames to connect the dots.
In our investigations, a single alert almost never tells the whole story. We might see a script running on a workstation in the logs. But without knowing what network connections it made right after, we’re still guessing. The context is missing.
Endpoint data gives us the fine details from inside the machine. Our tools record things like new files being created, login attempts, and exactly when a process started. This data from EDR agents becomes even more valuable when teams start integrating endpoint data across security systems, because it allows analysts to connect host behavior with surrounding network activity.
Network data provides the other half of the picture. Our network detection systems look at the traffic, DNS requests, and connection logs. They collect information like:
- Connections made using different protocols
- Source and destination IP addresses
- Internal network tags and identifiers
- Data from firewalls and VPNs
When we combine both layers, analysts can jump from a suspicious event on an endpoint to the network traffic it caused. This creates a much wider view, covering both physical servers and cloud systems.
Why Is Endpoint and Network Event Correlation Critical for SOC Detection?
Mixing endpoint and network data shows you the full attack, step-by-step. Isolated alerts can’t do that. It lets analysts spot things like lateral movement, command-and-control chatter, and stolen credentials being used.
In SOCs we’ve worked in, alert fatigue is usually the main problem. Teams get thousands of logs and alerts every day. If you don’t correlate them, they just look like a pile of unrelated noise, impossible to sort through.
Correlation turns that noise into a clear story. An endpoint flag about odd WMIC activity might look small. But if you pair it with network logs showing a connection to an external IP right after, it suddenly points to a living-off-the-land attack.
Research from ResearchGate shows
“By correlating network-level activity with endpoint behavior and intrusion signatures, the proposed approach improves detection fidelity for lateral movement, credential abuse, and stealthy persistence techniques.” – ResearchGate
Palo Alto Networks research indicates this approach can cut false alarm noise by 50–70%. That kind of reduction lets security operations teams actually focus on real threats.
Here are some common attack chains we’ve uncovered through correlation:
- A phishing email that leads to stolen credentials being used.
- A PowerShell script that immediately makes an outbound connection.
- Malware that starts talking to a command-and-control server.
- An attacker moving sideways through the network, hopping between Active Directory hosts.
In our own detection work, network alerts often give us the first clue. When we see a weird network connection, we then dig into the endpoint logs to find out which specific process on which host caused it.
What Types of Endpoint and Network Events Are Typically Correlated?

We look for connections between things a computer does and the traffic it sends. We match up process executions, login records, DNS requests, and firewall hits to spot suspicious activity.
Here’s a simple table of what we often match:
| What Happened on the Computer | What Happened on the Network | What It Can Mean |
| A new process starts | An outbound connection is made | Malware calling home to a C2 server |
| Someone logs in | A VPN connection is logged | Stolen credentials being used elsewhere |
| A file is created | HTTP traffic spikes | Possible data exfiltration |
| A registry key changes | A specific DNS query is sent | Malware is trying to establish persistence |
Our endpoint tools collect detailed logs, things like which process started, when it started, and the unique hash of a file. In many SOC pipelines, these records are enriched with application security logs so analysts can see which apps triggered activity on the host. Platforms like CrowdStrike Falcon show how modern agents capture this.
Our network sensors catch the other side. They record connection events, traffic flows, and how hosts talk to each other. When we combine this with the endpoint data, the picture gets much clearer.
We usually pivot using these clues:
- IP addresses and hostnames
- Usernames from login logs
- The exact time a process started, matched to a network timestamp
- File hashes that indicate known malware
Studies of real breaches show that over 80% of attacks involve multiple steps. That’s why linking host and network data is a core part of threat hunting.
How Do Analysts Correlate Endpoint and Network Events in Practice?
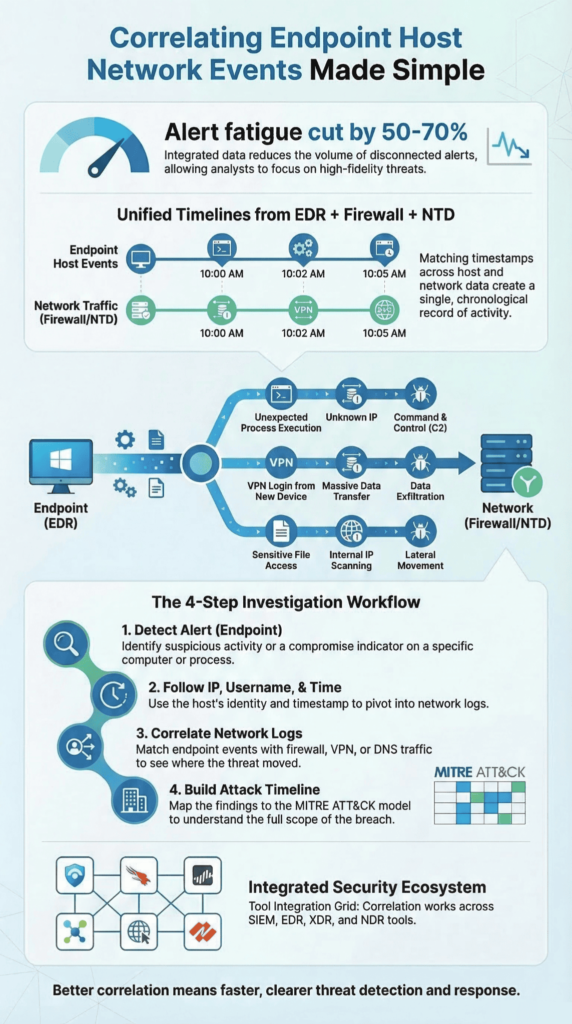
We connect events by lining up timestamps, following identifiers like IPs or usernames, and building a timeline of what the attacker did.
Our workday often starts with a single weird alert. It could be a strange process or a flagged connection.
From there, we chase timestamps. We dig through logs from different systems, looking for events that happened around the same time, usually within five minutes.
Then we pivot. We match computer logs to network traffic using whatever clue we have: a username, an IP address, or a device name. In remote environments, analysts often cross-check endpoint activity with VPN connection logs to confirm whether a session originated from legitimate remote access or a suspicious location.
The basic steps are simple:
- Find that first alert.
- Follow the breadcrumbs, IPs, hostnames, usernames.
- Hunt for more linked connections or process runs.
- Piece together a timeline of what the host did.
With the timeline built, we slot actions into a framework like MITRE ATT&CK. It shows us the attacker’s playbook: how they stuck around or called home.
The result is a clear story of the attack progression, not just random alerts. We can then take action, like isolating a host or collecting a process dump for deeper forensics.
Which Tools and Platforms Enable Endpoint Network Event Correlation?

We use tools like SIEMs, XDR, and network analytics to pull logs together. Automated rules then find attack patterns.
| Platform Type | Example Tools | What It Does |
| SIEM platforms | Microsoft Sentinel | Gathers all logs into one spot and finds links |
| Endpoint detection | CrowdStrike Falcon | Watches what happens on computers |
| XDR platforms | Palo Alto Cortex XDR | Looks for threats across endpoints and networks |
| Network analytics | NDR solutions | Checks network traffic for odd patterns |
These systems pull data from cloud sensors, endpoint agents, firewalls, and identity tools like Active Directory.
In real use, correlation depends on set policies. These rules check incoming event types, decide how serious they are, and send alerts when a limit is hit.
As noted by Vectra AI News
“It then automatically correlates threats against hosts that are under attack and provides unique context about what attackers are doing so organizations can quickly prevent or mitigate loss.” – Vectra AI News
Our typical automation logic includes:
- An alert after three odd events from different sources.
- Rules linking a new file on an endpoint with sudden outbound traffic.
- Cross-checking VPN logs, firewall hits, and endpoint activity.
Many SOC teams put all this data into one analytics platform. This lets analysts see network maps, host behavior, and attack flows on one screen.
For teams building detection now, network threat detection is key. It often spots weird traffic before malware shows up on the computers.
What Challenges Do SOC Teams Face When Correlating Endpoint and Network Events?
Correlation often fails because timestamps don’t match, logs look different, there’s too much data, and rules are tuned badly, making more noise.
One big challenge we see is noisy data. Big companies make a huge number of security logs from endpoints, firewalls, identity systems, and cloud platforms.
An analyst checking a suspicious alert might dig through thousands of log files just to see if it’s a real threat or not.
Common problems we run into:
- Alert fatigue from too many event alerts.
- Timestamp drift between the endpoint and the network systems.
- Logs that look different across various sources.
- Gaps between different security tools.
Another constant issue is rule tuning. Rules that are too strong create false alarms that swamp the team. Rules that are too loose miss small signs of an attack.
Many SOCs deal with this by setting up whitelist policies and snooze periods. These quiet down low-priority alerts for a while.
Analysts also use clear investigation steps and test checks. This makes sure a correlation rule really catches attack behavior.
What Best Practices Improve Endpoint-Network Event Correlation?
Credits: LiveAction Network Performance Software
Good correlation needs logs that look the same, synchronized timestamps, and clear investigation steps that mix endpoint data with network watching.
From our work setting up detection, network threat detection is crucial. It watches how computers talk across the local network and to the outside world all the time.
Two simple things guide many of our checks. First, attackers often move sideways inside a network after they get in. Second, network data usually shows that movement before endpoint alarms go off.
Teams can make correlation better by doing a few things:
- Sync all systems using Network Time Protocol (NTP).
- Make logs from EDR, firewalls, and VPNs look the same.
- Map finds to the MITRE ATT&CK framework.
- Keep host-level details like user info and host profiles.
A typical check for us goes like this:
- Get a starting alert from an Endpoint Detection and Response tool.
- Jump to network logs using the IP address.
- Confirm an outbound connection to a suspected command-and-control domain.
Research from IBM Security says clear steps like this can cut check time by almost half.
More importantly, a strong correlation gives you a wider view across mixed infrastructure. This fits well with modern Zero Trust security models.
FAQ
What causes alert fatigue when correlating endpoint host network events?
Alert fatigue occurs when security teams receive too many alerts from endpoint telemetry, security logs, and network traffic. Many alerts originate from noisy log events or routine endpoint activity.
Correlation rules group related network events, event logs, and endpoint signals into meaningful patterns. This approach reduces unnecessary alerts and highlights suspicious activity, allowing analysts to focus on real adversary activity instead of reviewing harmless events.
How does threat intelligence help correlate endpoint and network events?
Threat intelligence adds context to endpoint telemetry and network detection data. It provides indicators of compromise such as IP addresses, SHA256 hash values, and C2 domain records.
Security systems compare this data with network connections, log files, and endpoint activity. Analysts can then identify patterns more quickly, which supports threat hunting and helps detect lateral movement while reducing attacker dwell time.
Why are Endpoint Detection and Response signals useful for event correlation?
Endpoint Detection and Response collects endpoint signals from endpoint agents installed on operating systems. These agents record process execution details, file creation, PowerShell scripts, and authentication activity.
Analysts combine this information with network traffic and firewall data to build a detailed host timeline. This process helps security teams track suspicious activity across endpoint behavior monitoring and multiple network event sources.
How do correlation rules improve threat hunting in cybersecurity infrastructure?
Correlation rules connect multiple correlation inputs, such as endpoint telemetry, VPN logs, firewall data, and protocol connection events. These rules allow threat hunting teams to identify credential misuse, WMIC calls, and unusual network protocol connection activity.
By linking different event sources across the cybersecurity infrastructure, analysts can clearly observe attack progression and understand adversary activity inside the local network.
What role does network detection play in reducing attacker dwell time?
Network detection systems monitor network traffic, network connections, and VLAN tags across physical and cloud-based environments. When analysts combine this information with endpoint security monitoring and behavioral analytics, they can detect hidden adversary activity.
Security operations teams can then identify lateral movement earlier, reduce attacker dwell time, and respond quickly to incidents while strengthening Zero Trust defenses.
How Endpoint-Network Correlation Improves Threat Detection
Security teams rarely lose because attackers are invisible. They lose because the story is broken apart. One alert shows a login. Another shows odd traffic. Another shows a strange process.
Alone, each event is small. Together, they tell the attack story. When teams link endpoint and network events, they see the path an attacker takes. And once lateral movement starts, every minute matters.
Attackers already think in chains, so defenders must do the same. Connect the signals. Cut the noise. See the threat before it spreads.
If you want a clearer view of how attackers move, you can explore how your team can strengthen detection visibility and see what better correlation looks like in action. Stopping a breach often begins with seeing the full story early.
References
- https://www.researchgate.net/publication/400621470_Improving_Real-Time_Threat_Detection_Accuracy_Using_Correlated_Firewall_IDS_and_Endpoint_Telemetry_Data
- https://www.vectra.ai/about/news/sans-institute-reveals-that-automated-threat-detection-helps-fulfill-protection-goals-of-critical-security-controls


