Connected devices now power offices, factories, homes, and healthcare systems. They improve automation, efficiency, and visibility, but they also introduce new security risks when left unmanaged. Weak passwords, outdated firmware, and poor network controls can quickly turn useful devices into entry points for attackers.
Building security into every stage of deployment helps reduce threats and maintain trust. Organizations that act early are better prepared for future risks. Keep reading to learn practical ways to secure IoT device security best practices.
Key Insights: IoT Device Security Best Practices
Strong IoT security starts with simple, repeatable controls. The best results come from combining technical safeguards with ongoing monitoring.
- Replace default credentials immediately
- Update firmware on a schedule
- Segment IoT devices from core networks
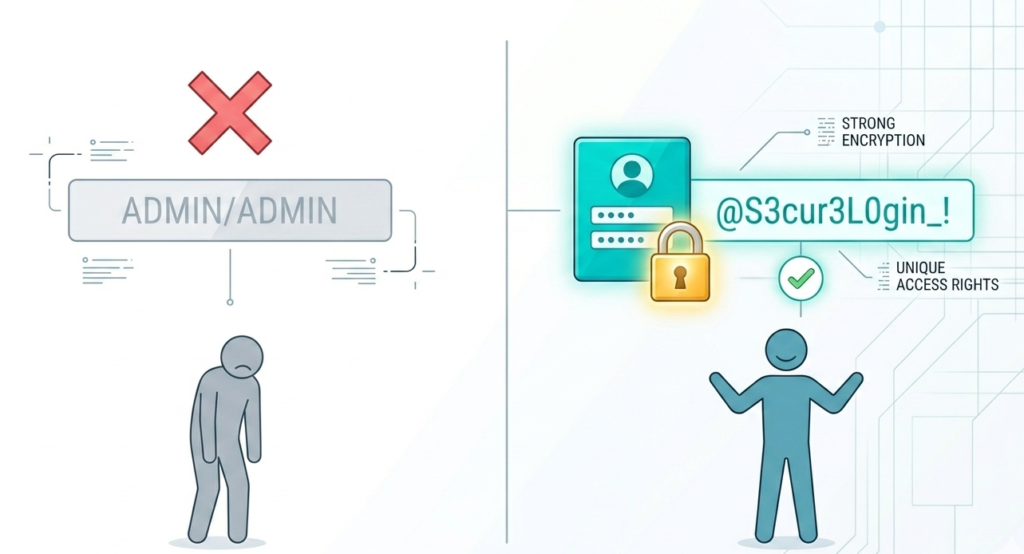
Change Default Credentials and Access Rights
Many IoT devices exchange telemetry, commands, and credentials across networks. When analyzing IoT device telemetry data, unencrypted traffic may be intercepted or altered.
Best actions include:
- Use unique passwords for every device
- Disable unused accounts
- Limit administrator access
- Rotate credentials periodically
- Use password vaults for scale
Least privilege also matters. Only authorized staff should manage devices. Reducing excessive access limits damage if credentials are stolen. Identity discipline remains one of the fastest ways to improve IoT security without expensive upgrades.
Keep Firmware and Software Updated
Outdated firmware leaves devices exposed to known vulnerabilities. Vendors often release fixes that close security gaps and improve stability.
Recommended process:
- Track device models and versions
- Test updates before rollout
- Schedule monthly review cycles
- Replace unsupported devices
- Document completed patches
“Firmware is a specific class of computer software.” – Wikipedia
Because many IoT devices run embedded firmware, patch management should be treated as a core security function. Ignoring updates creates unnecessary long-term risk.
Segment IoT Networks from Business Systems
Credits: Engineering Funda
IoT devices should not operate on the same unrestricted network as finance systems, laptops, or sensitive servers.
Use segmentation methods such as:
- Dedicated VLANs for IoT assets
- Firewall rules between zones
- Restricted east-west traffic
- Guest network separation
- Zero trust access policies
If one smart camera or sensor is compromised, segmentation can help stop movement into critical systems. This containment strategy is especially valuable in factories, healthcare sites, and multi-office environments.
Encrypt Communications and Secure Protocols
Many IoT devices exchange telemetry, commands, and credentials across networks. Unencrypted traffic may be intercepted or altered.
Use protections like:
- TLS for dashboards and APIs
- VPN for remote management
- Certificate-based authentication
- Secure MQTT configurations
- Disabled legacy protocols
“MQTT is a lightweight messaging protocol.” – Wikipedia
Because lightweight protocols are common in IoT, secure configuration is essential. Encryption protects confidentiality while authentication helps ensure only trusted systems can communicate.
Monitor Behavior and Build Visibility

Security does not end after installation. Addressing security challenges monitoring IoT devices helps detect misuse, failures, and suspicious activity early.
Watch for:
- Sudden traffic spikes
- Unexpected external connections
- Repeated login failures
- Devices going offline frequently
- Unknown devices joining networks
Telemetry analysis can reveal patterns humans might miss. Monitoring also improves maintenance planning, making it both a security and operations advantage for connected environments.
IoT Device Security Best Practices Summary
A simple governance model for collecting telemetry data IoT platforms keeps security consistent across growing device fleets.
| Practice | Main Benefit |
| Strong Passwords | Prevent unauthorized access |
| Firmware Updates | Close known vulnerabilities |
| Network Segmentation | Limit breach spread |
| Encryption | Protect data in transit |
| Continuous Monitoring | Detect anomalies early |
Create an IoT Security Lifecycle
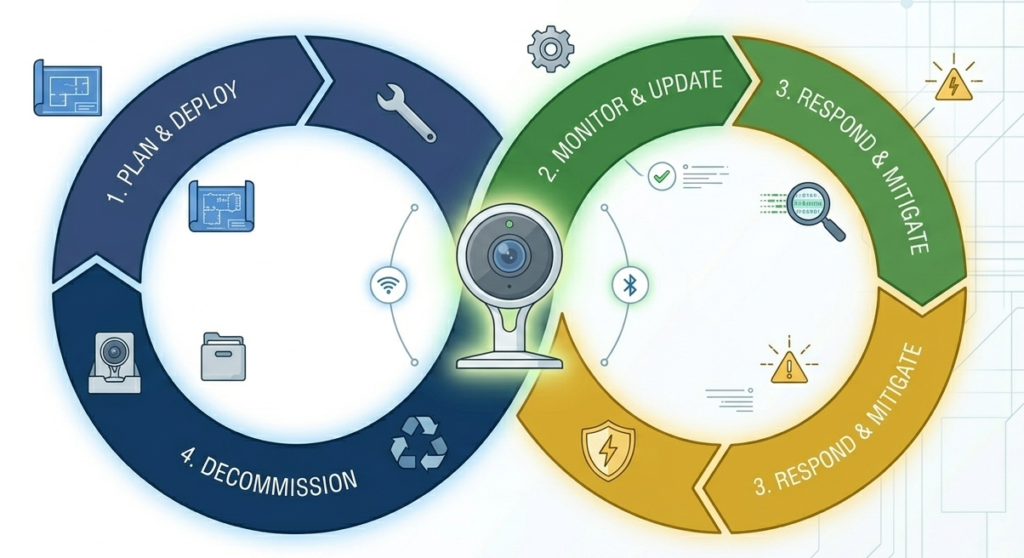
IoT protection should continue through procurement, deployment, maintenance, and retirement.
Lifecycle checklist:
- Buy devices with vendor support
- Configure securely before use
- Review logs regularly
- Patch throughout service life
- Wipe data before disposal
Organizations often focus only on deployment day. A lifecycle approach ensures devices remain secure months or years later, when forgotten assets often become the weakest links.
FAQ
Why are IoT devices considered risky?
IoT devices are often numerous, low-cost, and lightly managed. Many run old firmware, use weak credentials, or lack strong logging features. These factors make them attractive targets if security controls are missing.
How often should IoT devices be updated?
Review updates monthly at minimum, or faster for critical vulnerabilities. High-risk devices exposed to the internet should follow a faster patch cycle with testing and change management.
Is encryption necessary for internal IoT traffic?
Yes. Internal networks are not automatically safe. Encryption helps protect sensitive telemetry, credentials, and commands from interception or tampering inside compromised environments.
What is the first step to better IoT security?
Start with a complete asset inventory. Knowing what devices exist, where they are located, and who owns them enables patching, monitoring, and access control improvements.
IoT Device Security Best Practices for Long-Term Resilience
Establishing long-term resilience requires shifting from a one-time setup to a continuous security posture. By implementing robust passwords, regular updates, network segmentation, and encryption, organizations create a scalable baseline.
To proactively expose blind spots and prioritize risks before attackers do, cybersecurity teams can leverage NetworkThreatDetection.com. Their platform offers real-time threat modeling and automated risk analysis, streamlining vulnerability management for modern connected environments.
References
- https://en.wikipedia.org/wiki/Firmware
- https://en.wikipedia.org/wiki/MQTT


