Encryption scrambles your words. Everything else, the time, location, and people you message, stays clear. This “metadata” creates a detailed map of your life, often more telling than the conversations themselves.
It’s a silent, ongoing record of your behavior. You can lock the diary, but the record of every time you touch it is left out in the open. So what’s the real risk here, and what are your options? Find out how this unnoticed tracking works and what you can do. Keep reading.
Metadata Privacy Risks at a Glance
- Metadata builds a precise behavioral profile from your digital habits and connections.
- Common file formats embed hidden identifiers like GPS coordinates and device serial numbers.
- Effective protection requires specific tools and a skeptical approach to platform promises.
Why is metadata collection more dangerous than reading your messages?

Metadata tells a story you didn’t realize you were writing. Someone may never read your messages, yet still understand your habits, routines, and relationships just by analyzing patterns. The content is the “what,” but metadata is the context, the “how,” “when,” and “where.”
“Metadata equals surveillance. Imagine you hired a detective to eavesdrop on someone… Now imagine you hired that same detective to surveil that person. The result would be details of what he did: where he went, who he talked to, what he looked at, what he purchased, how he spent his day. That’s all metadata.”- Metadata Equals Surveillance
Encryption can protect the message itself, but metadata still exposes behavioral signals that enable large-scale user profiling and digital privacy concerns, especially when understanding network metadata analysis reveals how patterns across time, devices, and interactions can be reconstructed without reading message content.
- Timestamps and frequency of activity reveal routines and lifestyle patterns
- Geographic location and movement patterns show where you go and when
- Device identifiers and network information link activity across platforms
- Contact lists and social graph connections map relationships and influence
Collected by default and buried in consent terms, this data quietly shapes profiles used for targeting, scoring, and surveillance.
Is the term “metadata” downplaying your actual privacy risks?

Probably. The term sounds technical and harmless, which makes it easy to underestimate. Calling it “data about data” masks what it really represents: a continuous record of your behavior, patterns, and interactions. In modern data harvesting practices, metadata becomes the raw material for prediction, profiling, and behavioral tracking.
“The call records collected by the government are not just metadata, they are intimate portraits of the lives of millions of Americans… metadata is truly ubiquitous, created through the innumerable and near-continuous digital transactions and interactions attendant to modern life.” – why metadata matters
Even so-called anonymized metadata analysis can re-identify individuals when combined with other datasets. Under GDPR and similar frameworks, metadata can qualify as personal data if it can link back to a person.
This terminology trap softens public perception and weakens urgency. In reality, metadata enables passive observation, creating detailed, persistent records that are rarely truly anonymous.
What specific identifiers are hidden in your everyday files?

Everyday files quietly store embedded metadata that can expose personal details without you realizing it. A simple photo, PDF, or document often includes EXIF and system data automatically recorded by devices and software. This can reveal location history, device identity, timelines, and authorship.
Even small files may contain dozens or hundreds of metadata tags, creating a digital trail that can link online activity to a real person and closely resemble how utilizing network metadata session records can reconstruct timelines, device usage, and behavioral patterns.
These hidden identifiers raise serious metadata privacy risks and challenge data minimization principles, especially when files are shared publicly or across platforms.
| Data Point | Common Source File | Privacy Risk |
| GPS Coordinates | Photos, Videos | Reveals exact home, workplace, or routine locations |
| Device Serial Number | Photos, Documents | Links activity to a specific physical device |
| Creation & Modify Dates | All Documents | Builds timelines of behavior and actions |
| Software & OS Version | All Files | Exposes system setup and potential vulnerabilities |
| Author/Creator Name | PDFs, Office Docs | Directly identifies the individual |
Can you actually remove all metadata from your files?
Credits: Kalkine Media
Not completely. You can remove most visible metadata, especially from JPEGs and PNGs, but “all” metadata is a much higher bar. Complex formats like PDFs and RAW images often store layered or structural metadata that isn’t fully removable. Some residual tags may remain embedded in the file architecture.
Even the cleaning process has trade-offs, since uploading files to online tools can create new data exposure. For stronger privacy hygiene:
- Use offline, open-source metadata scrubbers
- Expect some hard-to-remove residual tags in complex files
- Convert files to simpler formats when possible (e.g., screenshot to PNG)
- Verify results with a trusted metadata viewer
In practice, metadata removal is mitigation, not absolute erasure.
Which tools provide the best protection against metadata harvesting?
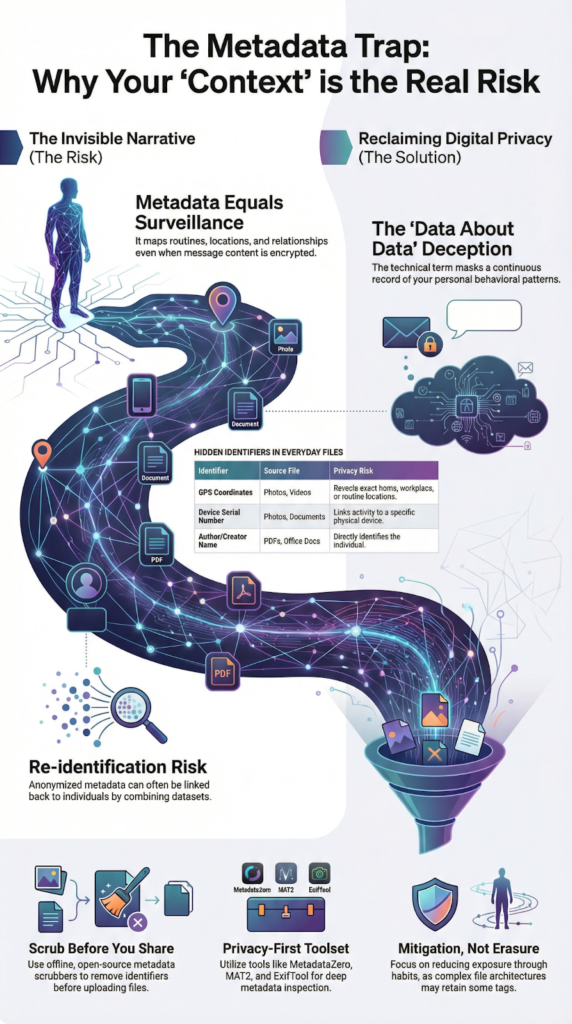
No single tool offers perfect protection, but the best options prioritize offline processing, transparency, and user control. Integrating metadata cleaning into your routine, before sharing files, matters more than relying on platforms to strip data automatically. Tools built with privacy by design help reduce digital footprint tracking and accidental leaks.
- MetadataZero: offline, drag-and-drop batch cleaning with granular control
- MAT2: privacy-focused and actively maintained for Linux users
- Signal: automatically removes metadata from shared media in chats
- ExifTool: highly thorough, industry-standard for deep metadata inspection
Used consistently, these tools reduce exposure, but they work best as part of a habit, not a one-time fix, particularly when considering the broader value of network metadata analysis in profiling behavioral signals and long-term digital footprints.
How do platforms like Reddit and WhatsApp handle your metadata?
Most platforms reduce some visible metadata but still collect extensive behavioral and communication data behind the scenes. Policies vary, and encryption usually protects message content, not the surrounding activity logs. That means timing, interactions, and account behavior are often still tracked for analytics, security, and advertising purposes.
- Social media platforms: may strip EXIF data but log engagement, timing, and connections
- Encrypted messengers: content is protected, yet communication metadata is often retained
- Cloud storage services: frequently keep full metadata unless settings disable location tagging
The key distinction is that private content can remain encrypted while metadata is stored, analyzed, and sometimes shared under legal or policy frameworks, making transparency and user control essential.
FAQ
How serious are metadata privacy risks in daily online activity?
Metadata privacy risks are significant because they expose patterns rather than content. Personal data tracking through timestamps, location data, and device identifiers enables detailed user data profiling. These digital privacy concerns increase when data harvesting practices operate without clear limits or oversight. Over time, even small metadata exposure risks can reveal routines, relationships, and behavioral patterns with surprising accuracy.
How can I improve data collection transparency from services I use?
You can improve data collection transparency by carefully reviewing privacy policy transparency statements and data usage disclosure sections. Look for clear consent for data collection and accessible user consent management controls. Services that follow data transparency standards and responsible data collection practices clearly explain third-party data sharing and data retention policies in specific, understandable terms.
Does anonymized metadata analysis still threaten my privacy?
Anonymized metadata analysis can still threaten privacy when datasets are combined. Behavioral tracking data and digital footprint tracking often allow re-identification, especially when multiple sources are linked. Strong data anonymization techniques and privacy-preserving data methods reduce this risk, but weak metadata privacy safeguards increase data surveillance implications and long-term exposure.
What rights protect me under information privacy laws?
Information privacy laws, including GDPR metadata compliance and CCPA data collection rules, strengthen user privacy rights. These frameworks require lawful data processing, privacy regulation compliance, and documented data governance policies. You have the right to request access, correction, or deletion of personal data, which supports consumer data protection and data privacy accountability.
What practical steps reduce metadata tracking concerns?
You can reduce metadata tracking concerns by applying data minimization principles and choosing services designed with privacy by design standards. Use privacy-aware data processing tools and secure metadata management practices. Conduct regular privacy audit processes and privacy risk evaluation to identify weaknesses. Following data security and privacy best practices strengthens privacy risk mitigation and personal information safeguards.
The Unseen Ledger of Your Life
Metadata creates a parallel biography of you, tracking routines, relationships, and behavior without consent. While laws are catching up, technology moves faster. Don’t dismiss it as “just metadata.” Audit permissions, favor offline-first tools, and clean files before sharing. Digital hygiene is modern risk governance. Take control of your threat visibility and strengthen defenses proactively. Join Network Threat Detection
References
- https://www.schneier.com/blog/archives/2013/09/metadata_equals.html
- https://www.eff.org/deeplinks/2014/11/klayman-v-obama-eff-explains-why-metadata-matters-and-third-party-doctrine-doesnt


