
Identifying Communication Patterns Metadata: Methods and Risks
Communication patterns metadata captures non-content signals such as timestamps, sender and receiver IDs, IP addresses, and message frequency…

Communication patterns metadata captures non-content signals such as timestamps, sender and receiver IDs, IP addresses, and message frequency…

Connection logs provide critical insight into network traffic, intrusion attempts, and system performance by analyzing structured metadata like…

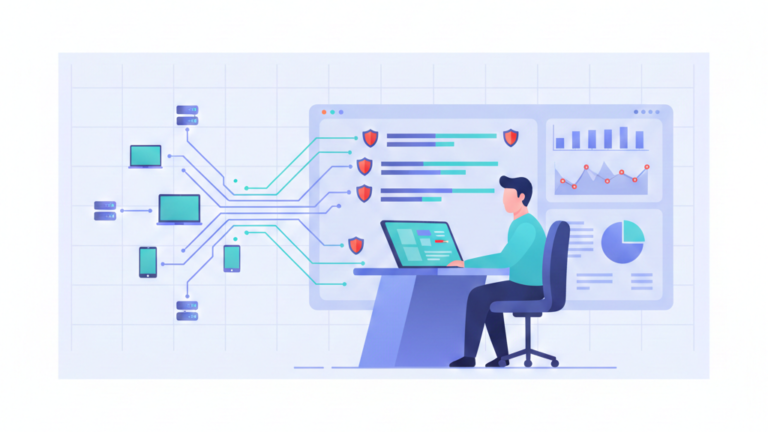
Metadata vs full packet capture serve complementary roles in network security. Metadata enables scalable monitoring, letting teams track…

Generating session data from traffic turns raw packets into structured, analyzable metadata by reconstructing full communication sessions using…
The value of network metadata analysis improves threat detection, accelerates incident response, and preserves privacy by focusing on…
Understanding network metadata analysis is the best way to spot intruders first. You examine the basic facts of…