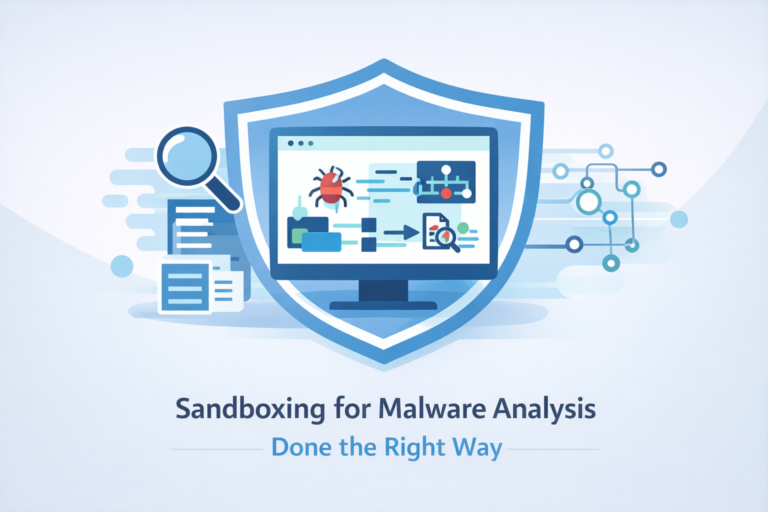
Sandboxing for Malware Analysis Done the Right Way
You can’t judge malware by how it looks, you have to judge it by what it does. Sandboxing…
You can’t judge malware by how it looks, you have to judge it by what it does. Sandboxing…

Visualizing network traffic turns noisy logs into a living map you can actually reason about. Instead of chasing…
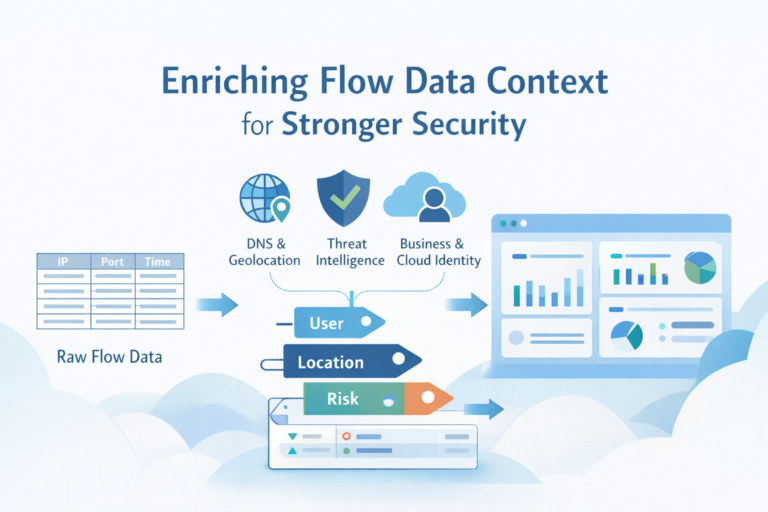
Enriching flow data means turning bare network logs into context-rich records that actually explain what happened, who was…
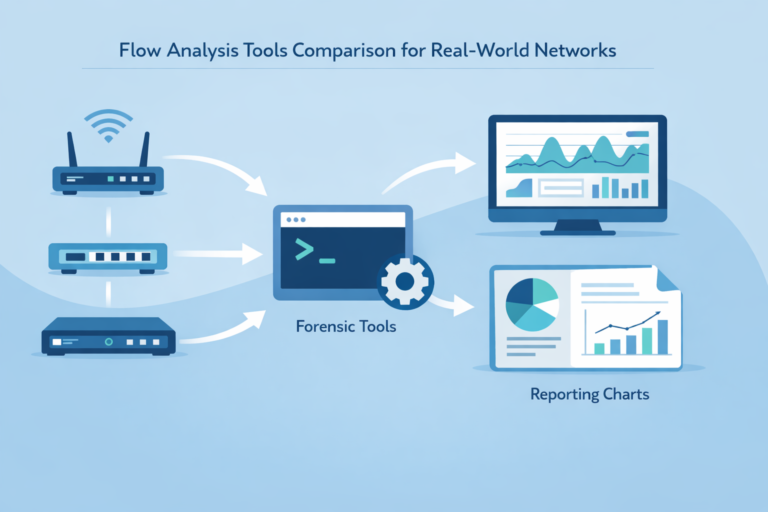
The best flow analysis tool is the one that fits how you actually run your network, not just…

Network reconnaissance is the quiet, early stage of an attack where someone systematically scans your network to discover…

It’s the sound of a thousand drums hitting the same note, at the same time, until your real…