In modern infrastructure, logs are the backbone of visibility. Understanding Syslog Protocol And Configuration helps organizations track events, detect anomalies, and maintain operational integrity. From our experience, many teams underestimate how crucial structured logging is until incidents occur.
When logs are properly configured, they become a powerful asset for troubleshooting and security monitoring. In this guide, we break down key concepts, configurations, and real-world challenges. Keep reading to learn how to optimize syslog for performance, security, and scalability.
Key Insights On Understanding Syslog Protocol And Configuration
A quick overview before diving deeper:
- Syslog provides standardized logging across devices
- Severity levels help prioritize incidents
- Centralized logging improves visibility
Syslog Ng Vs Rsyslog Comparison
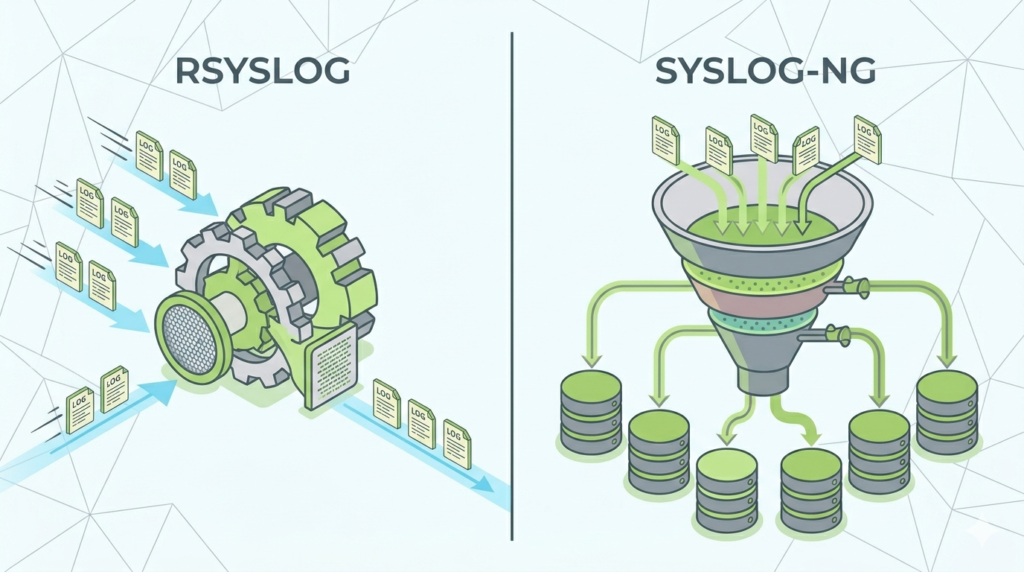
When comparing syslog ng vs rsyslog comparison, both offer flexibility, but their strengths differ:
| Feature | syslog-ng | rsyslog |
| Performance | High throughput | Highly optimized |
| Configuration | More readable | More modular |
| Extensibility | Strong parsing | Strong plugin ecosystem |
| Community Use | Moderate | Widely adopted |
From our deployments, rsyslog often fits traditional environments, while syslog-ng shines in complex parsing scenarios.
Syslog Message Format Severity Levels
Syslog messages follow a structured format including timestamp, hostname, and severity. The syslog message format severity levels range from:
- Emergency (0): System unusable
- Alert (1): Immediate action required
- Critical (2): Critical conditions
- Error (3): Error events
- Warning (4): Warning conditions
- Notice (5): Normal but significant
- Informational (6): General info
- Debug (7): Detailed debugging
“Syslog defines a standard for message logging that allows separation of facility and severity.” – Wikipedia
Understanding severity helps teams prioritize responses effectively.
Configuring Devices Send Syslog Messages
Credits: ChipTask
Configuring devices send syslog messages involves enabling logging and defining a destination server.
Typical steps include:
- Enable syslog feature on device
- Define syslog server IP
- Set severity threshold
- Choose transport protocol (UDP/TCP)
We’ve seen misconfigurations cause silent failures, especially when ports or severity levels mismatch.
Setting Up Central Syslog Server
A central syslog server aggregates logs from multiple sources into one location.
Key setup steps:
- Install syslog service
- Configure input listeners
- Define storage paths
- Enable log rotation
Centralization improves visibility and supports Network Threat Detection by correlating events across systems.
Securing Syslog Communication TLS
Securing syslog communication TLS is essential for protecting sensitive log data.
Benefits include:
- Encryption of log transmission
- Prevention of tampering
- Authentication of sources
“Transport Layer Security (TLS) ensures privacy between communicating applications.” – Wikipedia
From experience, unencrypted syslog is a common weak point.
Challenges Managing Syslog Data Volume
One major issue is the sheer volume of logs generated.
Common challenges managing syslog:
- Storage overload
- Performance degradation
- Difficulty in analysis
We’ve handled environments where logs reached terabytes daily.
Parsing Unstructured Syslog Messages
Parsing unstructured syslog messages transforms raw logs into usable data.
Approaches include:
- Regex-based parsing
- Structured templates
- Log normalization
Proper parsing enables better analytics and supports automated detection workflows.
Filtering Syslog Messages Effectively
Filtering syslog messages effectively reduces noise and focuses on relevant events.
Best practices:
- Filter by severity
- Filter by source device
- Exclude repetitive logs
- Prioritize security events
Filtering ensures teams respond faster to real issues.
High Availability Syslog Setup
A high availability syslog setup ensures continuous logging even during failures.
Key strategies:
- Redundant servers
- Load balancing
- Failover mechanisms
High availability prevents data loss and maintains monitoring continuity.
Storing Syslog Data Efficiently

Efficient storage is critical for long-term log management.
Options include:
- Compressed storage
- Tiered storage systems
- Retention policies
Efficient storage balances cost and accessibility.
FAQ
What Is The Main Purpose Of Syslog In Modern Systems?
Syslog standardizes log collection across devices, enabling monitoring, troubleshooting, and security analysis. It helps organizations detect anomalies and maintain operational awareness.
Why Are Severity Levels Important In Syslog?
Severity levels prioritize responses by categorizing logs based on urgency. This allows teams to focus on critical issues first and avoid overload from less important messages.
How Does TLS Improve Syslog Security?
TLS encrypts log data during transmission and ensures authenticity of sources. This prevents interception and protects the integrity of logging systems.
What Are The Biggest Challenges In Managing Syslog Systems?
The main challenges include handling massive log volumes, parsing unstructured data, and maintaining performance. Proper architecture and filtering are essential to overcome these issues.
Final Insight On Understanding Syslog Protocol And Configuration
Understanding Syslog Protocol And Configuration is essential for building reliable and secure logging systems. From configuring devices to securing communication and managing data volume, each step plays a role in operational success.
In our experience, combining structured logging with Network Threat Detection creates stronger visibility and faster response capabilities. Start improving your syslog strategy today and integrate it with smarter Network Threat Detection to strengthen your security posture.
References
- https://en.wikipedia.org/wiki/Syslog
- https://en.wikipedia.org/wiki/Transport_Layer_Security
Related Articles
- https://networkthreatdetection.com/syslog-ng-vs-rsyslog-comparison/
- https://networkthreatdetection.com/syslog-message-format-severity-levels/
- https://networkthreatdetection.com/configuring-devices-send-syslog-messages/
- https://networkthreatdetection.com/setting-up-central-syslog-server/
- https://networkthreatdetection.com/securing-syslog-communication-tls/
- https://networkthreatdetection.com/challenges-managing-syslog-data-volume/
- https://networkthreatdetection.com/parsing-unstructured-syslog-messages/
- https://networkthreatdetection.com/filtering-syslog-messages-effectively/
- https://networkthreatdetection.com/high-availability-syslog-setup/
- https://networkthreatdetection.com/storing-syslog-data-efficiently/


