
Google Cloud Platform GCP Logging Explained Simply
Google cloud platform gcp logging brings all your logs into one place. You can see what’s happening across…

Google cloud platform gcp logging brings all your logs into one place. You can see what’s happening across…

Azure monitor activity log analysis helps track who did what, when, and where across your Azure environment. It…
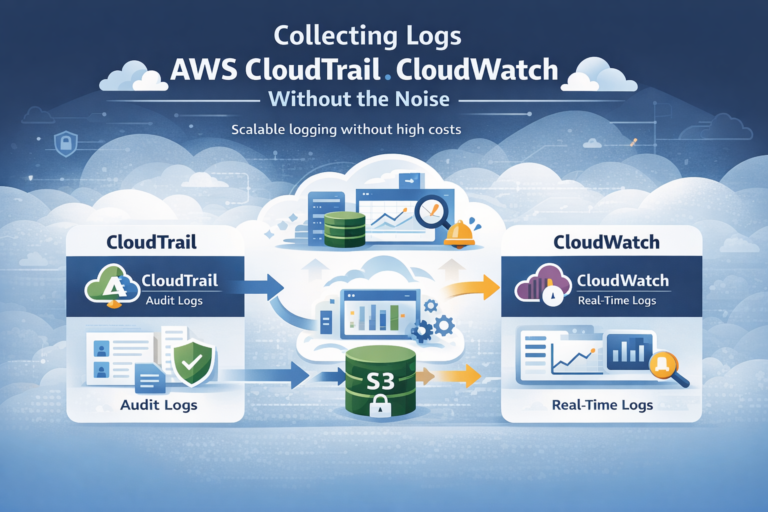
Collecting logs AWS CloudTrail CloudWatch works best when you treat it as a system, not a checkbox. It…

Cloud logs are the activity records from services like AWS, Azure, and Google Cloud. We use them to…

EDR vs traditional antivirus AV differs in scope and capability. EDR goes beyond signature-based blocking by continuously monitoring…

Investigating endpoint compromise EDR requires turning endpoint telemetry into actionable insights to confirm breaches, assess impact, and contain…