
Running an Open Source Log Management ELK Stack
Open source log management ELK stack helps teams centralize logs, investigate failures faster, and monitor environments without jumping…

Open source log management ELK stack helps teams centralize logs, investigate failures faster, and monitor environments without jumping…

Scaling log management infrastructure requires more than adding bigger servers or storing everything forever. Once environments start generating…

Log forwarding protocols Syslog SNMP are the core ways teams move network data into centralized systems. Syslog captures…
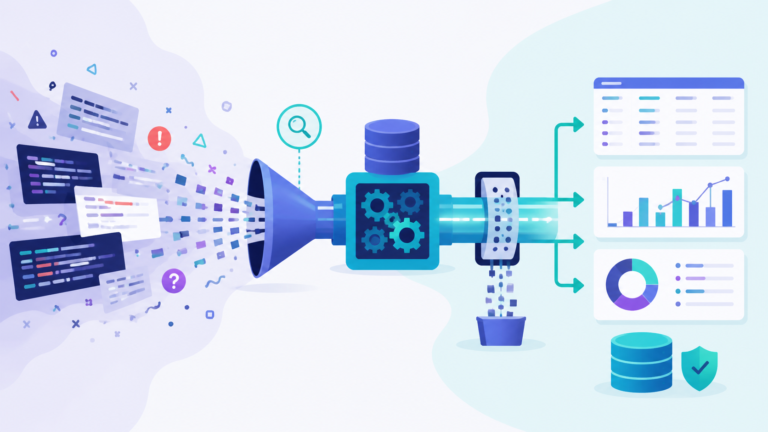
Searching analyzing large log volumes means turning massive machine data into usable insights quickly. At scale, logs can…
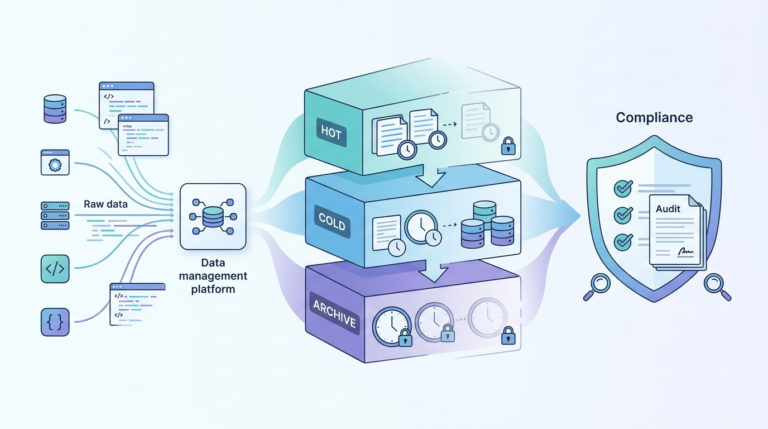
Log storage retention policies compliance defines how long logs are stored, secured, and deleted to meet both legal…
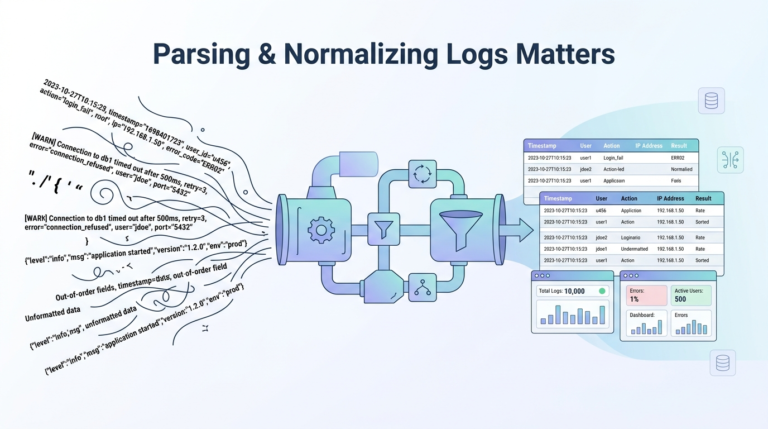
Parsing normalizing log data formats is how raw, messy logs become structured, searchable, and actually useful. Most logs…