IoT devices constantly exchange data, perform automated tasks, and connect with networks in ways that may seem routine. However, unusual behavior often signals hidden problems such as malware, unauthorized access, misconfiguration, or hardware failure.
Many organizations collect IoT data but struggle to recognize what activity is normal and what deserves attention. Understanding identifying anomalous IoT device behavior helps security teams turn raw telemetry into early warning signals. Keep reading to learn practical methods for detecting suspicious IoT activity before it escalates.
Key Insights: Identifying Anomalous IoT Device Behavior
Strong anomaly detection starts with understanding normal device patterns and monitoring deviations consistently.
- Baselines help define normal behavior
- Traffic anomalies may indicate compromise
- Authentication failures reveal access abuse
What Is Anomalous IoT Device Behavior?
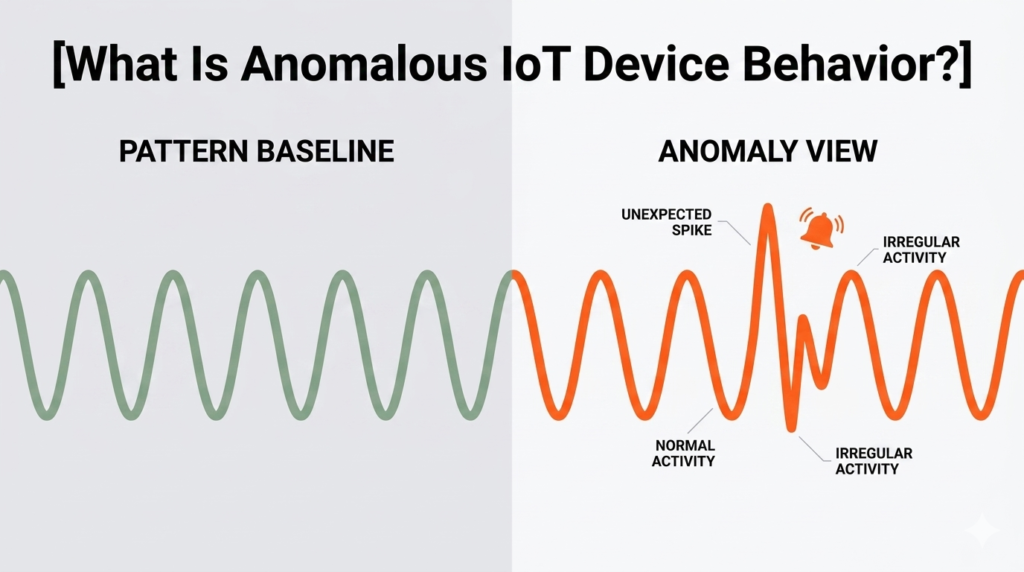
Anomalous behavior means activity that differs significantly from expected patterns for a device, user, or network segment.
Examples include:
- A camera sending traffic at midnight unexpectedly
- A sensor contacting unknown internet servers
- Sudden battery drain without cause
- Repeated failed logins
- Large outbound data transfers
- Frequent device reboots
“Anomaly detection is the identification of rare items, events or observations which raise suspicions.” – Wikipedia
Implementing IoT device security best practices to detect these signals early helps reduce downtime and cyber risk.
Build a Baseline of Normal Activity
Before finding anomalies, teams must know what normal looks like. Each device type may behave differently based on purpose and schedule.
Track baseline metrics such as:
- Average bandwidth usage
- Typical communication times
- Approved destinations
- CPU and memory levels
- Battery consumption trends
- Expected firmware version
Once baselines are established, navigating the security challenges monitoring IoT devices becomes much easier as unusual behavior is identified more accurately.
Monitor Network Traffic Patterns
Credits: Industrial Research Practices
Network telemetry often reveals the first signs of compromise. Unexpected communications can indicate malware or unauthorized control.
Watch for:
- Connections to unknown IP addresses
- Sudden traffic spikes
- Frequent DNS requests
- Port scanning behavior
- Unusual upload activity
- Repeated failed sessions
Traffic analytics is especially useful for devices with limited local logging because the network still records behavior externally.
Detect Authentication and Access Irregularities
Compromised credentials often create unusual login patterns. Monitoring identity events can expose attacks quickly.
Use alerts for:
- Multiple failed login attempts
- New administrator accounts
- Logins from unusual locations
- Access outside business hours
- Disabled account usage
- Password changes without approval
Strong authentication monitoring reduces the time attackers can remain undetected.
Watch Device Health and Performance Changes
Not every anomaly is a cyberattack. Some irregular behavior comes from hardware stress, overheating, or failing components.
Important indicators:
- Repeated unexpected restarts
- CPU spikes without workload changes
- Low memory conditions
- Rapid battery depletion
- Sensor reading instability
- Temperature warnings
“Predictive maintenance uses data analysis tools to detect anomalies.” – Wikipedia
Operational anomalies can still become security risks if ignored.
Use Machine Learning and Behavioral Analytics

Large IoT fleets generate too much data for manual review. Utilizing systems for collecting telemetry data IoT platforms alongside analytics tools helps detect subtle deviations at scale.
Benefits include:
- Faster pattern recognition
- Reduced manual workload
- Prioritized alerts
- Better correlation across devices
- Detection of hidden threats
- Continuous learning models
Machine learning works best when combined with human review and clear response workflows.
Respond Quickly to Confirmed Anomalies
Detection only creates value when paired with action. Build clear incident response steps for IoT events.
Recommended actions:
- Isolate affected device
- Verify logs and traffic history
- Reset credentials
- Update firmware
- Remove malicious connections
- Restore from trusted configuration
Fast containment limits business disruption and prevents lateral movement.
Identifying Anomalous IoT Device Behavior Summary
| Detection Area | What to Watch |
| Network Traffic | Unknown connections, spikes |
| Authentication | Failed logins, odd access times |
| Device Health | Reboots, battery drain |
| Performance | CPU or memory anomalies |
| Behavior Trends | Deviation from baseline |
Common Challenges in IoT Anomaly Detection
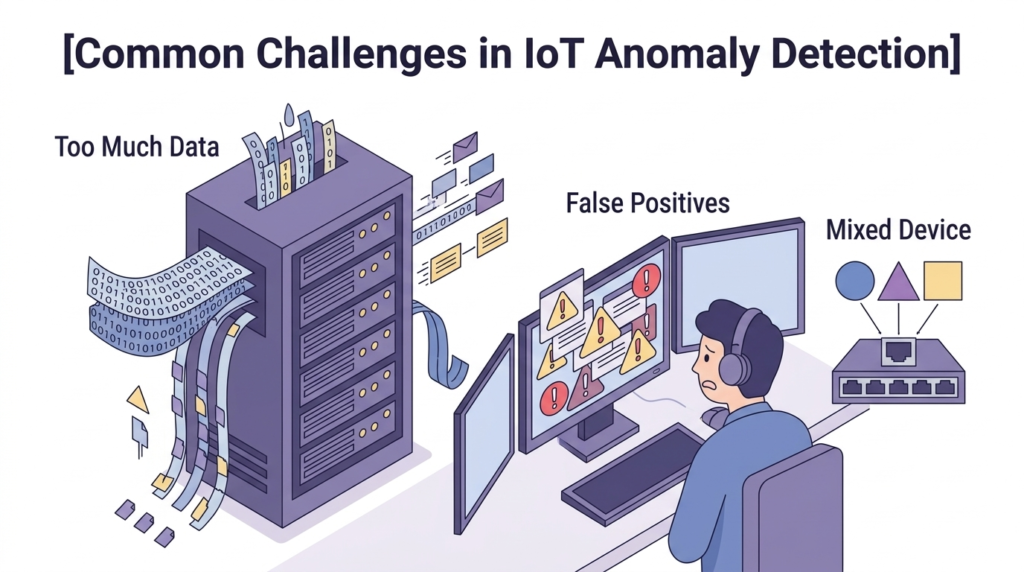
Organizations often face these obstacles:
- Too many alerts
- No baseline data
- Mixed device types
- Limited device logs
- Incomplete asset inventory
Solutions include:
- Tune alert thresholds
- Group devices by category
- Use centralized monitoring
- Maintain updated inventories
- Review incidents regularly
Better processes improve detection quality over time.
FAQ
Why is anomaly detection important for IoT devices?
It helps identify suspicious activity early, including malware, unauthorized access, and operational failures before they cause larger problems.
Can normal maintenance trigger anomaly alerts?
Yes. Firmware updates, reboots, or configuration changes can appear unusual. Good baselines and change records reduce false positives.
What data is most useful for anomaly detection?
Network traffic, login activity, firmware status, device health, and historical usage patterns are among the most valuable data sources.
Is machine learning required for IoT anomaly detection?
No. Basic rules and baselines can provide strong value. Machine learning becomes more useful as device numbers and data volume grow.
Identifying Anomalous IoT Device Behavior for Stronger Security
Mastering identifying anomalous IoT device behavior enables proactive defense. By combining baselines, traffic monitoring, and analytics, teams detect threats sooner.Their platform offers real-time threat modeling, automated risk analysis, and visual attack simulations, backed by frameworks like MITRE ATT&CK.
Streamline vulnerability management and confidently prioritize risks to strengthen your connected environment. Join Network Threat Detection today for a tailored demo.
References
- https://en.wikipedia.org/wiki/Anomaly_detection
- https://en.wikipedia.org/wiki/Predictive_maintenance


